
We all know that there's a problem with passwords. Most internet users are careless when choosing passwords - either re-using the same passwords they've used elsewhere or making them too easy to crack. And if they're not guilty of that mistake, there's always the chance that their computers are infected with spyware watching their keystrokes and stealing their login credentials that way. This is, obviously, a concern for many sites (such as online banks) which would feel happier having a greater level of confidence that the person who has logged in really is who they say they are. One of the ways in which some online services combat this concern is the use of two-factor authentication, perhaps demanding that the user enters a random number which has appeared on a keyfob as well as a password. The thinking is that a hacker may have succeeded in grabbing your password, but are they likely to have physical possession of the device displaying the random PIN as well. But authentication can go further than that, not just checking what you know (your password), and what you have (your PIN), and moving towards what you are (biometric solutions such as the iPhone's TouchID). One intriguing behavioural biometric is "how you type" or keyboard behaviour biometrics. People, it turns out, type differently. The differences may be largely imperceptible to the human eye, but a computer can tell different typists apart by monitoring how you type: for instance, how long you take between each keypress, the length of time you take pressing each key, how long it may take you to type a particular string of characters, and so forth... Many of these measurements are impossible for our puny human brains to handle, but a computer can measure them in terms of milliseconds.
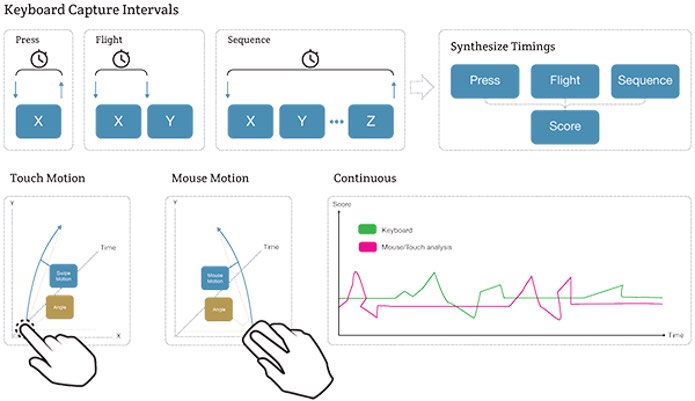
Image courtesy of BehavioSec Neat, eh? Well, if you're talking about this from the security point of view then yes, it does sound cool. Several online banks, for instance, appear to have been doing keyboard behaviour biometrics for some time - as part of their fight against fraudsters. And that sounds good. But what about keyboard behaviour biometrics being used to breach privacy? If a website can examine how you type, and identify with a high level of confidence who you are based upon the length of your keypresses and the gaps between them, then it's easy to imagine how this information might be abused. Even if you were using a service like Tor to cover your tracks on the net, and disguise your identity online, it could be that your typing style on a particular website could reveal your true identity to someone who was keen to know it. With that concern in mind, security researchers Paul Moore and Per Thorsheim have teamed up to develop and test a tool which can take a person's regular keyboard interaction with a website, and meddle with its characteristics that are imperceptible to humans, but utterly outfox any website attempting to identify the user. Moore and Thorsheim have released KeyboardPrivacy, a Chrome extension that can make your typing look like it is being made by someone entirely different. Check out this YouTube video where Per Thorsheim visits a website which demonstrates keyboard behaviour biometrics working successfully, and how it can then be outwitted by the KeyboardPrivacy plugin. In a blog post announcing KeyboardPrivacy, Paul Moore explains the intention is not to stop all websites from attempting to use keyboard behaviour biometrics as a means of authentication:
As I mentioned earlier, it's more important to strike a good balance between security & privacy; it's rarely possible to increase one without measurably degrading the other (password managers being an exception). If you're happy to leak this information to every site, or if you're forced to do so by a financial institution, you can disable the plugin on a per-site basis. Even if your behavioral profile is leaked to a 3rd-party, it's of no use unless you happen to disable it on their site too. The single biggest problem with passwords is not length or strength, but re-use. Your behavioral biometrics (knowingly or not) are essentially secrets which you unwittingly share with every site.
I'll be interested to see what the next steps are for the KeyboardPrivacy extension, and other tools that may bubble up to protect our privacy online from those examining our keyboard behaviour. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

