
An Israeli marketing company exposed more than 140GB of data by mishandling the credentials for an Elasticsearch database. A San Diego-based DevOps engineer who uses the Twitter handle 0m3n detected the disclosure after they grew tired of receiving text messages from "random phone numbers with similar messages containing links to gibberish domains."
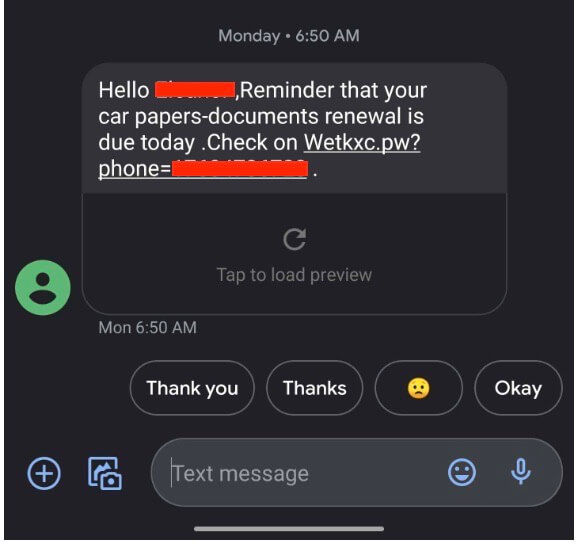
An example of an SMS marketing message received by 0m3n. (Source: ISMG) The engineer took a look and discovered a .env file on the web server of one of the domains referenced in the text messages. This file was a configuration file that pointed to an Elasticsearch instance. 0m3n learned that a set of plaintext credentials included in the file unlocked the Elasticsearch database. At the time of discovery, this instance consisted of two indexes that contained 140 GB of people's contact information including their names, phone numbers, email addresses and physical addresses. Data breach expert Troy Hunt analyzed the exposed data and said that it contained 49 million unique email addresses. He also found that 70 percent of those email addresses were already included in his Have I Been Pwned data breach notification service. A closer look at the Elasticsearch instance also uncovered the Laravel logs for an application developed by Israeli marketing company Straffic.io. Upon learning of the exposure, Information Security Media Group (ISMG) contacted Straffic.io and filed a report with Amazon Web Services. The latter confirmed on February 20 that the database had been secured. Straffic.io issued its own response just a few days after that. As quoted on its website:
We would like to bring to your attention that we have been reported that a security vulnerability has been found on one of the servers we use to provide our services. Following this report, we confirmed a weakness did exist and promptly patched it, in addition to fortifying our existing security protocols. As of now, all systems are secure and we did not find evidence of any data misuse or data loss. We continue to investigate and will notify if we find evidence to the contrary. Although we do our very best to protect the security of our service and deeply regret such a vulnerability has been found on our service, it is impossible to create a totally immune system, and these things can occur. We would like to express our gratitude for those of you who notified us, and ask that you help us keep our services safe.
News of this exposure comes approximately after eight months after a security researcher found a misconfigured ElasticSearch cluster that exposed over 90 million personal and businesses data records.

