
Security researchers reversed the encryption routine employed by L4NC34 ransomware by decrypting a file without paying the ransom. Sucuri Security first encountered L4NC34 ransomware when it began investigating an attack in which a malicious actor encrypted all website files and appended ".crypt" to their file names. The security firm dug a bit deeper and uncovered something interesting. As it explained in its research:
Among the files we also found the ransom note you might typically find in this type of malware, but this one was a bit unusual — It wasn’t an HTML or a .txt file. Instead, the ransom note was actually located within a PHP file and seemed to contain actual functions.
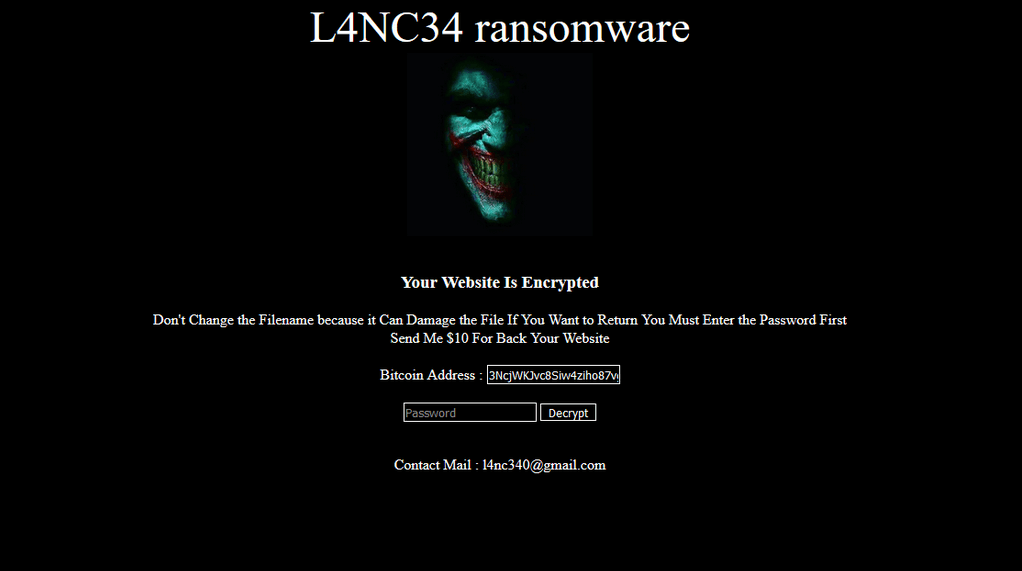
L4NC34's ransom note. It demands $10 in exchange for the restoration of a victim's website. (Source: Sucuri Security) Upon examining the malicious PHP file, Sucuri noticed that it was base64 encoded. Its researchers responded by decoding the file. Their efforts revealed portions of code that were responsible for displaying the ransom note and for completing decryption after receiving a password. This latter snippet revealed that L4NC34 had not actually "encrypted" the victim organization's data. Instead, it had used the "gzdeflate" function to alter the data. The threat followed up by changing the modified files' names. Using that knowledge, Sucuri found that it could run the decryption process through the terminal or the browser and successfully recover a file without a victim needing to pay the $10 ransom fee. No one had transferred funds to the bitcoin account associated with L4NC34 at the time discovery. Even though researchers were able to easily reverse L4NC34's encryption routine, the same cannot be said about other ransomware families. This explains why organizations need to take steps to protect themselves against a crypto-malware attack. One of the ways they can do this is by preventing a ransomware infection in the first place using these tips.

