
Security researchers are warning of a new wave of phishing emails which are using an unusual disguise in their attempt to both bypass scanners at email gateways and dupe unsuspecting users. The attack arrives in users' inboxes in the form of an email purporting to be a notification about a voice message using subject lines such as "PBX Message," "Voice:Message" or "Voice Delivery Report."
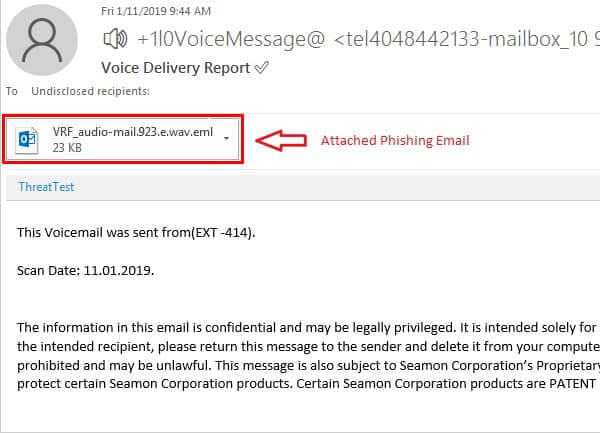
The attackers are banking on recipients' curiosity to find out who they might have missed a voice message from and what it might contain. Attached to the email is... an email in the form of a .EML attachment. As researchers at EdgeWave point out, although many users are very comfortable with the idea of forwarding an email, they may be much less familiar with the notion that emails can actually be sent as an .EML attachment and then opened by email clients. Furthermore, says Edgewave, it's quite possible that many companies have put measures in place to block dangerous attachment types but not taken such steps against .EML files because... well, they're email! If you were to click on the attached .EML file it will be opened by your email client and display an email message that pretends to come from RingCentral, a cloud-based platform for business phone system.
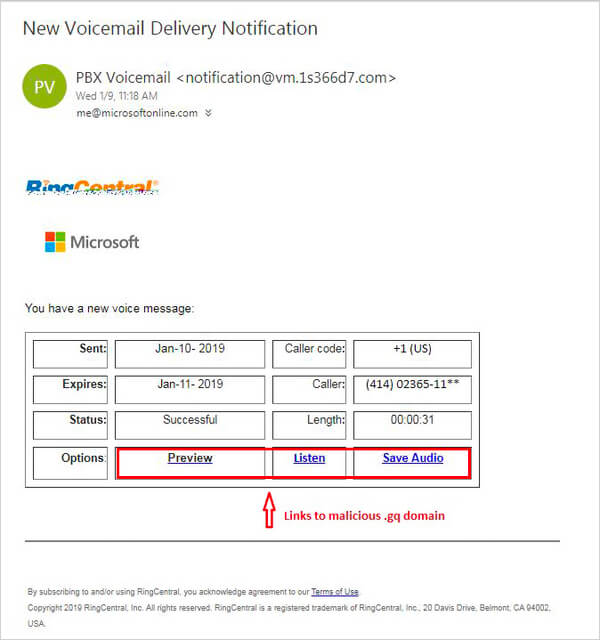
In an attempt to trick the targeted user into believing that they have received a delivery notification about a voicemail, the emails list bogus information about the call including the time it was made, how long it lasted, the caller's country code and a partially redacted caller's number. To make the message more convincing still, it appears as a preview within Outlook rather than as content in a separate window. The criminals who launched the campaign are hoping that all this will be enough to dupe unsuspecting users into clicking on the "Preview," "Listen," or "Save audio" links to hear the mystery message. As Bleeping Computer reports, users who click on the links are taken to a bogus Microsoft account login page that asks for credentials to be entered. Interestingly, the phishing page tells anyone entering their password that it is incorrect on the first occasion and then prompts them to renter the information. One possibility is that the attackers are aware that some users deliberately enter their password incorrectly when they are suspicious of a login page. Some users believe that deliberately entering their password incorrectly on the first attempt is a good way to spot if they might be being phished or not. Their thinking is that if the page accepts their deliberately-incorrect password then it must be bogus. This attack, however, proves that you would be unwise to rely on this practice to protect yourself. It's also possible that the double-entry of passwords is being requested in order for the fraudsters to have greater confidence that they have received the correct password for an account. Once a password has been entered by the targeted user for a second time, they are taken to a webpage containing an actual voicemail. The voice message is not intended for the recipient and is seemingly innocuous. The recording shared by Bleeping Computer, for example, appears to have been left by an elderly British woman identifying herself as "Eileen's cousin" who is "calling to find out how she is." Of course, it's perfectly possible for the criminals to switch the message played at any time.) A voicemail like that can be safely ignored, but what shouldn't be shrugged off quite so easily is that the user has just shared their email address and password with a hacker. Even if their Office email account is protected with two-factor authentication, they might have made the common mistake of reusing those same login credentials for other online accounts, thereby opening opportunities for hackers to breach systems and steal private information. Always be wary of unsolicited email attachments. If in doubt, get your IT security team to check it out.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

