
A new trojan leverages a fileless infection chain in that it never saves a file to the machine, thereby making analysis via a sandbox more difficult. It's unclear how the malware, detected by Trend Micro as JS_POWMET, initially arrives on a computer. Users could unknowingly download it from malicious websites. Alternatively, other malware could drop it onto an infected machine. Regardless of the download method, an autostart registry entry called "regsvr32" receives a URL as a parameter to fetch an XML file containing malicious JavaScript. This method enables regsvr32 to execute arbitrary scripts without saving the XML file to the computer. The autostart registry entry is capable of fetching the XML file from the malware's command and control (C&C) server every time the computer starts up. Upon execution, JS_POWMET downloads TROJ_PSINJECT, another file which runs as a Powershell script and connects to the website "hxxps://bogerando[dot]ru/favicon". TROJ_PSINJECT downloads an encrypted file named "favicon" at that location and injects it into its process using ReflectivePELoader. The malware then decrypts favicon using a hardcoded RC4 key so that it can load up its final payload. Michael Villanueva, a threat research engineer at Trend Micro, details this process in a blog post:
"Favicon will also be decrypted using the aforementioned RC4 key, resulting in a malicious DLL file known as BKDR_ANDROM (Detected by Trend Micro as BKDR_ANDROM.ETIN). Again, this part of the process is also fileless; the file will not be saved into the machine but rather injected into the powershell.exe process. All of these routines will be executed by the malware using PowerShell commands."
For the infection chain's last phase, BKDR_ANDROM terminates powershell.exe if it finds it running on the system, collects information about the computer, and executes the final payload, which in this case is some of its common routines. But that might not always be a case. Malware authors could always substitute in other malicious programs for their final payload.
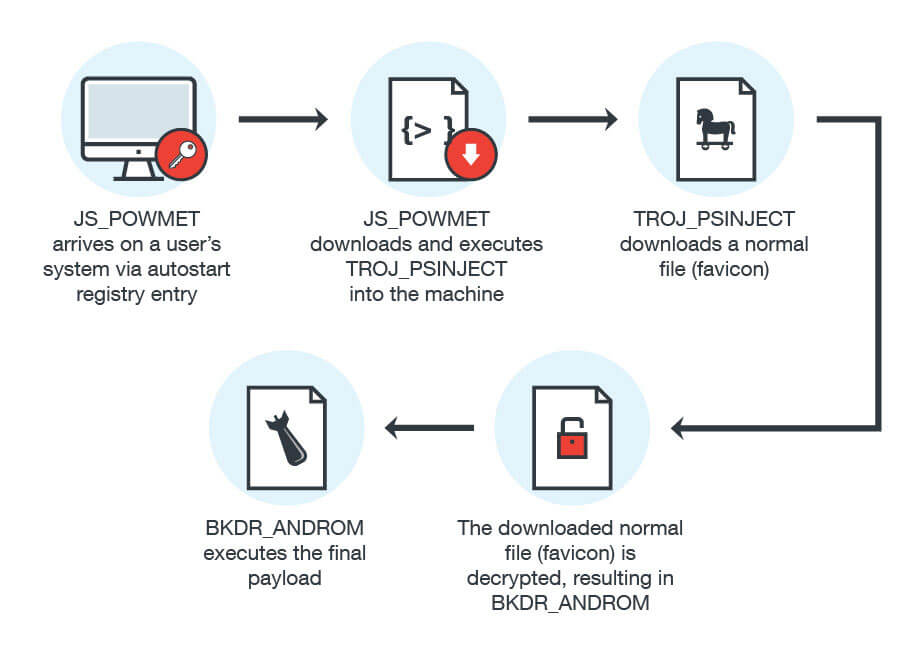
JS_POWMET infection Diagram. (Source: Trend Micro) To protect against fileless malware like JS_POWMET, organizations should consider segmenting their networks in order to limit access to critical infrastructure and look into disabling Powershell if they don't use it. They should also be on the lookout for stealthy, less obvious malware. These baddies may be "fileless," but if they are designed to persist on a machine for period of time, most leave a trace of their presence somewhere on disk. For more thoughts on the reality of many fileless malware, please read this article.

