
On January 7th, MITRE released ATT&CK for Industrial Control Systems, a taxonomy of real-world cyber adversarial behavior targeting ICS or industrial control systems. These systems operate critical infrastructure in manufacturing and utility industries, and they are popular targets in financial and espionage motivated attacks. Recent high-profile attacks on industrial control systems include the 2015 attack on the Ukranian power grid and the 2017 NotPetya campaign. The former is considered to be the first known successful cyberattack on a power grid, and the latter, a ransomware variant, targeted Ukranian energy companies, power grid, transportation systems, and banks before spreading globally with total damages estimated at more than $10 billion. Protecting ICS is particularly challenging because many legacy industrial systems were implemented with little or no attention to security or have unique characteristics that differentiate them from enterprise environments. As with ATT&CK for Enterprise, the framework can help security practitioners by establishing a standard vocabulary and body of knowledge for incident reporting, incident response, prioritizing defenses, defense gap assessment, adversarial emulation, and much more. Since the ICS domain is so distinct, MITRE has launched ATT&CK for ICS on a separate platform from ATT&CK for Enterprise for now. The distinction between ICS and enterprise IT environments follows the Purdue Reference Model, which contains a 5-level decision making and control hierarchy.
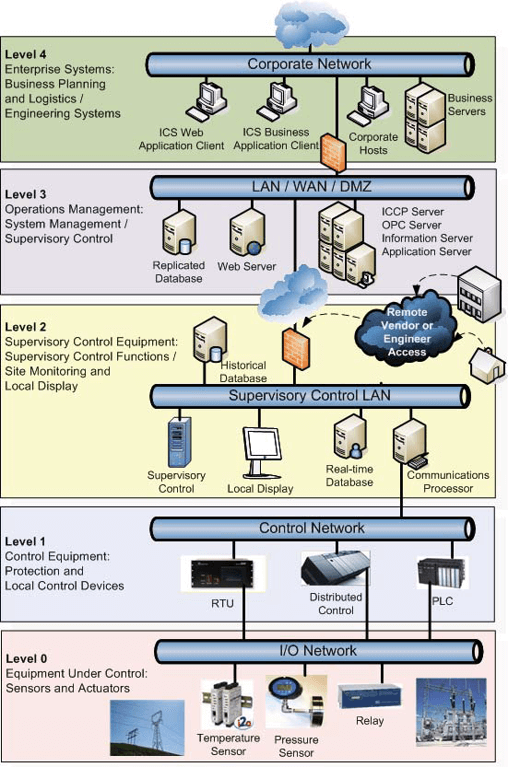
Levels 3 and 4 describe management and other business logistics systems within the enterprise IT environment covered by MITRE ATT&CK for Enterprise. The lower 3 levels describe systems that monitor, sense, and control physical processes along with the physical processes themselves, and these levels are the focus of ATT&CK for ICS. Compared to the 12 tactical categories of ATT&CK for Enterprise, ATT&CK for ICS has 11 tactics. Privilege Escalation, Credential Access, and Exfiltration are dropped, and Inhibit Response Function and Impair Process Control are added. And, while there is some overlap of the techniques between the two frameworks, ATT&CK for ICS is intended to describe behavior that targets industrial processes. Many participants and organizations, public and private, contributed or reviewed ATT&CK for ICS prior to launch. Given the success and popularity of ATT&CK for Enterprise, we’re looking forward to help ATT&CK ICS grow and mature. To learn more about the MITRE ATT&CK Framework, click here: https://www.tripwire.com/state-of-security/mitre-framework/mitre-attack-framework-what-know/
Tripwire ExpertOps
Elevate your organization's cybersecurity with Tripwire ExpertOps! Explore our managed security service now to ensure round-the-clock protection and expert guidance in safeguarding your digital assets.

