
A security researcher discovered an online credential stuffing list containing 111 million records that attackers could abuse to prey upon unsuspecting users. Troy Hunt, an Australian web security expert and creator of the second version of Pwned Passwords, learned about the list from several supporters of his Have I Been Pwned service. They directed him to a list called "Pemiblanc" that someone posted on a French server at the beginning of April. As of this writing, the list is no longer available, with the data now inaccessible. Inside of the list was a folder called "USA" that contained several different files consisting of email addresses and password pairs. In total, the folder stored 111 million records. These included 6.8 million email addresses and 50 million passwords that had not previously appeared in Have I Been Pwned and Pwned Passwords, respectively.
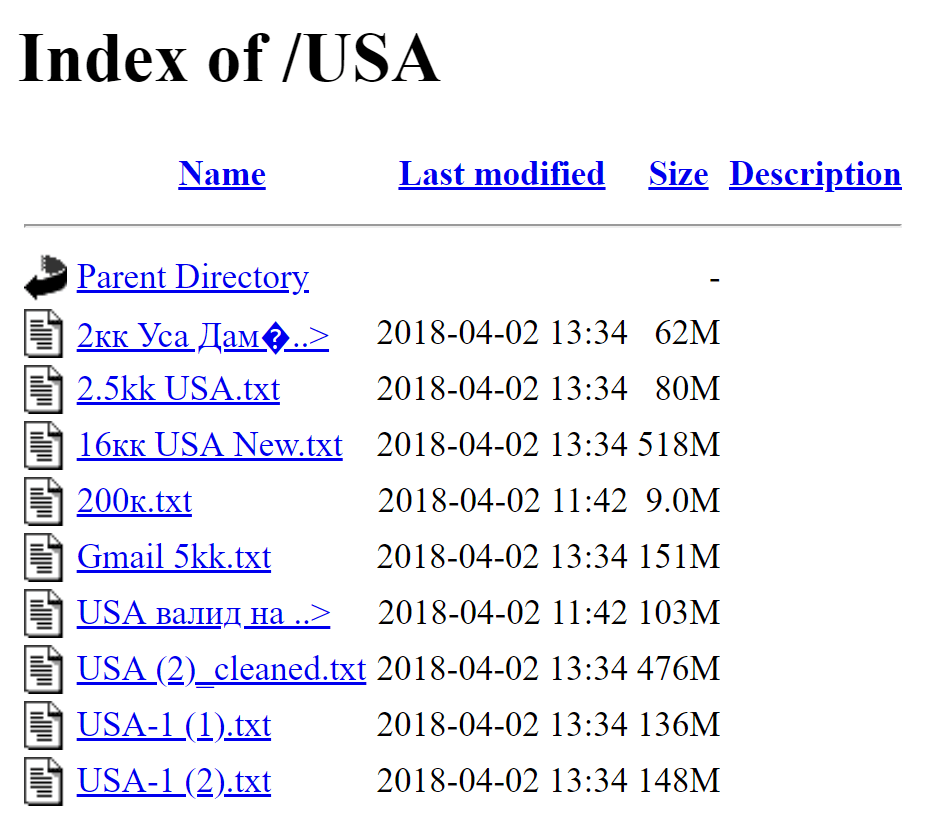
A screenshot of the USA folder's contents within the Pemiblanc list. (Source: Troy Hunt) At the time of publication, Hunt said he was working on creating a third version of Pwned Passwords so that users can check their passwords against this new data. While he works on that resource, he said it's difficult for users to learn what service might have leaked their data. Hunt said the records likely represent information exposed by multiple data breaches. Even so, he did make a recommendation to users in a blog post on how they can protect against credential stuffing attacks, or the automated injection of compromised credentials to gain access to web accounts.
The entire value proposition of credential stuffing lists goes away when people do this and the impact of a data breach is constrained to that single site rather than putting all your accounts at risk. I first wrote about password managers 7 years ago when I concluded that the only secure password is the one you can't remember and that advice is more important today than ever before.
For additional perspective on the value of password managers for account security, click here.
Zero Trust and the Seven Tenets
Understand the principles of Zero Trust in cybersecurity with Tripwire's detailed guide. Ideal for both newcomers and seasoned professionals, this resource provides a practical pathway to implementing Zero Trust, enhancing your organization's security posture in the ever-evolving digital landscape.

