
A ransomware attack campaign based in India has caused millions of dollars of damages after infecting three banks and a pharmaceutical company. The research team at Malwarebytes has identified LeChiffre, whose name means "encryption" in French, as the malware responsible for the attack campaign.
"It is different than most of the ransomware present nowadays," Malwarebytes comments in a blog post. "Instead of spreading to users and automatically infecting their machines, LeChiffre needs to be run manually on the compromised system. Common scenario of infection is that attackers are automatically scanning network in search of poorly secured Remote Desktops, cracking them, and after logging remotely they manually run an instance of LeChiffre."
This property suggests that the Indian companies must have been hacked at some point in the past, thereby allowing the attackers to regain entry into the compromised networks in order to run LeChiffre. The ransomware's encryption process works by encrypting both the first and last 0x200 (8192) bytes of a file, after which it appends a 32-bit content that is likely the AES key or initialization vector. The binary is also packed by UPX and written in Delphi.
"LeChiffre looks very unprofessional," concludes the team at Malwarebytes. "Code has been written in Delphi and packed by UPX – practically, no countermeasures against analysis has been taken. It can be justified by the fact, that this ransomware was not intended to be distributed in campaign, only used by attackers after they entered to the system. However, poorly implemented encryption and model of communication with victims (via e-mail), shows that this malware has been prepared lazily, probably by beginners."
Even so, LeChiffre has still managed to cause some damage. Earlier in January, attackers sent a fake email to the IT admins of several high-profile Indian targets, reports SPAMfighter. The personnel at three banks and one pharmaceutical company took the bait, allowing the ransomware to infect their computer as as well as several other company-owned PCs. Upon successful infection, each victim received a ransom note that urged them to contact the attackers via email and hand over 1 Bitcoin ($400) for the decryption key to each computer, writes Softpedia.
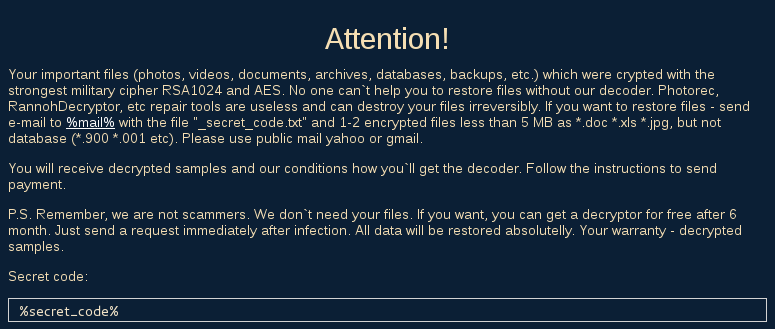
The LeChiffre ransom note (Source: Malwarebytes) A few of the companies have already paid the ransoms, which according to The Economic Times have climbed into the millions of dollars. This campaign marks the first instance in which malware-based attackers have sought Bitcoin ransom payments from victims located in India. Without a doubt, it will not be the last. For information on how you can protect yourself against ransomware attacks, please click here.

