
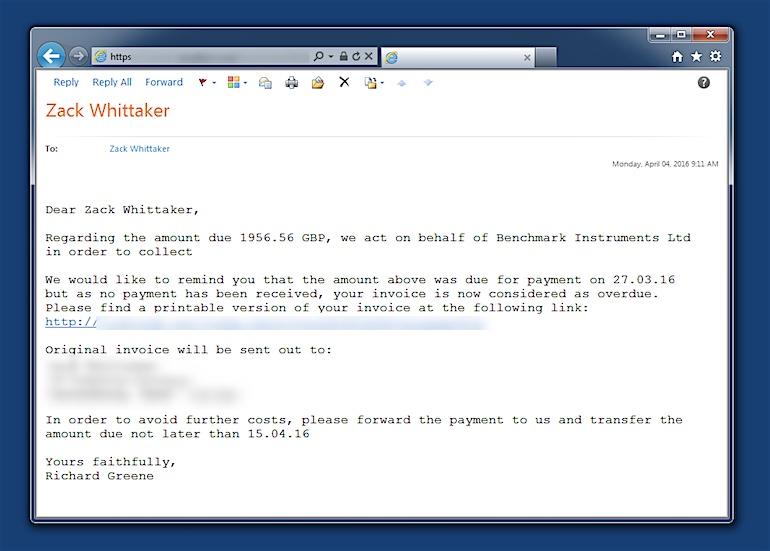
A new phishing scam is targeting thousands of people with scam emails that contain the recipient's home address. On Wednesday, Zack Whittaker, a writer for ZDNet, received a spam email that contained his home address from approximately eight years ago.
"The well-worded email appears to come from a legitimate email address and domain name, and raises very few irregularities," he explains in a blog post. "The email comes with an demand for money for an arbitrary service, along with a link that purports to be an 'overdue invoice.'"
Clicking on the link, which is disguised to look like a Word document, downloads Maktub Locker, a form of ransomware that is unique in that it does not need to call home to a C&C server for an encryption key. This means that encryption can proceed offline if a victim happens to click on the link.
Source: ZDNet/CBS Interactive At the time, Whittaker and the ZDNet team did not think too much of the spam email. But then BBC Radio 4's You and Yours team published an article in which they said some of its members had been targeted.
"The email has good spelling and grammar and my exact home address...when I say exact I mean, not the way my address is written by those autofill sections on web pages, but the way I write my address," recalls You and Yours reporter Shari Vahl. "My tummy did a bit of a somersault when I read that, because I wondered who on earth I could owe £800 to and what was about to land on my doormat."
It is currently unclear how the scammers gained access to their targets' home addresses. Security researchers believe the attackers emptied a database from a hacked retailer or website that contained customers' personal information. This campaign marks a developing trend where computer criminals are forgoing traditional phishing campaigns for attacks that blend together malware and social engineering techniques. Earlier this week, Proofpoint published a blog post on a financially motivated threat actor, known as TA530, that has been targeting company executives with phishing emails. The emails include the recipient's name, job title, phone number, company name, and other information, and they deliver a malware payload such as CryptoWall. The threat actor has thus far sent out a third of a million emails targeting executives in the United States, the United Kingdom, and Australia. Given this ongoing evolution of phishing attacks, users are urged to be on the lookout for suspicious emails and to never click on suspicious links. For more information on how to detect a phishing attack, please click here.

