It was 1977, and soon-to-be-fans were greeted with a masterful score and scrolling text. Darth Vader and Princess Leia share the screen in those opening moments, and the Star Wars universe was created. Nearly 30 years later, a new film would introduce us to the events immediately preceding the “scene that launched a franchise,” but how did things get to be this bad? How was it that the Emperor and a half-man, half-machine atrocity named Darth Vader were able to create such a dire situation? If you are willing to accept that Episodes I, II, and III exist, then you may have an explanation, but many don’t feel those are a part of the true franchise world. Jar Jar Binks was like the Slapchop, a horrible idea that some people love. Whether or not you consider those first three episodes to be a part of Star Wars canon, the question still remains, “Why were things that bad?”
Darth Vader was more IoT than man
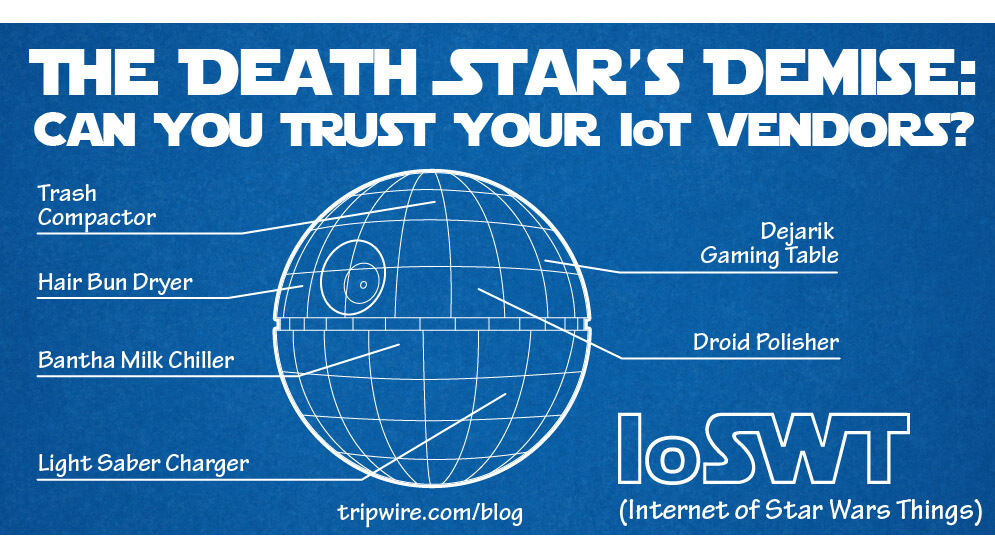
The downfall of the Republic is upon us. It wasn’t “a long time ago in a galaxy far, far away” - it’s here and now. The Emperor rose to power as people became lazy and weak, preoccupied with the Internet of Things (IoT). Consider this: Darth Vader was more IoT than man. Today, we’re embedding RFID in our hands and getting QR Code tattoos; tomorrow, we’re breathing loud and speaking like James Earl Jones. Remember Luke practicing with the training remote on the Millennium Falcon? Is that really much more than an impressive extension of the Wii U? Ultimately, the Lightsaber handle is not unlike the Wiimote. Dejarik was a fancy version of IoT-enabled Chess. The most obvious example of IoT in A New Hope was the trash compactor. This simple device designed to compact your trash in order to save space was network connected. Ask yourself, why would you ever need remote network access to your trash compactor other than to save someone from being crushed? This trash compactor is not unlike the IoT-enabled light bulbs and slow cookers of today.
The Death Star's Demise
We’re adding fancy capabilities to devices that don’t need it and allowing tiny beeping robots (and malicious hackers) to manipulate these devices due to a lack of security and access control. While R2D2 was a hero to the viewers, he exploited plans detailing a massive security hole in the Death Star that would have been prevented with proper access controls. R2D2 may have been one of geek cultures earliest on-screen hackers.
A backdoor left behind by an angry designer ultimately defeated the Death Star. Insider threat is just as real for IoT systems as it is for a planet-killer like the Death Star. Many of these pieces of hardware come from unknown companies and malicious individuals; lazy and incompetent developers often plague the remaining product lines. While many people say that IoT needs proper security and controls (and it does!), there’s something even more important – IoT needs to be limited. Every new IoT device we add to our environment increases our attack surface and expands our network footprint. So ask yourself, do you really need a WiFi connected light bulb? Is it important that your phone beep when your slow cooker reaches temperature? These are nice to have features, but they aren’t necessities. We’ve reached a point where we’re dependent on these devices, if this isn’t a precursor to the rise of the Empire and fall of the Republic; it’s likely foreshadowing the reality of The Terminator. The ultimate path to security is to take a minimalist approach. Eliminate anything that isn’t needed. When that is done, disconnect anything that is seldom used... if no one complains, it isn’t needed. Then you can focus on immediate security concerns. The lessons of Star Wars are lessons of a minimalist approach where you use only the tools you need. No blasters are needed for a Jedi to accomplish their task. Only a basic Lightsaber. This minimalism is something everyone in information security should aspire to achieve. Star Wars: A New Hope should be mandatory viewing material for all new IT and IS employees, a reminder that the Force may be a powerful tool when wielded by a master but that it doesn't stand a chance next to backdoors, unpatched vulnerabilities, and malware. #MayThe4thBeWithYou
Zero Trust and the Seven Tenets
Understand the principles of Zero Trust in cybersecurity with Tripwire's detailed guide. Ideal for both newcomers and seasoned professionals, this resource provides a practical pathway to implementing Zero Trust, enhancing your organization's security posture in the ever-evolving digital landscape.

