Without a doubt, log management should be part of the core of any IT security platform of a government agency. It has a role in not only security but also in operations and compliance requirements. Logging can provide situational awareness of things happening within an environment by keeping track of events recorded in the logs of the different systems that support an agency. After all, logs contain vital information that IT security and administration officials can use to gain a clear understanding to what is occurring in their environments, including potential threats that are being exploited. Visibility, monitoring, and analytics are key for an organization to be successful in protecting and monitoring their environments. That sounds great and all, but it produces its’ own set of challenges.
Log Management: The Challenges Agencies Face
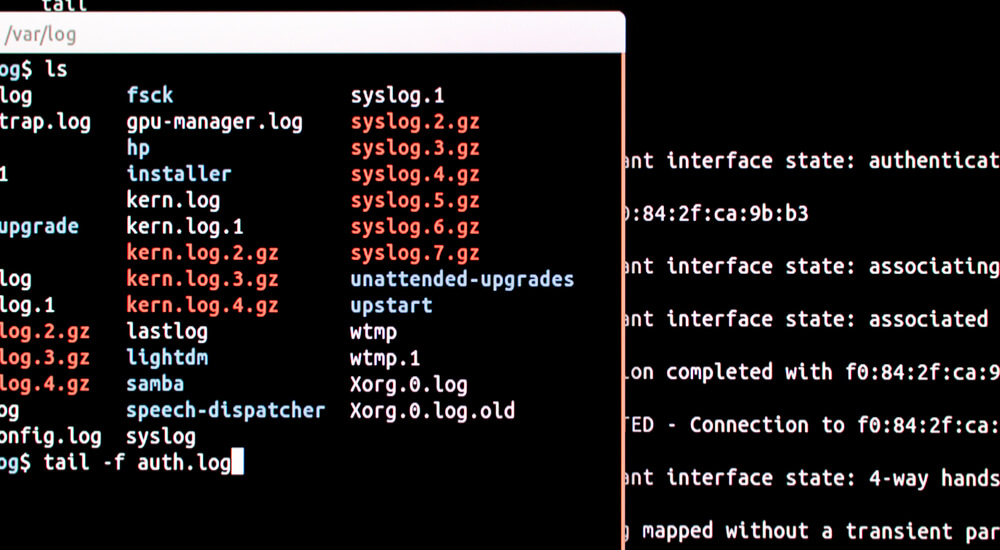
Keep track of logs can be an overwhelming task. Without quality analytics and expertise, it is far too easy for security threats to creep in unnoticed. Storage of log data can become costly and time-consuming. Agencies will find themselves paying to store data that doesn’t need to be in the analytic tools. As a result, it is important to keep a laser-like focus on the role that log management should play in security, IT operations, and compliance. For security, logging plays an important role in helping security teams identify malicious attacks through software and trace the steps of the attack on an organizations system. Audit logs allow a security team to be notified when an attack is occurring and allows them to respond before organization systems are compromised. This includes keeping track of multiple systems to be able to trace any series of events that led to the compromise. If data on a system is not collected and stored, then this may produce a gap in understanding of what is happening in the environment. IT operations still benefit greatly from a well-done log management solution. Logs can provide the necessary information for what is happening on a system. It’s invaluable to be able to troubleshoot anomalies within the organization by providing error and debug information. This can become time-consuming without a centralized way of storing and searching through the information. Manual processes easily overwhelm an organization. It’s also important to proactively watch a system for warnings and performance indicators. This allows organization to respond before an actual problem or outage occurs. Compliance seems to be the biggest factor within government agencies that drives a good log management practice. The Federal Information Security Management Act (FISMA) for 800-53 has become the primary standard by which most agencies are measured for compliance. Requirements for logging are found in the Audit and Accountability (AU) section for NIST 800-53. It contains details on what to keep, what to capture, and how to respond. The latest draft for NIST 800-53 can be found at crsc.nist.gov. Selecting the right log management solution can mean the difference between success and failure. Organizations should understand the criteria in order to be successful.
Learn how Log Management can enhance cyber situational awareness, and complement the SIEM, Security Analytics or Big Data tools within your agency, here.
Tripwire Enterprise: Security Configuration Management (SCM) Software
Enhance your organization's cybersecurity with Tripwire Enterprise! Explore our advanced security and compliance management solution now to protect your valuable assets and data.

