LinkedIn scams are rampant. Know why? Scammers play on trust, which is why they love exploiting professional networks that have earned a trustworthy reputation. In a lot of ways, it’s the last place you’d expect. Unfortunately, given the incredibly high rates of LinkedIn scams, fake accounts, and more, it has become one of the first.
One of the reasons these scams work is because there are still those of us out there who haven’t heard of them. That leaves us vulnerable to the element of surprise and eventual compromise. So, in the interest of being informed (and staying safe), here are some of the five most common LinkedIn scams everyone needs to have on their radar.
LinkedIn Scam #1: Illegitimate Contact Request Scams
Like on any social media platform, the act of connecting with another LinkedIn user creates ample room for malicious activity. Indeed, one of the most common LinkedIn scams is when a user receives a connection request from a fake user. These types of requests may take on one of several different forms. In some, fraudsters may claim that they’re romantically interested in the recipient.
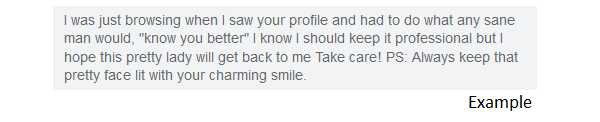
In others, they’ll play the long game by creating a fake persona that can execute a well-thought-out, custom-built attack. In his article, "The 1,000 Chinese SpaceX Engineers Who Never Existed,” Zeyi Yang chronicled one unfortunate instance in which a California professional was groomed by a fake LinkedIn user who leveraged their “shared” field of accounting. As told to NPR, once trust was established, the woman continued the conversation on WhatsApp, where she was ultimately led to transfer her money to cryptocurrency, and “after a while, she realized that those cryptocurrencies are completely lost, and she could never withdraw them back.”
This problem is all too common; there were over 63 million fake accounts blocked in the first half of 2023, per the company’s community report. Image how many got through? Hopefully, it's nowhere near that amount, but the thought is unsettling. Users should always be careful when clicking on suspicious links in their emails. If they receive an e-mail invitation to connect with another LinkedIn member, they should log into their accounts and review their connection requests there.
LinkedIn Scam #2: Fake Job Offer Scams
In this type of LinkedIn scam, users receive a LinkedIn message from someone claiming to be a job recruiter. The spammer outlines the details of a high-paying job and tells the user that they can perform their duties from anywhere with an Internet connection. This type of offer comes off sounding too good to be true for many users. To assuage their target’s skepticism, the fraudster commonly says that the offer is 100% legitimate. Those are empty assurances. When payday comes around, there’s no paycheck to be found. The victim thus decides to reach out to the “supervisor,” but in many cases, both the supervisor and payless job have already disappeared, which leaves the victim with no recourse.
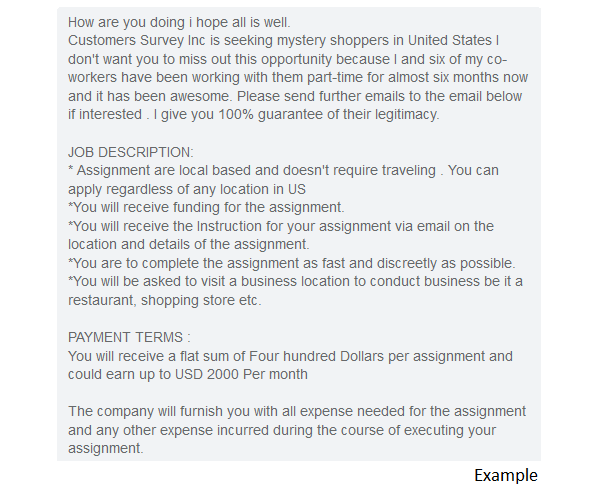
This was almost the case with Sandi Pounder, an IT professional with several years of experience who was “hired” within 48 hours of an unsolicited LinkedIn recruiting reach-out. While the ruse was caught in time, she did end up completing the entire application process as “she figured it was just how things worked in a pandemic-transformed world.” As cited in the LA Times, employment-related scams reported to the Federal Trade Commission nearly tripled between 2020 and 2021. Given the variety of fake jobs targeting LinkedIn members, it’s important that users exercise caution if they are offered a job over an in-platform message. Reputable job-search sites such as FlexJobs and Indeed.com are a better avenue for finding real, paying work.
LinkedIn Scam #3: Phishing & Whaling
Not all scammers leverage fake job offers to steal LinkedIn users’ information. In this common LinkedIn scam, bad actors used compromised accounts of other LinkedIn members, including trusted users, to send out in-platform messages urging recipients to click on a link in order to view a Google Doc. When clicked, the URL redirected the recipient to a phishing page designed to steal their Google credentials.
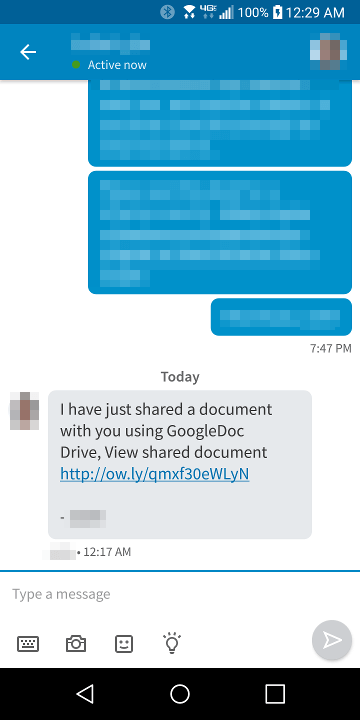
These types of campaigns are more common than one might think. According to CheckPoint, 45% of all email phishing attempts impersonated LinkedIn, with the goal of driving users to a spoofed page and stealing their credentials. These statistics reflect the wealth of information that LinkedIn offers to potential phishers. Indeed, common LinkedIn scams often leverage the information that LinkedIn users post on their profiles, which can often include details regarding where they work, the causes that they support, and the skills that they possess. They use this ammunition to launch spear-phishing—or, in the case of executives, “whaling”—attacks against companies. If one of those attacks succeeds and the scammer obtains an employee’s credentials, they could leverage those to gain access to sensitive corporate information, putting the entire organization at risk while operating beyond the security scope of the CISO, as Bleeping Computer notes.
To protect your account credentials against scammers, make sure that you treat emails and in-platform messages from people you don’t know – and even the ones you do - with caution. Invest in an email security and anti-phishing solution. Verify requests and message content in multiple places (like an email or Slack) before responding, and remember, if your boss wanted to communicate something urgent and work-related, they probably wouldn’t choose an outside social media platform to do it.
LinkedIn Scam #4: Tech Support Scams
Of course, phishers don’t always need to impersonate a trusted user or fellow employee in order to pull off a successful LinkedIn scam. Sometimes, all they need is the guise of the social media network’s technical support department.
Threat actors posing as LinkedIn IT staff will send out bogus email alerts warning users that an account compromise has been made and that they need to log in to correct the mistake. They’ll then redirect users to their LinkedIn login page, but of course, it is a spoofed site designed to steal the user’s credentials. Or they’ll provide a phone number to “Customer Support” and ask for sensitive account information there. Often, they’ll even charge you for the service.
To guard against these tactics, the company offers the following advice: think before you act on a message, keep in mind that cybercriminals try to get you to react, remember that no legitimate organization ever asks for login credentials, and report LinkedIn scams to the Internet Crime Complaint Center.
LinkedIn Scam #5: Advanced Fee Scams & Inheritance Scams
We have seen these 419 scams flood our Spam folders for years, so it is only fitting that we would come across them on LinkedIn from time to time. These are the messages from a distant relative or public figure asking you to send over your account information so they can wire you (previously unknown) inheritance money. Of course, a small cut will go to them as a processing fee, and more often than not, that includes whatever you have in your account at the time.
While these may seem obvious to spot, newer and more obvious LinkedIn scams center around cryptocurrency. CNBC reports that typically, “the fraudster directs the user to a legitimate investment platform for crypto, but after gaining their trust over several months, tells them to move the investment to a site controlled by the fraudster. The funds are then drained from the account.” When dealing with money, it’s best to avoid it on any social media site.
As the U.S. Army Cybercommand official website sums up, “Users who get these ‘advanced fee’ scam messages in LinkedIn should not reply and report the messages to the platform.” Having the wherewithal to avoid an inheritance scam is the first step; protecting others by reporting nefarious campaigns should be the next.
How to Tell if a LinkedIn Message Is Real
If you’re uncertain of the legitimacy of a LinkedIn message, look for the following signs of probable authenticity:
The sender’s profile is detailed and comprehensive
The sender regularly shares, comments, and is otherwise engaged and active with LinkedIn content across the platform
You and the sender have connections in common
The message doesn’t contain attachments
The message doesn’t contain suspicious links (hover over the URL without clicking to see if the address is legitimate)
The sender isn’t creating an undue sense of urgency or pressure, nor are they promising something too good to be true
The contents of the message are relevant and personalized
No one of these indicators is a guarantee that the LinkedIn message is real, but, taken together, they can help you determine the message’s authenticity.
Conclusion
Social networking sites are a useful tool for connecting with friends and colleagues. But we must remember that, like on any website, scammers prowl these platforms for unsuspecting users. As you build your connections, remember to keep an eye out for the common LinkedIn scams that could bring your professional momentum to a halt.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.


