
Despite retailers’ continuous improvement in compliance with the Payment Card Industry (PCI) security standards, four out of five companies are still failing at interim assessments, according to Verizon’s latest report.
The report highlights that the overall state of compliance grew significantly in 2014, with 20 percent of organizations achieving full compliance – up from 11 percent in 2013, and only 7.5 percent in 2012. Nonetheless, the findings show there’s much room for growth.
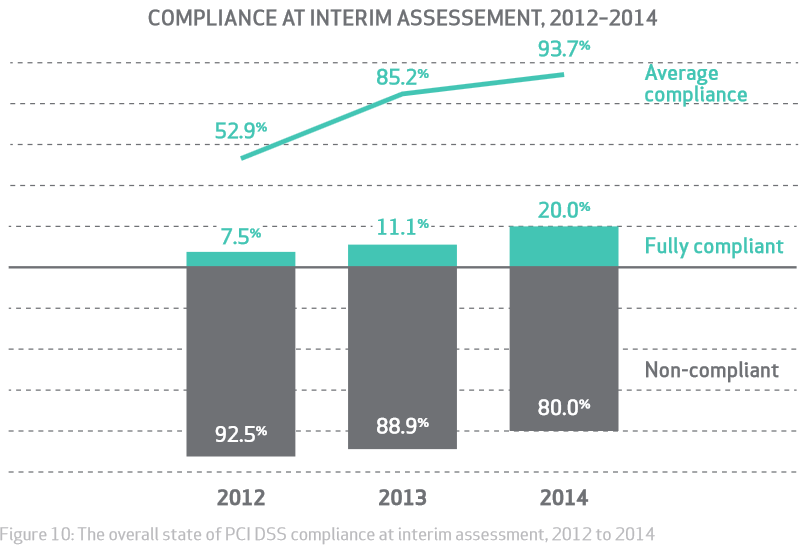
Source: Verizon 2015 PCI Compliance Report Additionally, the 2015 report states the average increase in compliance per requirement was 18 percentage points. Eleven of the twelve requirements increased in average compliance, with the exception of Requirement 5, which dropped four percentage points. Furthermore, the study also found that the most difficult requirement for companies to comply with was Requirement 11 – obliging companies to perform regular and frequent vulnerability scans to search for unaddressed security issues, scan for rogue wireless networks, carry out file integrity monitoring to identify unauthorized system changes, and implement intrusion detection systems to search for indicators of compromise. “Requirement 11 is fundamental to ensuring that the organization is prepared for the range of attack types reported in the 2014 DBIR,” read the report.
“During post breach investigations, we found that just 9% of organizations were compliant with this requirement.”
Tripwire Senior Product Marketing Manager Katherine Brocklehurst adds these results are not surprising. "The PCI DSS 3.0 is significantly more challenging than PCI 2.0 was, and a lot of the past methods – or loopholes – of reducing scope used by organizations have been eliminated," said Brocklehurst. Verizon’s research is based on data gathered from more than 5,000 merchants in 30 countries, including Fortune 500 companies and large multinationals in the retail, healthcare and hospitality sector. “Since 2009, our research for the PCI Compliance and Data Breach Investigations Reports has shown a strong correlation between compliance and data protection,” the report said. “While compliance is no guarantee that you won’t be breached, it should reduce the likelihood — that’s why the PCI DSS exists.”
Insider Insights for the PCI DSS 4.0 Transition
Gain valuable insights from cybersecurity experts on transitioning to PCI DSS 4.0. Tripwire's comprehensive guide provides strategic advice, making the compliance process more streamlined and efficient. Understand the challenges and solutions for meeting PCI DSS requirements with expert guidance.

