
A security researcher found a misconfigured ElasticSearch cluster that exposed over 90 million personal and businesses data records.
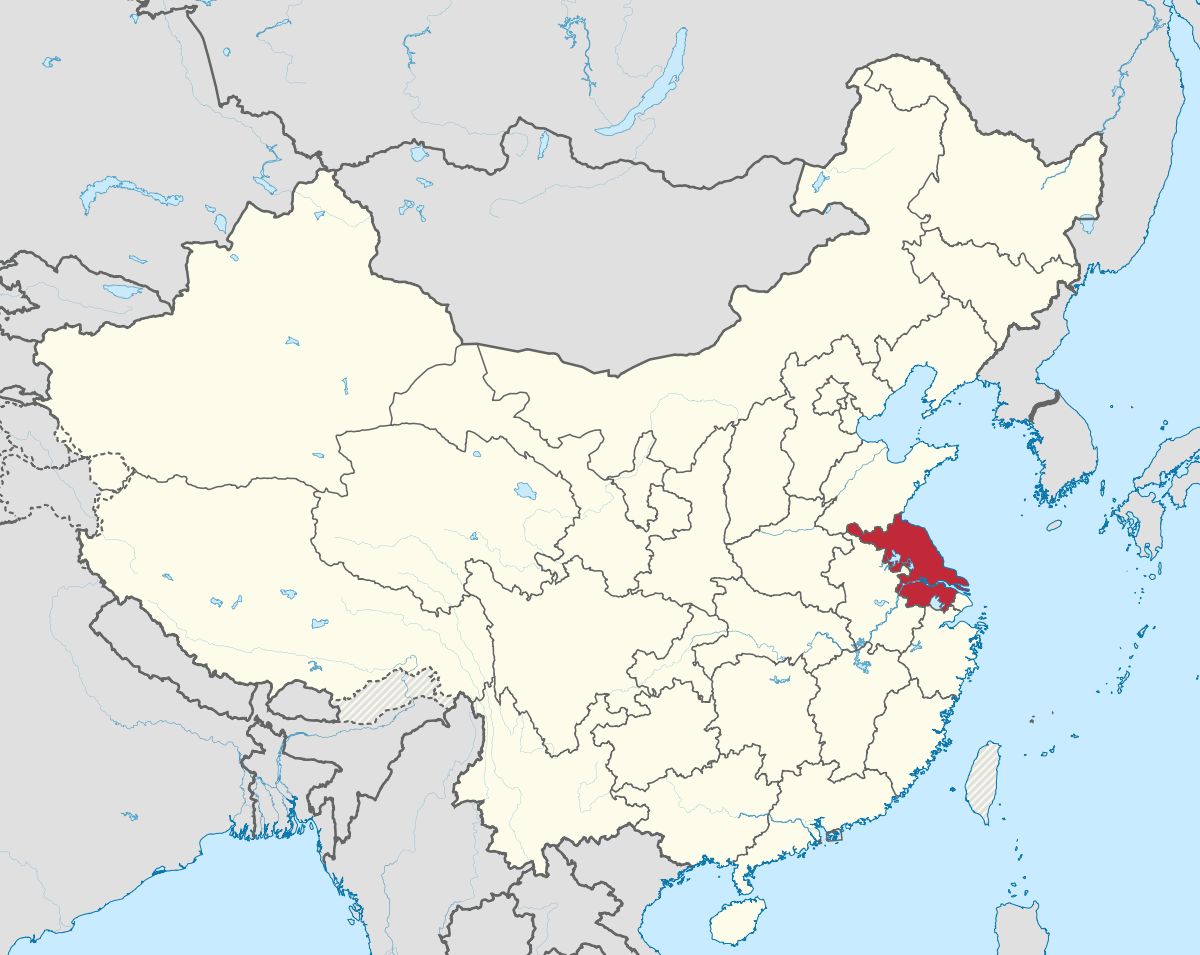
A map of China, with the Jiangsu Province marked in red. On 1 July, GDI Foundation member and an independent security researcher Sanyam Jain found that the unprotected ElasticSearch server lacked proper configuration in that it sent anyone to the "Create index pattern page" once it loaded in a browser. Through this misconfiguration, Jain discovered that the server hosted two databases containing 26 GB of information. Among that data was personally identifiable information including names, birth dates and identity card numbers as well as business details such as business IDs and location coordinates. In total, the two databases held more than 90 million records at the time of discovery. Jain determined that the ElasticSearch cluster belonged to the Provincial Public Security Department of Jiangsu, an eastern-central coastal province in China with a population of over 80 million. But that's not all the security researcher found. He also observed that the Provincial Public Security Department owned a Public Security Network admin console requiring valid login credentials and a publicly-accessible Kibana installation. This isn't the first time that Jain has discovered exposed ElasticSearch servers. In April, he was one of several researchers who came across several exposed servers that belong to Chinese recruitment firms. A month later, he found an unprotected database that made it possible for anyone on the web to view the personal and employment information of 13.7 million users. In this latest case, Jain attempted to reach out to the Jiangsu Provincial Public Security Department as well as the National Computer Network Emergency Response Technical Team / Coordination Center of China (CNCERT/CC) on 2 July. It was around that same that the researcher contacted Bleeping Computer about the disclosure. On 4 July, the computer security website notified CNCERT/CC about the exposed cluster. CNCERT/CC responded within a day and said that it had notified the server owners. The server was no longer reachable three days later.
Mastering Security Configuration Management
Master Security Configuration Management with Tripwire's guide on best practices. This resource explores SCM's role in modern cybersecurity, reducing the attack surface, and achieving compliance with regulations. Gain practical insights for using SCM effectively in various environments.

