
A new variant of Petya ransomware has reportedly struck banks, airports, and power utilities in an apparent outbreak affecting Ukraine, Russia, and parts of Europe. Ukraine's national bank, state power company, and airport appear to have been some of the attack campaign's first victims. In a statement, the National Bank of Ukraine attributed the event to an "unknown virus." As quoted by Reuters:
"As a result of these cyber attacks these banks are having difficulties with client services and carrying out banking operations. The central bank is confident that the banking infrastructure's defence against cyber fraud is properly set up and attempted cyber attacks on banks' IT systems will be neutralised."
Oschadbank, a state-owned lender in Ukraine, along with Ukrainian state power distributor Ukrenergo separately confirmed digital attacks against their systems. The latter said the incident didn't affect availability of power supplies. This clarification comes less than two weeks after researchers unveiled their discovery of Industroyer/CrashOverride, modular malware which many in the security community believe was responsible for an attack against Ukrenergo on December 17-18, 2016 that caused parts of Kiev to lose power for a short period. The latest attacks against Ukraine appear to be part of a campaign targeting the Eastern European country's government infrastructure. Rozenko Pavlo, the deputy Prime Minister, told The Independent he and other members of Ukraine's government couldn't access their computers:
"We also have a network 'down'. This image [below] is being displayed by all computers of the government."
https://twitter.com/RozenkoPavlo/status/879677026256510976 Following early reports of attacks, other affected Ukrainian organizations came forward. The state-run aircraft manufacturer Antonov, Ukrposhta state postal service, multiple television stations, and Kiev's metro system confirmed to The Independent that the campaign had also struck them. So too did Boryspil, an international airport based in Kiev which suffered a targeted attack at the hands of BlackEnergy malware in early 2016.
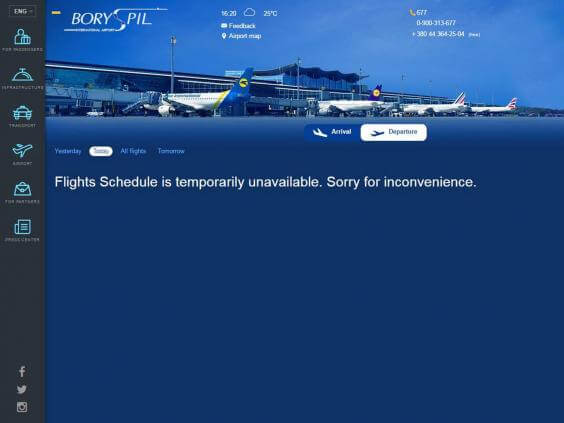
The website of Boryspil International Airport during a digital attack targeting Ukrainian infrastructure on 27 June 2017. (Source: The Independent) But the attacks haven't just struck entities in Ukraine. Maersk, a Danish transport and energy company, posted a statement to its website on 27 June indicating it had experienced a security incident:
"We can confirm that Maersk IT systems are down across multiple sites and business units due to a cyber attack. We continue to assess the situation. The safety of our employees, our operations and customer's business is our top priority. We will update when we have more information."
Russian oil company Rosnoft wasn't far behind. https://twitter.com/RosneftRu/status/879665160012673024 Translated into English:
"On the servers of the Company a powerful hacker attack was carried out. We hope that this has nothing to do with the current judicial procedures."
The attack appears to have also affected France’s Saint-Gobain, the offices of multinationals in Spain, and the British advertising group WPP. In their analysis of this campaign, many security experts said the attack appears to be consistent with Petya ransomware. https://twitter.com/mikko/status/879701456563175424 Petya is not like most other crypto-ransomware, malware which targets victims' files for encryption and demands a ransom from victims in exchange for the decryption key. Instead it encrypts the Master File Table (MFT), a file on NTFS partitions that contains critical information about every other file including their name and size. Successful encryption prevents an infected computer not only from finding the locations of users' files but also from determining whether that data even exists. The MFT encrypter gained a considerable boost on the digital underground in the summer of 2016. At that time, its handlers announced a new ransomware-as-a-service (RaaS) platform for Petya and Mischa, an ordinary file-encrypting ransomware. Under this affiliate system, Petya executes on a machine and encrypts a user's MFT if the malware acquires administrator rights on a machine. Otherwise, Mischa sets to work individually encrypting the victim's files. https://twitter.com/codelancer/status/879688596852101120 This latest Petya campaign is the second widespread ransomware outbreak to surface in less than two months. Back in May 2017, WannaCry ransomware affected more than 300,000 organizations in over 150 countries. It struck the United Kingdom's National Health Service (NHS), the telecommunications provider Telefonica, and others by exploiting a Windows SMB vulnerability using exploit code developed by the National Security Agency and leaked online by the hacker group the Shadow Brokers. Symantec and others have confirmed that Petya is using EternalBlue, the same exploit leveraged by WannaCry, to spread to vulnerable Windows machines after establishing an initial infection via malicious emails. https://twitter.com/threatintel/status/879716609203613698 If you didn't patch your system following the WannaCry campaign, it's imperative you do so now. You can find a patch for this exploit in Microsoft's security advisory issued back in March 2017. This is a developing story. Check back soon for further details.

