
PC manufacturer Lenovo has been forced to push out a security update to more than two dozen of its laptop models, following the discovery of high severity vulnerabilities that could be exploited by malicious hackers.
Security researchers at ESET discovered flaws in 25 of its laptop models - including IdeaPads, Slims, and ThinkBooks - that could be used to disable the UEFI Secure Boot process. That matters because Secure Boot, as its name suggests, is a feature that allows a PC's firmware to be "locked down" as a defence against rootkits, ensuring that only trusted cryptographically-signed code can be run at bootup.
A vulnerability in the laptops' Secure Boot process could open opportunities for cybercriminals to install malicious firmware onto a device that would survive a hard drive being wiped or an operating system being reinstalled.
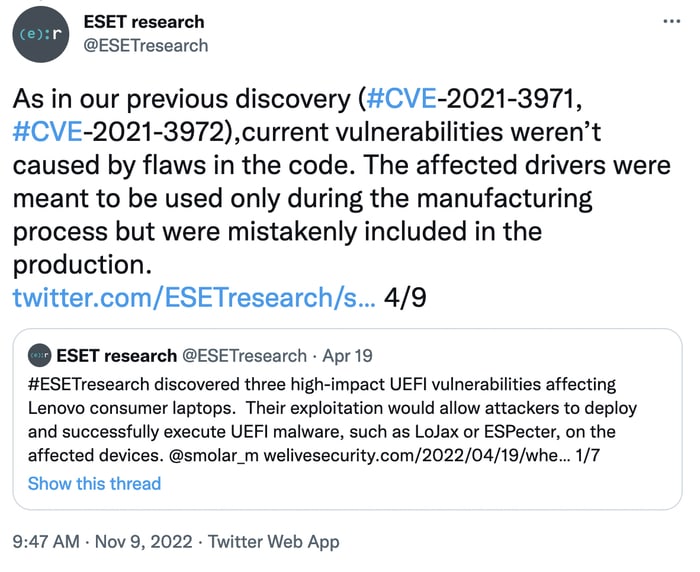
According to ESET, the vulnerabilities are present because Lenovo mistakenly shipped to the public drivers that were only supposed to have been used during the manufacturing process.
Lenovo acknowledged that it was to blame for shipping the laptops in a vulnerable state:
“A potential vulnerability in a driver used during manufacturing process on some consumer Lenovo Notebook devices that was mistakenly not deactivated may allow an attacker with elevated privileges to modify secure boot setting by modifying an NVRAM variable.”
ESET's research team disclosed similar high-impact UEFI vulnerabilities on Lenovo laptops back in April. Lenovo has issued firmware updates for two of the latest vulnerabilities - which have been given the names CVE-2022-3430 and CVE-2022-3431. However, the third vulnerability - CVE-2022-3432 - has been left unpatched as it only affects the Lenovo Ideapad Y700-14ISK.
Lenovo says that as that particular laptop is no longer supported by the company, it will not be receiving a fix. Owners of Lenovo laptops can check if their particular models are impacted by the vulnerabilities by consulting the list the company shares in its security advisory.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

