
Fraudsters have designed a new LinkedIn scam that uses phishing emails and a fake website to trick job seekers into handing over their CVs. The scam begins when a user receives a phishing email disguised as a LinkedIn email. In their message, the fraudsters inform the recipient that a company is "urgently seeking for immediate employment" in their region. They urge them to upload their CV to take advantage of the opportunity.
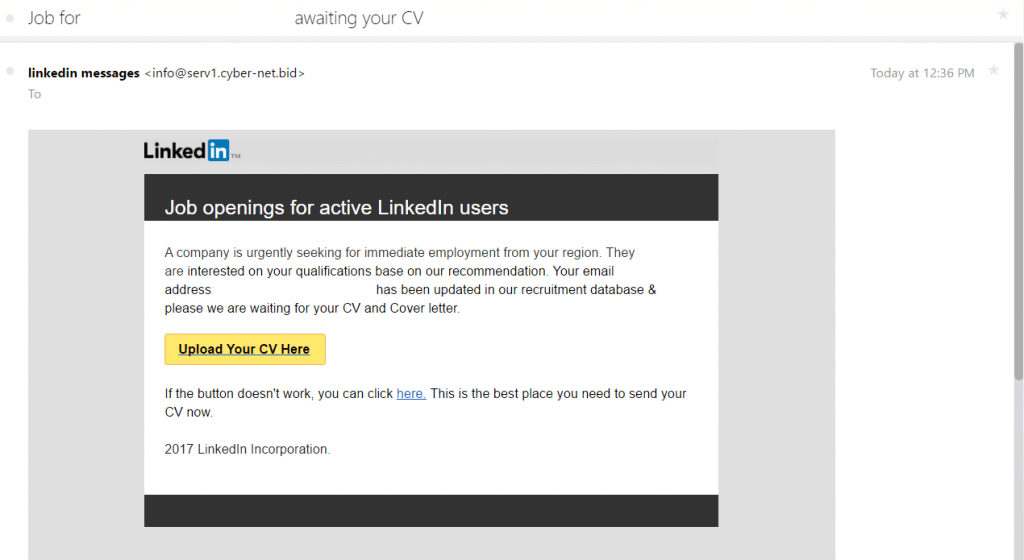
Source: Heimdal Security Aside from creating a sense of urgency, there's plenty of factors that give this email away as a fake. The email should originate from "LinkedIn" at a legitimate "@linkedin.com" email address. Instead, it comes from "linkedin messages" at the email address info@serv1[dot]cyber-net[dot]bid. (The top-level domain ".bid" mostly designates websites hosting online auctions.) The email also doesn't properly incorporate other design elements like a footer or connection suggestions that are found in actual LinkedIn emails. Clicking on the URL or the "Upload Your CV Here" button leads to https://linkedinjobs[dot]jimbo[dot]com, which as of this writing bears a 0/64 Virus Total rating.
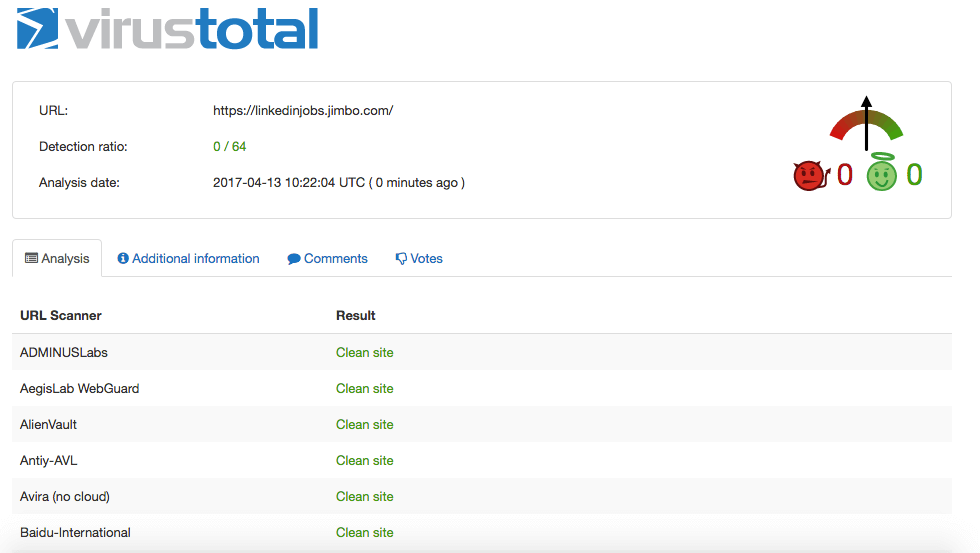
Located at that site is a web page that provides visitors with the option of submitting their CVs.
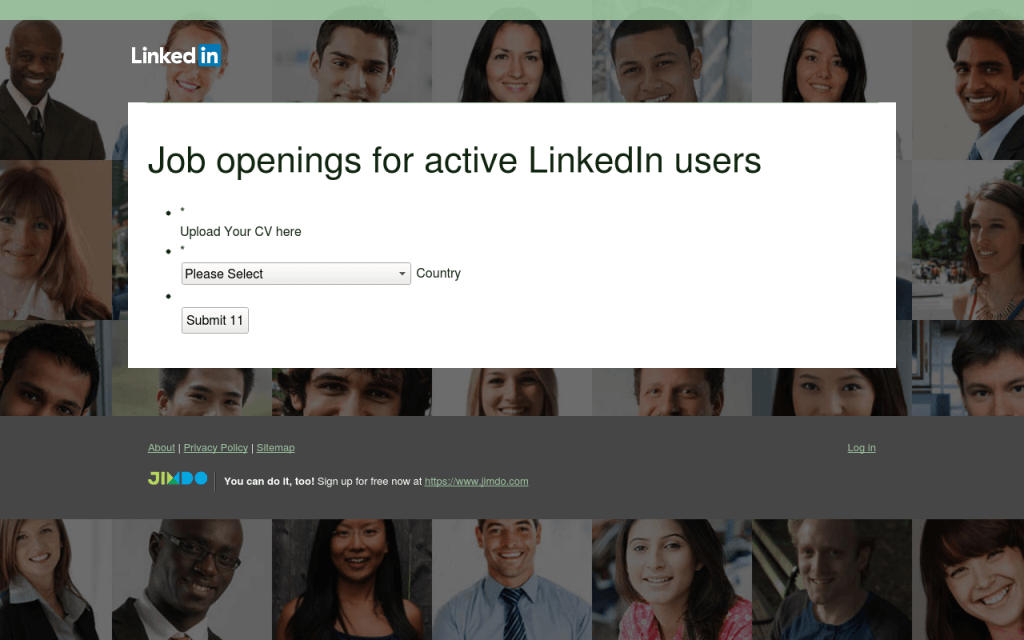
Source: Heimdal Security It's not a good idea to upload your CV to an unfamiliar website. Heimdal Security junior security evangelist Paul Cucu explains why in a blog post:
"Your CV contains a wealth of personal data which a cybercriminal uses to make a profit at your expense. Phone numbers can be sold for companies doing promotional cold calling. Or, the cybercriminal might call you himself in a vishing attack. In other cases, he might use the information for identity theft, using the companies you worked at or attached references as a cover for fraudulent activities."
Cucu goes on to note the fraudsters can also use people's CVs to conduct spear-phishing (and whaling) attacks or to perpetrate other common LinkedIn scams. To protect themselves against these types of schemes, users should confirm the sender and search for other suspicious indicators before they click on a email link. They should also verify a domain before they upload their personal information to a website.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

