Early February is when Red River College puts on its Directions conference, which I attended twice as a student. The purpose of this conference is to connect students and businesses and to assist the former in the transition from student to professional. This year, I had the privilege to speak about my journey of starting out with little experience in the Information Technology field. https://twitter.com/InfoSecPlaya/status/698258193340882946 Beginning a new career can be an intimidating and frustrating endeavor. You begin by looking for entry-level and junior positions; even those jobs require some level of experience! This is the chicken and the egg question or a catch-22. How are you supposed to have experience when you're just starting your career? How will you prove you have the skills necessary? What differentiates you from the next candidate? Another challenge is the fact that no one knows who they are. A lot of technology jobs aren’t advertised online but are spread via WOM (word of mouth). Unfortunately, meeting new people outside of school can be extremely difficult if you aren’t sure where to start. I spoke with a few friends from my Twitterverse community to see what they had to say on the topic:
“The biggest challenge I’ve had when starting out is comparing myself to those that have been around much longer. It always led to a mental uphill battle when it came to learning, and I felt like I was absolutely terrible at my job. It seems insurmountable, but staying curious and taking things one at a time helped me to get where I am today.” – @Agnu
Starting out can be challenging and scary. It’s hard to see others so far along and to not get lost in trying to translate how they got from point A to point B. You may not be 100% confident in your abilities yet, and you might not really know how to learn more. This brings me to another very common challenge (especially among professional women) in the IT and other fields: dealing with "Imposter Syndrome." One of my close friends, @da_667, who is well respected in the community, mentors many people in IT, including those who are just starting out, as well as those who are already successful. Da truly is impressive, so it might come as a surprise that he deals with Imposter Syndrome continuously. Imposter Syndrome is not actually based on your abilities, it can affect anyone from those starting out to those who are better established.
“Imposter Syndrome is best described as a feeling of deep inadequacy with your current level of skill; as though you just don't measure up to your peers. Sometimes, it's punctuated with a feeling of inadequacy, other times it may be punctuated with a feeling of listlessness; 'What's the point if everyone is better at this than me?'"
You'll see your peers doing awesome things and sharing their knowledge, and you'll think, "I didn't know /any/ of that. Am I really fit to be here?" Y'see, the thing about infosec, IT or any particular career in general is that there are so many different areas of specialization that being a master in every aspect is impossible. If you're a jack of all trades, you are certainly a master of none.
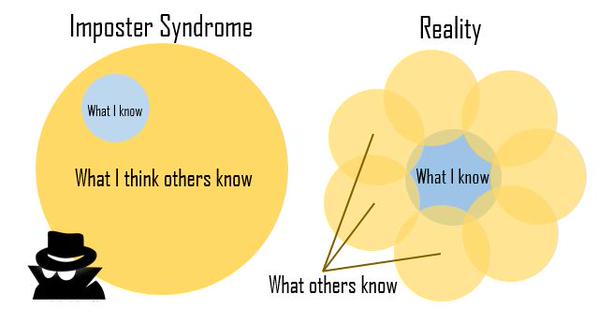
You aren't as inadequate as you think; you just see others' focus/talent down one particular specialization and assume that they know everything there is to know about a subject, that their knowledge dwarfs yours and that you'll never be their equal. But that's just not so. The reality is that each of us has a particular specialization in our fields that we gravitate towards, and it is only through sharing knowledge (blogs, white papers, articles, conference talks, etc.) that the entire picture is unveiled. Take me, for instance. My specialization is rule-based IDS/IPS (Snort), with some skill in other NSM functionality (flow monitoring, full packet capture, and anomaly monitoring like BRO). I also have some modicum of skill when it comes to malware analysis tools and mining Open-Source threat intelligence. I don't know the first thing about appsec (my programming skill is rudimentary at best), I know next to nothing about reverse engineering (trying and improving on this), and while I understand the concepts of penetration testing and adversary emulation, I've never held a position as a penetration tester in my life. But I go to conferences, I read articles/blogs/tutorials and I engage others in the community. I learn through their experiences in their specializations, and I make myself a little more well-rounded as a result.
"If you're suffering from Imposter Syndrome, I just want to tell you that you aren't as clueless as you seem. Even if you're new to Infosec, there is likely some view or some perspective you bring that makes the knowledge that you share unique. Take your time, find your niche, and share your knowledge with the world.” – @da_667
https://twitter.com/alisdairdaws/status/698254938795716608 Although going to school isn’t the only option, I know for me it was a huge part of forming who I am today. Even so, I still have my struggles. I continually deal with Imposter Syndrome. I feel great one second, but then the next, I feel like I’m faking it. Especially when I’m reaching further and trying more challenging things. It is extremely beneficial to challenge yourself, but it can be hard on your confidence when you fail. And you will. Any time you’re in a job that comes easily, for me, it’s time to move on. When I was working at Lazer Grant LLP, the accounting firm I started out with, I realized I enjoyed the IT department but felt like there was so much I was missing to be able to move forward. I chose to go back to school and in January 2013, I entered the Business Information Technology program at Red River College. This program looked at many different parts of Information Technology, including programming, web development, Cisco networking academy, system administration, communications, basic accounting, network management, database management, entrepreneurship, and more. It gave me a solid foundation of knowledge that I now can use to continue learning. Additionally, there is that little paper that proved, to me, I knew what I was talking about. Working in a professional atmosphere doesn’t always mean you instantly get along with everyone, the ‘soft skills’ rarely come naturally, especially in this sort of field. Jimmy Vo (@JimmyVo) did a talk back in 2014 at BSides Asheville entitled "How to Win Friends and Influence Hackers." It was an interesting look at working with both extroverts and introverts. He discussed different ways for interacting with either personality type, methods on how to build your brand, and more.

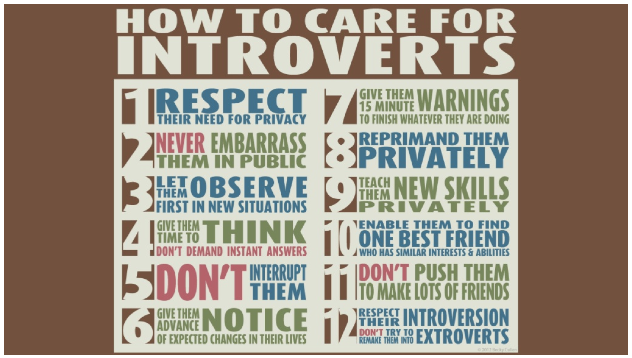
[ How to Win Friends and Influence Hackers by Jimmy Vo, BSides Asheville 2014 ]One thing you should note is this: who are you in that scale? I recently purchased a book called Emotional Intelligence 2.0, which looks at how you can interact with others and respond to situations. You take a test before reading the book that initially examines how you respond to a situation. Then, after giving you some tips on better ways to understand things, you retake it and see how you’ve improved. Knowing how you are going to react to situations can help you address places you want to improve or know others you don’t need to worry about.
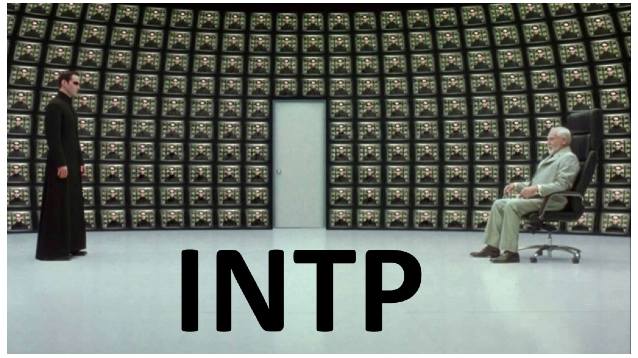
[ How to Win Friends and Influence Hackers by Jimmy Vo, BSides Asheville 2014 ]This includes knowing your ‘personality’ type. Take note that this can and does change. Before college, I was highly introverted, but during college, I scored much higher on the extrovert side. Now a year after I’ve graduated, I’m more in the middle. The most recent test I’ve taken gave me INTP. I know that I can be very logical in my thought process, but I know I lack emotional understanding now and then, which just means I should take extra notice on that. Another member who is starting their journey into the InfoSec community makes his point on what making a mark really means to him:
“Making my mark in IT and more specifically Information Security has proven incredibly tough, and I still have not reached the point where I feel I have made my mark. However, ongoing projects, ideas, and collaborations with people from the InfoSec community has been pushing me further. Making your mark also depends on how you specifically want to impact IT, and I believe that people have different milestones in mind for when they consider their mark made. Some people may want to be well recognized and popular in the IT community; others may just want to release a tool they have in mind; still others may just want to reach a point of where they can then start teaching newcomers in the IT community. All of these are great ways to engrave your presence in the IT community. Personally, I conducted a lot of research into malware analysis and started to hunt malware before posting those findings on my Twitter account. Doing this started to get me some attention from the InfoSec community, and I started to build connections, which is exactly what I wanted. "I love the InfoSec community, but making my entry felt rather rough. This is because when you say you work in IT, many people assume you know everything instantly. When you run into an issue you might ask for help and receive the 'you don’t know that?' response, or you are in fear of that response and therefore don’t want to ask. Obviously this is an issue. "We work in information security, so our end goal is to work together to design new technologies, processes, and methodologies that will ensure the safety of our data. We are here to beat 'cybercrime,' so we really need the entire information security community to band together. As our end goals are similar, I would say creating more of a community is what will really set us up for success. Whether you are just starting out or are a veteran of InfoSec, I believe that each of us needs to work hard to collaborate to make a difference in the world. "Just to restate; you are never really finished learning and pursuing new things. Work hard at your goals but remember it isn’t a simple walk in the park. You can ask for help; we are a community, and you should utilize the contacts you make. Also don’t feel bad about not being in the place you want to be right away. It takes time, and everyone struggles once in awhile. We’re here to help.” – @sudosev
Sev’s commentary above reminded Agnu of another point:
“Its super important to never brush off any question, no matter how dumb you may think it is. You don’t know other people’s backgrounds, and that question might fill in a key piece of knowledge that lets a lot of other pieces click into place."
This is a very important thing to note. Think of the phrase "There are no stupid questions." I do believe there are questions that are not helpful, but when someone is trying to learn, they might not pick up every piece right away. As mentioned above, we all come from different backgrounds but we all learn differently, as well. IPv6 addressing seems logical to me, as do subnetting and summary addressing, but to many techs out there, they honestly do not understand what IPv6 is all about. We want to create a community where others are not scared to ask questions, an environment where when they do ask questions, they can get informative and correct answers. I would like to leave you with some space to think about your ‘personal brand.’ This is the image you are giving out in the world, how others perceive you before you have had the chance to meet. It is extremely important to give off the best image possible and always remember context is not easily seen, especially over text-based conversations. https://twitter.com/jessysaurusrex/status/692731455160463361 To learn about some of the jobs that await you in IT, particularly in information security, please click here and here. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc. Title image courtesy of ShutterStock

