
A new proof-of-concept ransomware is capable of targeting the programmable logic controllers (PLCs) that help manage critical infrastructure. Researchers at Georgia Institute of Technology designed a cross-vendor ransomware worm known as LogicLocker to specifically seek out vulnerable PLC computers that are exposed online. At they write in their paper (PDF):
"LogicLocker uses the native sockets API on a Schneider Modicon M241 to scan the network for known vulnerable targets, namely Allen Bradley MicroLogix 1400 PLCs and Schneider Modicon M221 PLCs, and infect them by bypassing their weak authentication mechanisms, locking legitimate users from easily recovering the PLC, and replacing the program with a logic bomb that begins to dangerously operate physical outputs threatening permanent damage and human harm if the ransom is not paid in time."
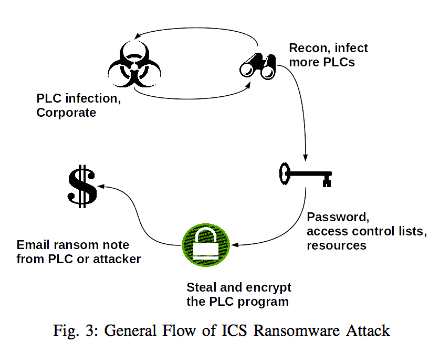
To test their ransomware, they used Shodan to discover vulnerable PLCs connected to the web. They found 1,400 such devices. The research team therefore programmed their ransomware to search the web and target a vulnerable PLC directly. If malware like BlackEnergy were to infect a workstation at an industrial site, attackers could alternatively introduce LogicLocker after that initial compromise. Most PLCs don't come with strong authentication measures that block the installation of new programs. As a result, attackers could simply search for and exploit a vulnerability on a target PLC. With this level of control, they could change the password on the PLC and thereby deny operators from accessing the computer. They could then move laterally and/or vertically, infecting additional PLCs and even compromising the rest of the network. The researchers hypothesize that a group of attackers could encrypt the raw binary of each infected PLC's program and send it to the victim along with a ransom note. They feel the bad actors could have a little "fun" in the process. All they would need to do would be to impress the seriousness of the threat on the victim. Here's how the researchers feel a LogicLocker infection at a water treatment facility could go:
"If the ransom is paid by the ultimatum, the attacker gives the victim a program that will reload the original programs, but if it is not paid he threatens to dump harmful amounts of chlorine into the water supply. To maximize chances of success, before notifying the victim of compromise LogicLocker first allows the level of the water in the storage tank get low while sending false level readings to the operators. Therefore, given the choice between paying and attempting a recovery, the victim also has to consider the effects of waiting too long and running completely out of clean water."
Considering the dangers of extended downtime, industrial organizations are a perfect target for PLC-seeking ransomware families like LogicLocker. Organizations should make an effort to protect against these new threats via implementing defense-in-depth strategies at the endpoint level, segmenting the IT network from the control network, and educating all employees about phishing attacks.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

