
Security researchers have identified a new phishing scam that is targeting customers of the popular accommodation booking site Airbnb. Christopher Boyd, a malware intelligence analyst at Malwarebytes, says he recently discovered an email phishing campaign impersonating the company and redirecting users to a fake Airbnb login page in an attempt to compromise users’ credentials. “The page asked visitors to ‘Login with your Airbnb account,’ offering them username and password fields to fill out,” explained Boyd.
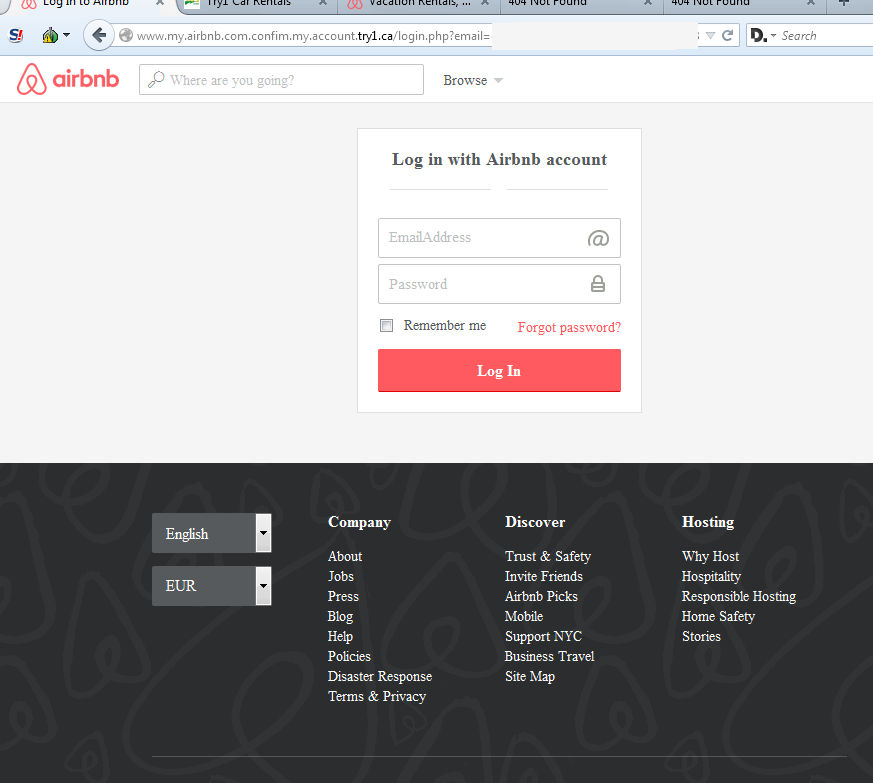
Source: Malwarebytes He noted that the URL bar did not contain HTTPS – or a green padlock icon – which indicates a safe, encrypted connection. Furthermore, the extremely long URL was another indicator that the site was suspicious: my(dot)airbnb(dot)com(dot)confim(dot)my(dot)account(dot)try1(dot)ca/login(dot)php The researchers revealed that the fake Airbnb login page was being hosted on a compromised car rental service website, which has since gone offline. “The only ‘genuine’ part of the URL is the bit highlighted in bold because that’s the main URL of the car rental service,” said Boyd. The rest of the long string of words is part of the scam, which could be troubling for mobile users, as the bulk of what they’d see would likely be hidden off the right of their small screen, he said. After entering their login details, visitors are shown the following ‘Thank You’ page, and are redirected to the genuine Airbnb website.
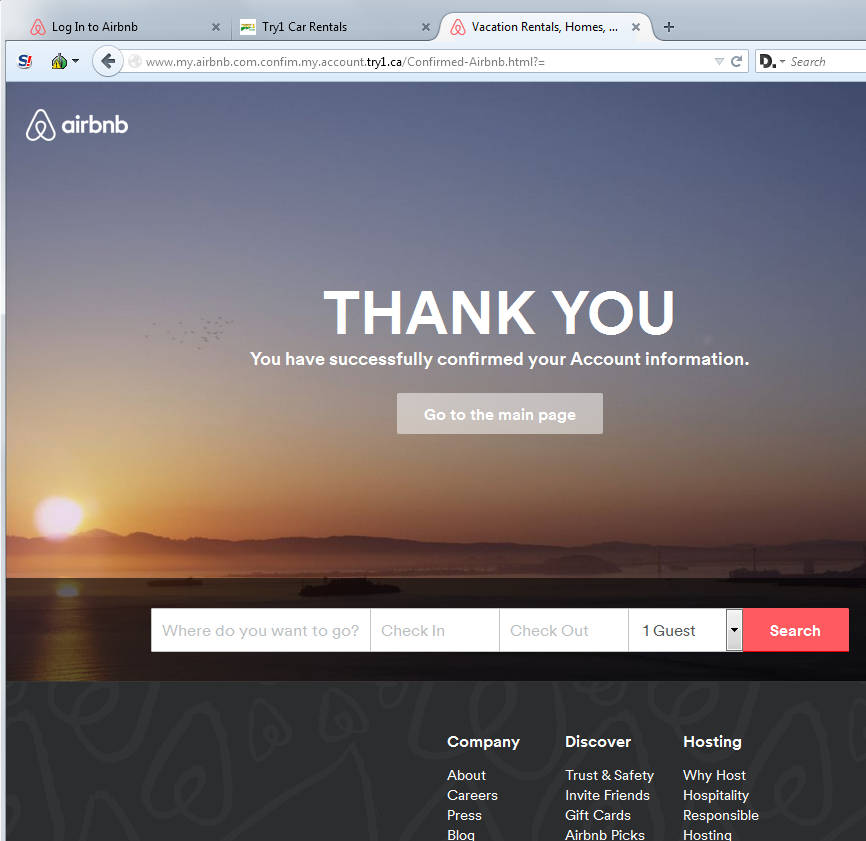
Source: Malwarebytes Scammers have plenty of options after successfully hijacking an account, especially those that are verified and have obtained stellar reviews, making it easier to lure potential victims into paying in advance in order to secure their rental.
“The sky’s the limit in terms of how you can try and part people from their money (and all too often, there’s no way to get it back,” Boyd said.
“This also means that the owner of the phished Airbnb account has a major reputation hit to deal with … after any initial money grab, which could cause some long-term headaches,” Boyd added. For helpful tips on how to protect yourself against phishing scams, check out our article here.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

