
The Bizarro Sundown exploit kit is spreading two versions of Locky ransomware via the still-active ShadowGate malvertising campaign. In October, Trend Micro spotted two versions of Bizarro Sundown, a modification of the earlier Sundown exploit kit which rose to prominence with RIG following Neutrino's demise. The first iteration reared its ugly head at the beginning of the month to scan users' computers for three vulnerabilities: one memory corruption bug in Internet Explorer and two security holes in Adobe Flash Player. That version shared some similarities with Sundown in how it redirected targets to websites hosting malware. But it did make an effort to distinguish itself. Trend Micro threat analysts Brooks Li and Joseph C. Chen explain:
"The first Bizarro Sundown attacks shared a similar URL format as Sundown. However, it obfuscates its landing pages differently, without using a query string. Bizarro Sundown also added anti-crawling functionality. An increasingly common feature found in exploit kits today, anti-crawling functions are designed to defeat automated crawlers used by researchers and analysts. It was used to deliver a Locky variant which appended the .odin extension for encrypted files."
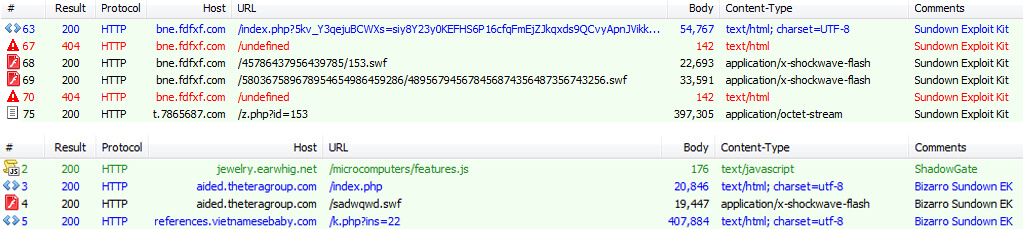
Traffic of Sundown (above) and Bizarro Sundown (below) exploit kits (Source: Trend Micro) First detected in late-September 2016, the .odin file virus is one of several of Locky's variants that have surfaced in the past few months. Those include .zepto in July 2016 and one other variant in October. Bizarro Sundown's second version emerged in mid-October. Aside from dropping the IE exploit, it began using a malicious Flash (.SWF file) to determine the Flash Player version installed on each victim's computer.
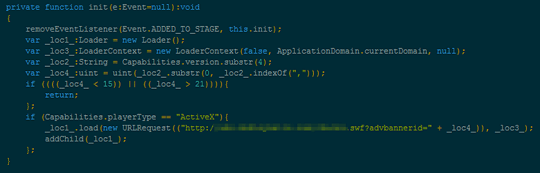
Part of code that determines the version of Flash Player installed on the system (Source: Trend Micro) It then used this information to deliver the appropriate Flash exploit, a technique which effectively removed landing pages from its distribution campaign of the .thor Locky variant. Both exploit kits operated through ShadowGate. Researchers at Cisco Talos reportedly took down the malvertising campaign that targeted multiple open-source advertising servers back in September 2016. But that's not what Li and Chen found:
"While the campaign was reportedly shut down in September this year, we found that it’s still alive and well, using 181 compromised sites to deliver ransomware. In September we saw ShadowGate using the Neutrino exploit kit to drop a variant of Locky (with the encrypted files having the .zepto extension). On October 5, the campaign shifted to Bizarro Sundown. Two weeks later (October 19), a modified version of Bizarro Sundown was spotted."
To protect against both versions of Bizarro Sundown, users should make sure they keep their software and operating systems up-to-date. They should also develop a data backup plan just in case they experience a ransomware infection. To learn more about ransomware, please click here.

