
A malicious Google Chrome extension punishes users who search for certain keywords by redirecting them to a tech support scam. Attackers introduce users to the rogue extension via a malvertising campaign. Most of the time, malicious adverts redirect users to an exploit kit that installs ransomware or other baddies. In this case, the advertisement leads a user to a web page that plays an interminable loop of fullscreen modes. Their only option is to install the extension if they wish to leave.
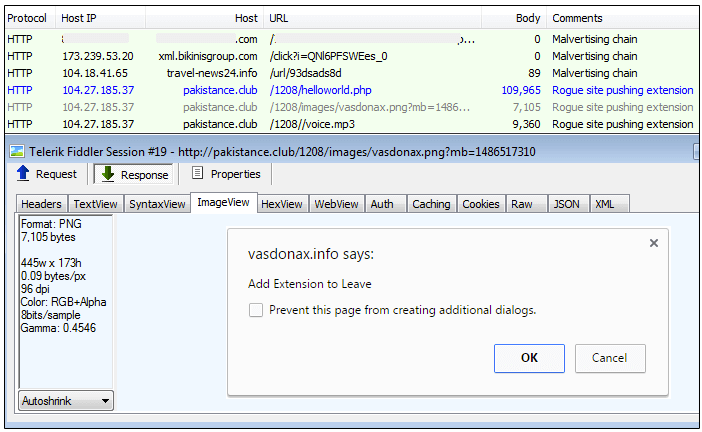
The malvertising flow that leads to the malicious Chrome extension. (Source: Malwarebytes) This extension is designed to achieve a level of persistence on a victim's machine. As Malwarebytes lead malware intelligence analyst Jérôme Segura explains in a blog post:
"Once installed, this extension ensures it stays in hiding by using a 1×1 pixel image as its logo (note the blank space on the top right next to the Chrome menu from the animation below) and by hooking chrome://extensions and chrome://settings such that any attempt to access those is automatically redirected to chrome://apps. That makes it much more difficult for the average user to see what extensions they have, let alone uninstalling one of them."
Redirection from chrome://settings and chrome://extensions to chrome://apps. (Source: Malwarebytes) Such cover helps the extension execute its primary functions. First, similar to the Webpage Screenshot extension discovered in 2015 and the add-on secretly pushed out by Adobe Acrobat in early 2017, it collects information and sends all data back to a location of its choosing. Second, and by far much worse, it'll look for certain keywords in the URL to determine whether it should trigger redirection/blocking techniques. For example, if a user attempts to visit the Malwarebytes website, the extension will redirect them to a potentially unwanted program (PUP) or get-rich-quick scheme. Certain keywords will even trigger a redirect to a fake Microsoft tech support warning.
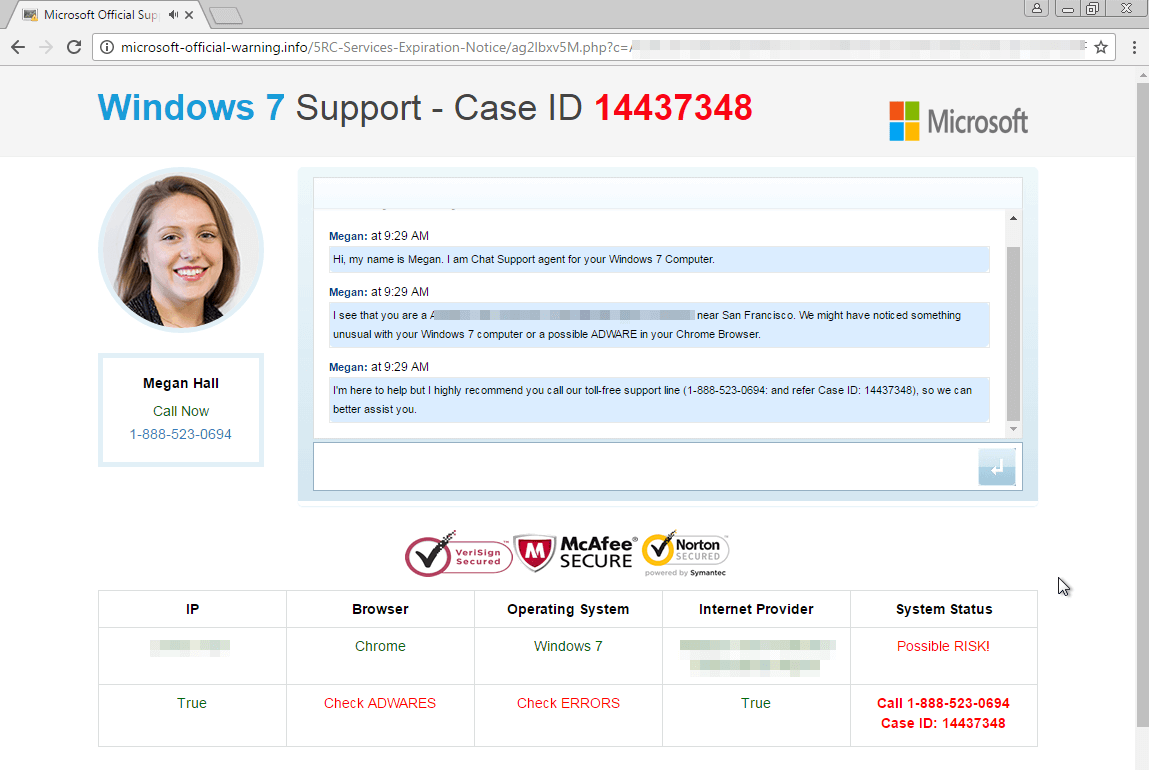
Tech support scam pushed by the malicious Chrome extension. (Source: Malwarebytes) Given this threat, Segura recommends users adopt a realistic viewpoint of Chrome extensions:
"Google Chrome extensions are very powerful programs which are extremely useful in extending the browser’s capabilities, but can also be used for malicious purposes. Unfortunately, it is way too easy for online crooks to trick people into installing their malicious extension."
Google has removed the rogue extension from its store as of this writing.

