Now in its 11th installment, Verizon’s Data Breach Investigations Report (DBIR) is a must-read for cybersecurity professionals across the globe. The 2018 edition dives deep into more than 53,000 real incidents and 2,216 confirmed data breaches with the ultimate goal of informing defenders on the threats they face and how to protect against them. The 68-page report is available for download here, but if you’re looking for the key takeaways, we’ve highlighted some of this year’s key findings below.
The Big Picture
Outsiders were behind the majority of cyberattacks last year (73 percent). Organized crime groups carried out 50 percent of all data breaches with 12 percent involving actors known as nation-state or state-affiliated. Meanwhile, 28 percent of data breaches were perpetrated by internal actors. Nine out of 10 times, the main drivers motivating them were financial gain and espionage.
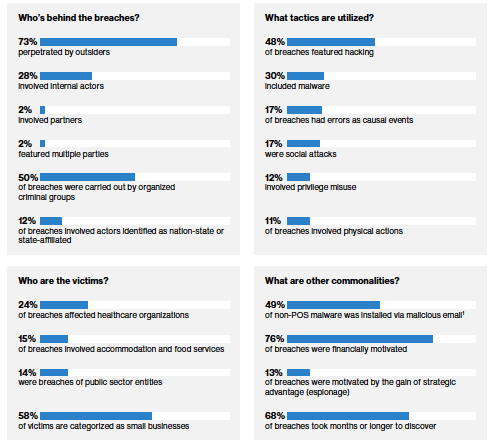
Source: Verizon DBIR, pg. 5
Breach Timeline
It takes cybercriminals just minutes, or even seconds, to compromise a system – but only three percent of breaches are discovered as quickly. Sadly, this year’s report shows that two-thirds (68 percent) of attacks went undiscovered for months or longer. Tim Erlin, VP of Product Management & Strategy at Tripwire, believes that faster recovery begins with monitoring for changes on the network:
"It may seem trite, but every incident begins with some kind of change. Organizations shouldn’t underestimate the value of being able to detect changes in their environment and make sense of them. Start by understanding what you have, then by ensuring it’s deployed securely, and follow-up with monitoring for changes. If you need an independent third-party to justify these controls, the CIS 20 critical security controls does exactly that."
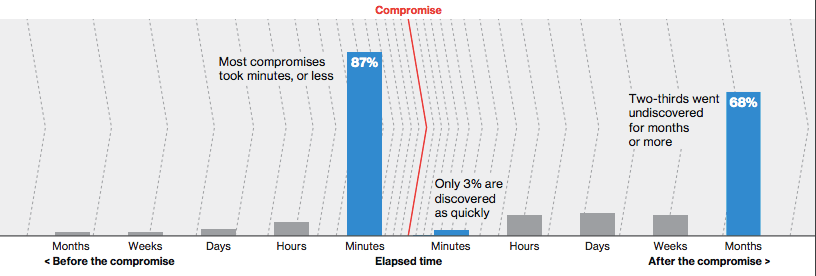
Source: Verizon DBIR Executive Summary, pg. 6
Social Attacks
Unfortunately, humans are still considered the weakest security link – something organizations should be wary of when 98 percent of incidents and 93 percent of breaches involved phishing and pretexting (defined by the DBIR as the creation of a false narrative to obtain information or influence behavior). On the bright side, 78 percent of people in a median-sized organization don’t click a single phish all year. However, four percent of people in any given phishing campaign will click the link, but at least it’s an improvement from 11 percent back in 2014.
Ransomware
This year’s report crowned ransomware as the most prevalent variety of malware, seen in 39 percent of cases where malicious software was identified. The DBIR also notes that in recent years, we’ve seen more server assets affected, meaning “infections aren’t limited to the first desktop that is infected.”
"Lateral movement and other post-compromise activities often reel in other systems that are available for infection and obscuration. Encrypting a file server or database is more damaging than a single user device." – Verizon DBIR, pg. 14
Findings by Industry
Instead of getting lost in the numbers, the report encourages readers to look at the data from the perspective of their own industry. As expected, threat actors, motives and attack patterns can vary significantly from one industry to another.
Accommodation and Food Services
Unsurprisingly, the accommodation and food services industry continues to be dominated by financially-motived point-of-sale (POS) breaches, accounting for 90 percent of all breaches within this vertical. Furthermore, 96 percent of malware-related breaches utilize RAM scrapers to stealthily collect credit card data. The DBIR also notes: “As evidenced by the great number of ‘integrity’ issues in our caseload, illicit software installation continues to be rampant.” Here's Erlin's thoughts on that finding:
"Illicit is a great term here because it covers both malicious and simply prohibited. It’s time for the industry to move from data integrity to Integrity Management. Used as a framework for understanding and managing risk, Integrity Management can drive down incident and improve risk mitigation."
Education
The education sector is frequently targeted with Denial of Service (DoS) attacks, especially now that online classes are becoming more commonplace. “Make sure you have adequate DoS protection against these attacks and an appropriate migration plan in place for when they do occur,” the DBIR recommends (pg. 30). Last year, the education industry was also highly targeted by the evolving W-2 scam. The DBIR explains it is not immediately clear why this scenario has figured so prominently in Education, but “it may be due to the more ‘open source’ nature of schools and universities.” To protect against this, it recommends conducting regular security training and having routine security audits.
Financial and Insurance
DoS attacks are also a top pattern for the finance and insurance industry, although attacks were not as rampant as in recent years. Regardless, the DBIR adds that, “while you are strengthening authentication into your applications, ensure that you have controls and response plans in place for availability attacks, as well” (pg. 31). Another interesting finding involves the type of data frequently compromised – banking information (13 percent) actually trails behind both personally identifiable information (36 percent) and payment card information (34 percent).
Healthcare
Healthcare is the only industry that has a greater insider threat than it does an external threat regarding data breaches. This is likely due to the fact that this vertical suffers from a large amount of human errors and employee misuse. As far as incidents, healthcare is nearly seven times more likely to feature a casual error than other industries. Additionally, ransomware accounts for a whopping 85 percent of all malware in healthcare. “Due to the ease of the attack, the low risk for the criminal, and the potential for high monetary yields, [ransomware] is likely here for a lengthy stay,” warns the DBIR (pg. 34). The report urges healthcare security practitioners to “ensure that policies and procedures are in place which mandate monitoring of internal Protected Health Information (PHI) accesses,” as well as to implement preventive controls that can help minimize the impact of ransomware on your network.
Information
Per the DBIR, this vertical includes everything from publishers, motion picture and sound recording industries to telecommunications, data processing companies and broadcasting. This industry was another top target for DoS attacks, accounting for more than half (56 percent) of all incidents. Web application attacks total 41 percent of breaches, and the use of stolen credentials is among the most common methods attackers use to gain unauthorized access.
"Implement a routine checklist for general security hygiene, and have sys admins make sure that the systems you build are built to deploy patches and updates in a timely fashion. Automate anything you can as this reduces the human error associated with many breaches we see. Conducting routine scans to discover misconfigurations before an adversary does." – Verizon DBIR, pg. 36
Manufacturing
This year, espionage motives fell slightly in the manufacturing industry, but it’s still a hot target for state-affiliated adversaries. Cyber-espionage made up 31 percent of all breaches in which nearly half of attackers (47 percent) sought to steal valuable intellectual property to gain a competitive advantage. Also noteworthy is the finding that 86 percent of breaches in this vertical are targeted. “Since, overall, the vast majority of attacks are opportunistic in nature, this finding underlines the point that criminals go after certain Manufacturing entities with a very specific purpose in mind,” the report notes (pg. 38).
Professional Services
In the professional services field, almost half of the breaches involved either phishing or pretexting and were financially motivated. There’s also a high amount of miscellaneous errors caused by employees, such as sending information to an incorrect recipient. Furthermore, in 60 percent of the cases, breaches are discovered by an external third-party. “We have seen numerous examples of POS breaches were the vendor didn’t establish some basic security controls on the assets, and neither did the client,” says the DBIR (pg. 40). “When it comes to protection of client data, whether in an IT services relationship or other service provider engagement, eliminate diffusion of responsibility wherever possible up front.”
Public Administration
Cyberespionage continues to be a major concern for the public sector and rightfully so. It was the motive for 44 percent of breaches in the field – over half of which were carried out by state-affiliated actors. However, public administration also has a prevalence of insiders as threat actors, trailing only behind healthcare. “Depending on the function, government entities may be targeted by state-affiliated groups, organized crime or employees. Keep in mind the type of data you handle and consider who might benefit from access to it and plan your security accordingly,” recommends the DBIR (pg. 43).
Retail
For retailers, web application attacks taking advantage of input validation weaknesses or stolen credentials were fairly common. DoS attack hits were also a major area of concern as they could potentially have serious consequences for retailers with an online presence, such as preventing transactions from being processed or slowing down the website or in-store systems. “E-commerce applications are a critical asset for retailers. Defenses against availability, as well as integrity and confidentiality losses, must be implemented, tested, and refined,” the DBIR suggests (pg. 46).
Conclusion
The DBIR wraps up by reminding us that cybercriminals will continue to leverage the tools that have previously proven to be the most effective against us. “Knowing where your organization is in the food chain for criminals gives you an advantage, so be sure to use it,” the DBIR concludes (pg. 47).
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

