
A spam campaign is personalizing its emails with the recipient's name and address so that more people will feel inclined to open the malicious attachment. Sophos Labs has seen several versions of this scam pop up in recent weeks. But although the text differs across samples, all the emails generally follow the same format. The scam email includes the recipient's first name in the salutation, their last name as the title of the attachment, and their physical address in the body of the message. Here's one example of the scam.
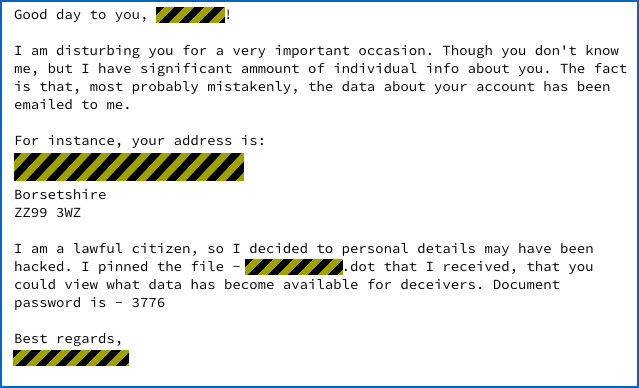
Sample scam email. (Source: Sophos Labs)
"Good day to you, [FIRST NAME] I am disturbing you for a very important occasion. Though you don't know me, but I have significant ammount of individual info about you. The fact is that, most probably mistakenly, the data your account has been emailed to me. For instance, your address is: [STREET ADDRESS] Borsetshire ZZ99 3WZ I am a lawful citizen, so I decided to personal details may have been hacked. I pinned the file - [LAST NAME].dot that I received, that you could view what data has become available for deceivers. Document password is - 3776. Best regards, [SENDER NAME] [sic]"
It's not clear where the attackers obtain each recipient's personal information. But considering the wealth of data breaches, it's probable they purchased the data on an underground forum. They then could have used an automated tool to properly format the address based upon the recipient's country of origin. So what happens if the recipient clicks on the attachment? Nothing too out of the ordinary. A Microsoft Word document opens and prompts the user to enter the password. It then asks them to "Enable Content". If the user complies, the document tries two different web pages hosted on hacked servers and loads what appears to be a GIF file.
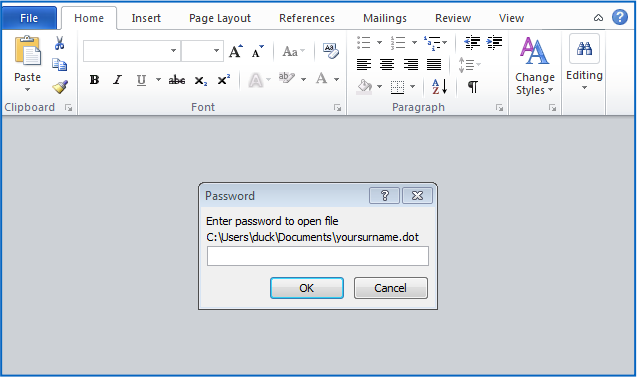
Password prompt in scam emails. (Source: Sophos Labs) But as Sophos Labs senior security advisor Paul Ducklin explains in a blog post, there's more to this file than meets the eye:
"In fact, the GIF file has just 10 bytes of valid header data, followed by a 256-byte decryption key, followed by about 0.5MB of binary data scrambled by XORing it with the decryption key repeated over and over. (This is known as a Vigenère cipher, named after a cryptographer from the 1500s who didn’t actually invent it.) "The GIF header makes the file look innocent, even though it won’t display as an image, and the Vigenère scrambling means that the suspicious parts of the file aren’t obvious."
At that point, the malicious code embedded in the Word document initiates a decryption process of the executable and saves it to the Temp folder. When Sophos Labs tested this attack vector, malware known as Troj/Agent-AURH infected their computer. The trojan enlisted their machine into a botnet and then awaited further instructions from its command and control (C&C) server. This is not the first scam of its kind. We've seen other personalized campaigns targeting users in the UK and Germany. Those emails infected recipients with Maktub Locker ransomware and a banking trojan named Nymaim.B, respectively. To defend against these types of scams, users should avoid clicking on suspicious links and email attachments. They should also not click on an attachment just because the email contains their personal information. Rather, they should generally assume someone gained their information from a data breach. They should therefore monitor their accounts for any signs that are indicative of fraud. If they believe the scam emails are more targeted in nature, they should report the attacks to law enforcement.

