
A new SMS-based phishing ("smishing") campaign is using the United States Postal Service (USPS) as a disguise to target mobile users. On September 15, SlickRockWeb CEO Eric JN Eliason tweeted out two examples of the operation. Both attack SMS messages claimed to contain important information about a USPS package. Using that lure, they attempted to trick the recipient into clicking on a link containing the domain "m9sxv[.]info."
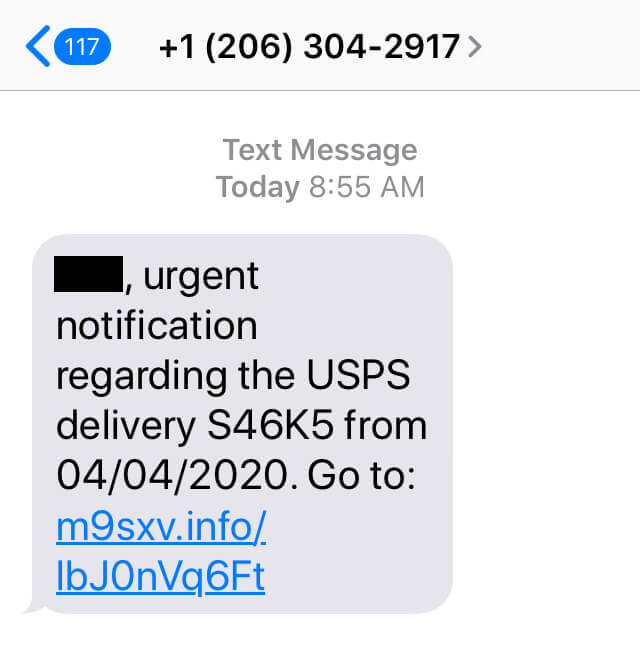
An example of the smishing campaign masquerading as the USPS. (Source: Twitter) Eliason decided to do some digging into the domain. He found that whoever was responsible for having registered it had done so on September 15. In the process, he also uncovered several individual smishing links using that domain. SlickRockWeb's CEO looked a bit deeper to see what happened if a recipient clicked on any of those smishing links. He observed that the links exhibited varying behaviors. In one instance, the link redirected the user to jtuzd.rdtk[.]io. Another led them to a fake casino game, while most others appeared to try to steal victims' credentials for their Google accounts. This smishing campaign isn't the first time that a delivery scam gained people's attention in 2020. Back in February, for instance, the U.S. Federal Trade Commission issued an alert warning users to be on the lookout for SMS messages that appeared to originate from FedEx. It was just a few months later when the Better Business Bureau published some guidelines on how individual users could avoid falling victim to a SMS-based delivery scam. Those recommendations included verifying the tracking information of an expected delivery and examining a link before clicking on it. Smishing is just one of the ways that malicious actors seek to steal users' credentials and/or infect their machines with malware. Acknowledging that fact, organizations should consider using ongoing security awareness training to educate their employees about some of the most common phishing attacks that are in circulation today.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

