
An unprotected database made it possible for anyone on the web to view the personal and employment information of 13.7 million users. Security researcher and GDI Foundation member Sanyam Jain discovered the database and determined that it belonged to Ladders, a New York-based job recruitment site which specializes in high-end jobs. Jain then shared his findings with TechCrunch. In its analysis of the database, TechCrunch found that the database consisted of 13.7 million data records. Each of those files included several bits of personal information including an individual's name, email address, postal address, phone number and IP address. Every record also included an individual's employment data including their employer history, security clearances and in some cases detailed job descriptions of previous work going back several years.
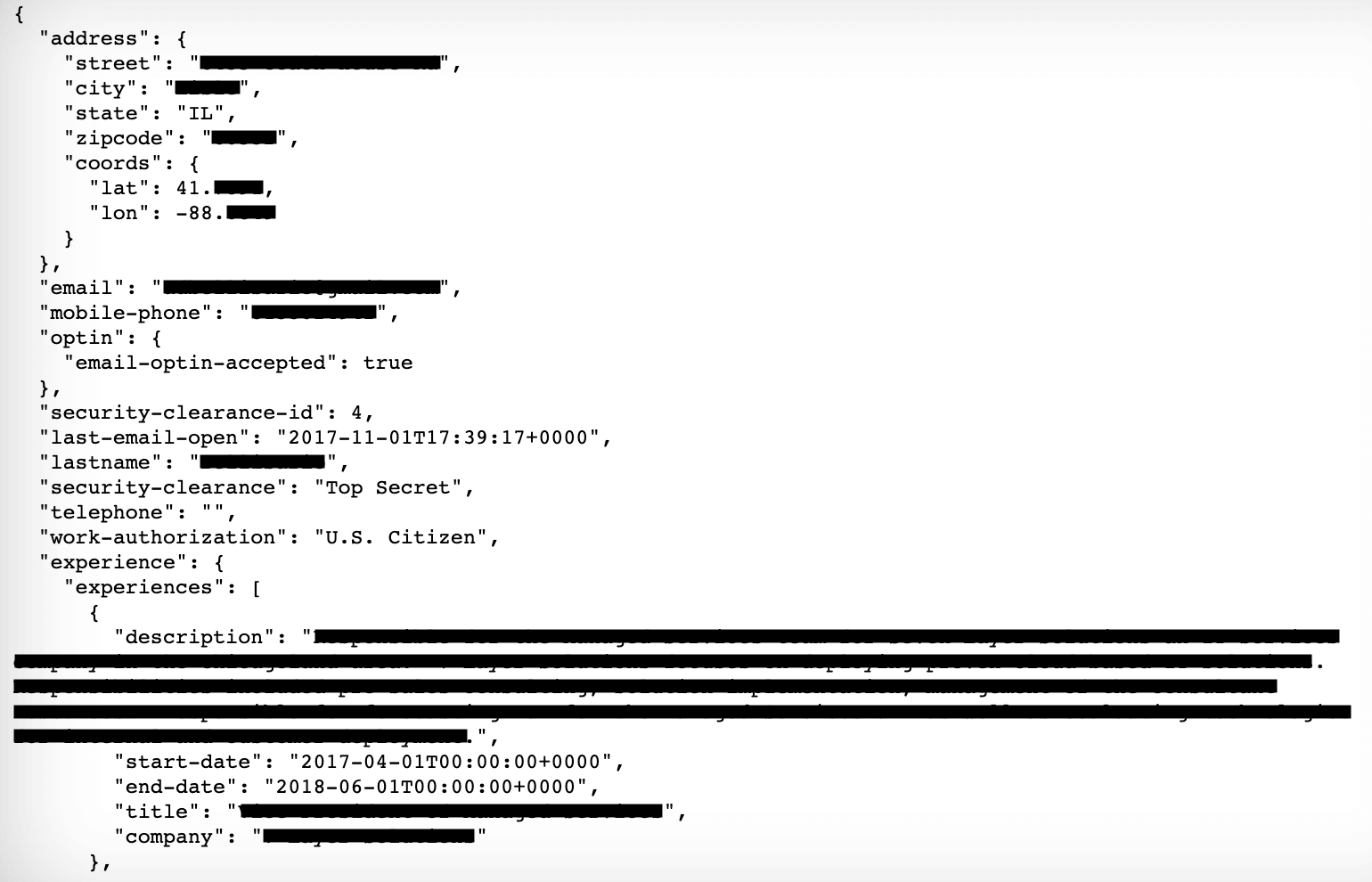
A partial record (redacted) including a person’s name, address, phone number, job description and details of their security clearance (Source: TechCrunch) The database, an Amazon-hosted Elasticsearch asset that lacked a password at the time of discovery, also exposed less sensitive details of 379,000 job recruiters. Subsequently, TechCrunch took it upon itself to verify the information contained in the database. It did so by contacting more than a dozen users of the site. Several of those individuals confirmed that the information was correct, while one even said they had stopped using Ladders after learning of the data breach. TechCrunch also reached out to Ladder about the security incident. In less than an hour, the recruitment site responded by pulling the database offline. Marc Cenedella, chief executive of Ladders, explained in a statement provided to TechCrunch that the company is currently working to determine the impact of this breach:
AWS confirms that our AWS Managed Elastic Search is secure, and is only accessible by Ladders employees at indicated IP addresses. We will look into this potential theft, and would appreciate your assistance in doing so.
News of the incident follows less than a month after Jain along with security experts Devin Stokes and Bob Diachenko discovered several exposed servers that belong to Chinese recruitment firms.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

