
Researchers believe the BlackEnergy group launched malware attacks against the Ukrainian financial sector in the second half of 2016. ESET malware researcher Anton Cherepanov says the malware attacks started off with spear-phishing emails. Attached to the messages were Microsoft Excel documents containing malicious macros as an initial infection vector. Curiously, the emails didn't make use of social engineering, which suggests the attackers believed pure curiosity would motivate recipients to fall for the ruse.
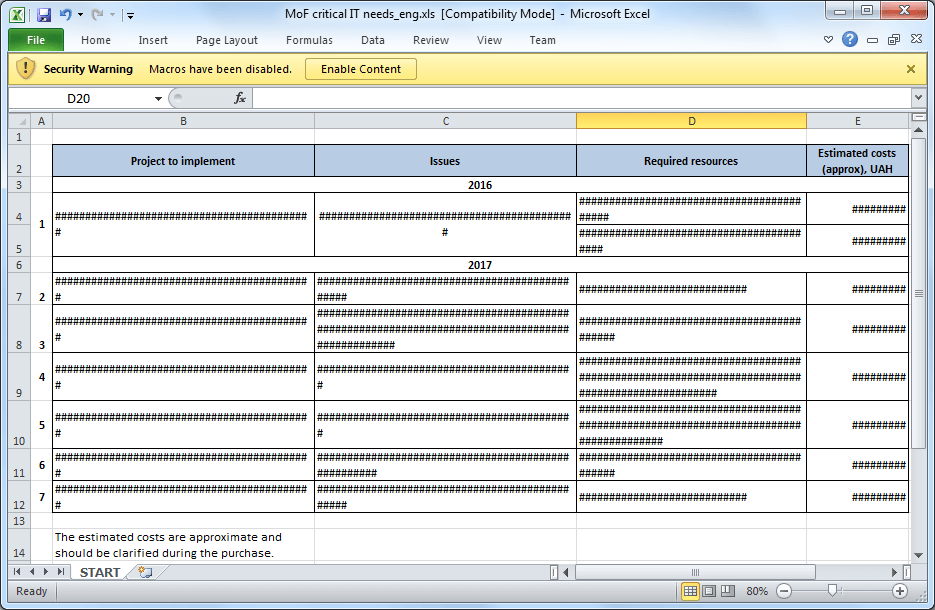
One example of a malicious XLS document from the campaign. (Source: ESET) Enabling content caused the malicious macro to execute and drop a malicious binary that in turn downloaded the final payload: a Python-written backdoor detected as Python/TeleBot.AA trojan. Cherepanov observes the TeleBots backdoor shares some striking similarities with GCat, another Python backdoor developed by a group who conducted malware attacks in January 2016. As he explains in a blog post:
"The Python/TeleBot malware uses exactly the same approach; the Python backdoor code is obfuscated and packed into a standalone executable using PyInstaller. In addition, the Python code is ROT13 encoded, AES encrypted, compressed using zlib library and then Base64 encoded."
Those behind the January attacks used the same mail server as the BlackEnergy group in late 2015, meaning the two threat actors could be one in the same. It's possible. After all, the malicious macro code used by TeleBots and BlackEnergy is itself similar.
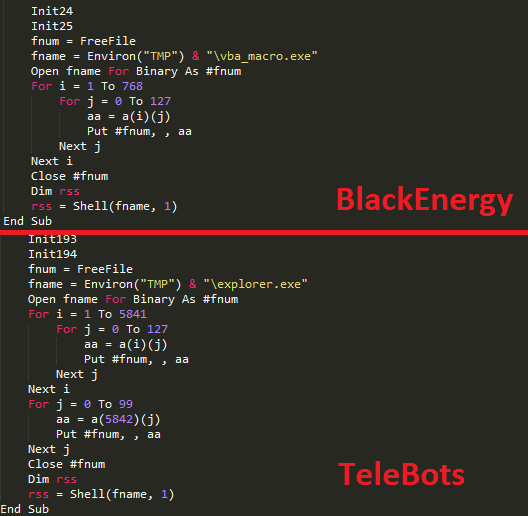
Similarities between malicious macro code used by BlackEnergy and TeleBots. (Source: ESET) Like TeleCrypt ransomware, TeleBots uses the public API of the Telegram messaging app to communicate with the attackers and to download other malicious tools onto an infected computer. In this campaign, TeleBots dropped a tool called "CredRaptor" that collects saved passwords from web browsers and another called "plainpwd" that dumps Windows credentials. The malware also came with a keylogger, a console version of Interceptor-NG for sniffing passwords in network traffic, a LDAP query tool used for dumping information about computers and usernames listed in Active Directory, and additional fail-safe backdoors that allowed the attackers to access the network even if admins discovered and shut down TeleBot. Each successful attack ended with KillDisk, malware which deletes important files, overwrites others, and makes the computer unbootable. The attackers also programmed KillDisk to draw an image inspired by the television show Mr. Robot.
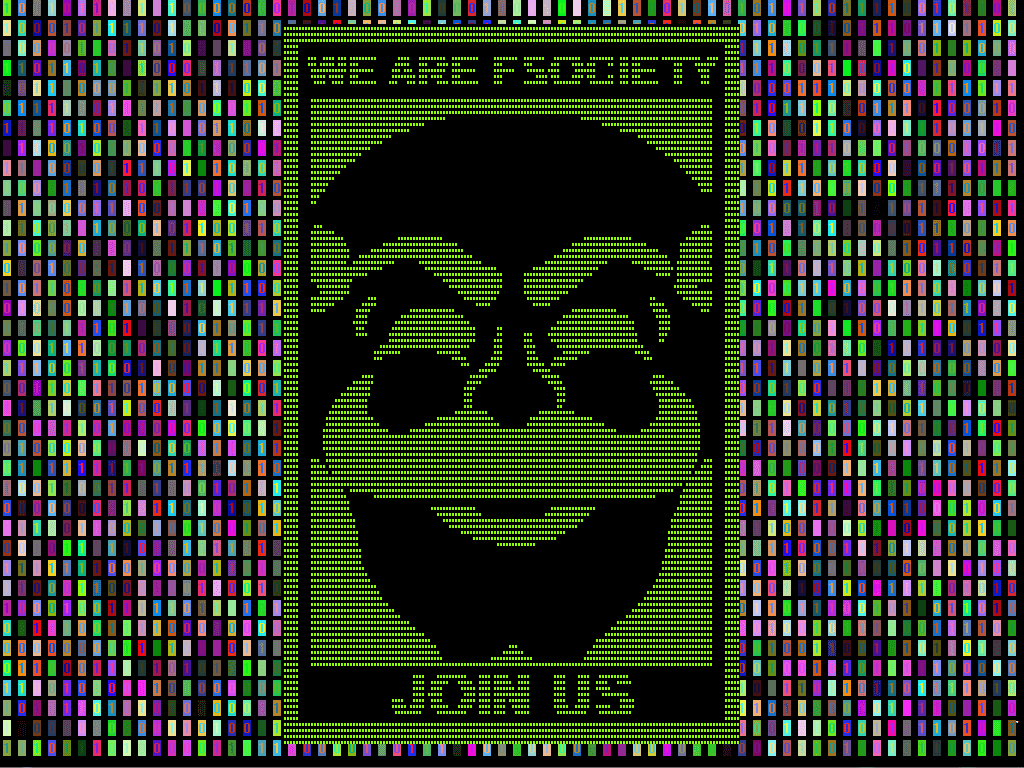
Picture displayed by KillDisk component. (Source: ESET)
The complexity of TeleBots shows just how far computer criminals will go to steal organizations' data. Cherepanov couldn't agree more:
"The cybercriminals behind these targeted attacks demonstrate serious intention to conduct cybersabotage attacks. To be able to mount such attacks, they are constantly inventing new malware and techniques, such as the use of the Telegram Bot API instead of a more conventional C&C server for example."
To protect against attacks similar to this malware campaign, organizations need to train their employees on how to spot a phish and to not click on suspicious attachments. They should also make sure macros in Microsoft Office are disabled on each relevant system.
Financial Services Cybersecurity Regulations
Learn how Tripwire's strategies bolster cybersecurity in the financial sector. Facing heightened risks, financial organizations can benefit from Tripwire's expertise in security configuration management and file integrity monitoring, ensuring compliance with critical regulations and safeguarding sensitive data.

