
Locky ransomware is now appending the ".lukitus" extension to victims' files after it's completed its encryption routine. On 16 August, Fortinet junior anti-virus analyst Rommel Joven came across one of Locky's newest variants. https://twitter.com/rommeljoven17/status/897766198674300928 The ransomware is making its way onto users' machines via a malspam campaign. Many of the attack emails don't contain any subject lines, a tactic we've seen in other ransomware distribution campaigns. Though some come with a subject containing a suspicious string of letters and numbers like "Emailing - CSI-034183_MB_S_7727518b6bab2." In both cases, the malspam messages speak of an "email bill request" and attempt to trick the recipient into opening an attachment that contains JS files. If the recipient clicks on the attachment, the JS files download Locky from a remote site. Bleeping Computer's Lawrence Abrams explains what Locky's variant does next:
"Once the file is downloaded and executed, it will scan the computer for files and encrypt them. When this Locky variant encrypts a file it will modify the file name and then append the .lukitus. When renaming the file, it uses the format [first_8_hexadecimal_chars_of_id]-[next_4_hexadecimal_chars_of_id]-[next_4_hexadecimal_chars_of_id]-[4_hexadecimal_chars]-[12_hexadecimal_chars].lukitus. "This means that a file named 1.png would be encrypted and named something like as E87091F1-D24A-922B-00F6B112-72BB7EA6EADF.lukitus."
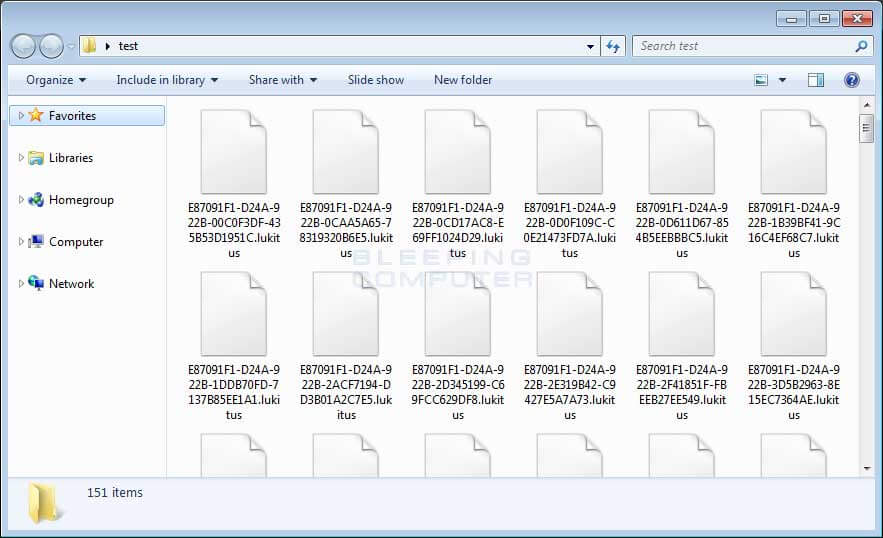
Files encrypted by the Lukitus Locky ransomware variant. (Source: Bleeping Computer) Upon completing its encryption routine, the ransomware deletes its downloaded executable and displays its ransom note to the victim. That message contains a link to a .onion website where a victim is instructed to pay 0.49 Bitcoins (more than US$2000) in exchange for the decryption key. At this time, there is no way for Lukitus victims to decrypt their files for free. Users should therefore focus on protecting themselves against Locky and other ransomware threats by following crytpo-malware prevention strategies. These tips include updating their computers, exercising caution around suspicious links and email attachments, and backing up their important data on a regular basis.

