
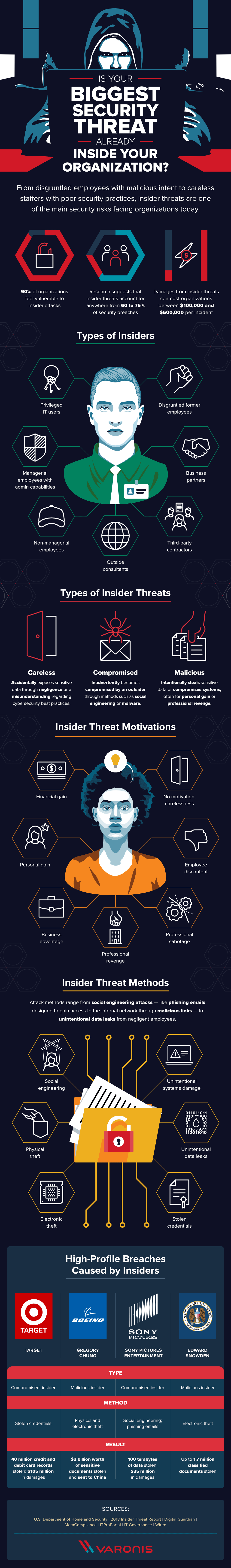
While stories of international espionage and government-sponsored hack attacks may captivate public attention, cyber security threats that originate from inside an organization pose a remarkably large threat. In fact, research suggests that insider threats account for anywhere from 60 to 75 percent of data breaches. Insider threats can range from the malicious, such as disgruntled ex-employees bent on professional revenge, to unintentional, such as current employees who aren’t trained in the best cybersecurity practices. This wide range of motivations and methods makes insider breaches hard to detect and difficult to stop. So, what should you be on the lookout for? To answer this question, Varonis took a look at the different types of insider threats, where they come from, and the methods they use. Take a look at their full infographic below to learn more about what threats may already be in your organization.

About the Author: Rob Sobers is a Sr. Director at cybersecurity firm Varonis. He has been writing and designing software for over 20 years and is co-author of the book "Learn Ruby the Hard Way," which has been used by millions of students to learn the Ruby programming language. Prior to joining Varonis in 2011, Rob held a variety of roles in engineering, design, and professional services. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.

