A digital security strategy embodies every organization's efforts to protect its industrial control systems (ICS) against intentional and accidental security threats. Lots of different factors shape this plan. As I discussed in a previous article, organizations should conduct regular industrial digital security assessments to identify what frameworks and standards apply to them, as well as prioritize gaps for action in their security strategies. I also emphasized the importance of blending a risk-based approach to industrial digital security with defense-in-depth elements. Now that we know the overall purpose of an ICS security strategy, here are a few recommendations for what such a plan should do in practice:
- A digital security strategy should use the first five CIS Critical Security Controls. As such, it should help organizations inventory all authorized and unauthorized hardware and software with an emphasis on prioritizing critical business assets for protection; secure and harden configurations of industrial networks, endpoints, and control systems; continuously assess for and remediate vulnerabilities; and control use of administrative privileges.
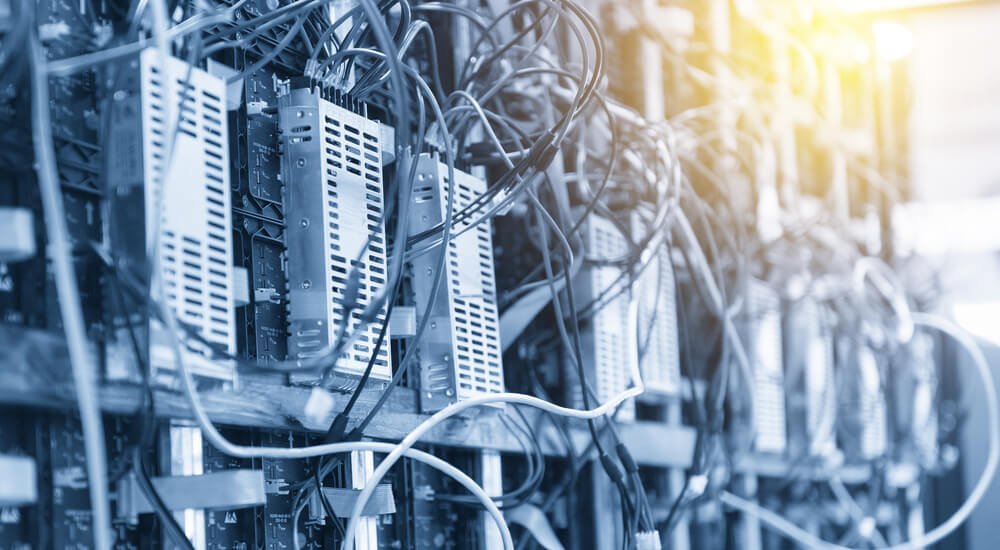
- Organizations should secure all network and web connections to control systems. This connectivity creates problems that often overshadow the benefits it provides. As such, companies should minimize and eliminate this connectivity wherever possible. They should also secure wireless and remote access as well as minimize who has authorization to use it.
- Strong authentication goes a long way towards protecting systems against digital attacks. As a result, organizations should incorporate measures that implement robust authentication in their industrial environments. These features should not only accept complex and unique passwords but should also require additional components like two-factor authentication.
By themselves, the elements discussed above will help strengthen an organization's industrial security posture. But companies can do even more to protect themselves and their ICS systems against digital threats. In their e-book entitled Industrial Cyber Security for Dummies, Tripwire and its parent company Belden recommend that organizations formalize their ICS security strategies by writing them into their security policies. They can then use those policies to not only monitor for network changes but to also increase security awareness via employee training exercises. In addition, these policies can enumerate companies' implementation of defense-in-depth layers such as network segmentation, creation of zones, logging, and access control. For more information about what elements your organization's ICS security strategy should incorporate, please download Tripwire and Belden's resource here.
Tripwire Enterprise: Security Configuration Management (SCM) Software
Enhance your organization's cybersecurity with Tripwire Enterprise! Explore our advanced security and compliance management solution now to protect your valuable assets and data.

