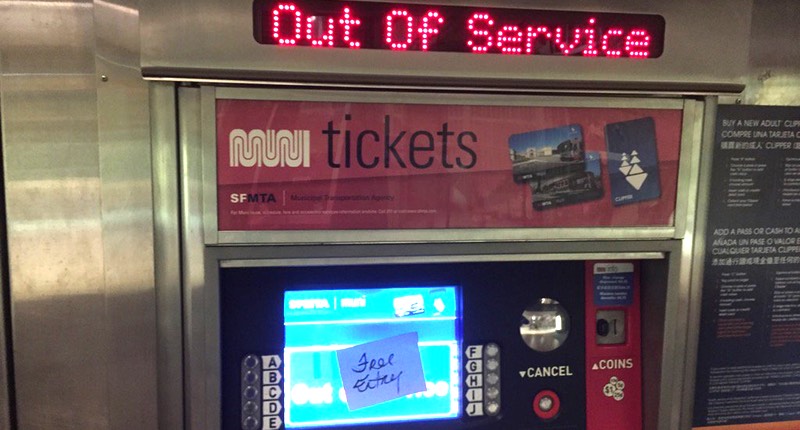
San Francisco's transport system, known as Muni, was hit hard by a ransomware attack this weekend that forced the network to offer free rides to passengers. More than 2000 systems at the public transport agency are believed to have been hit, including Windows workstations, servers and ticketing machines. The first many users would have known that their computer was infected would have been on boot-up, as the modified MBR displayed a stark ransom demand:
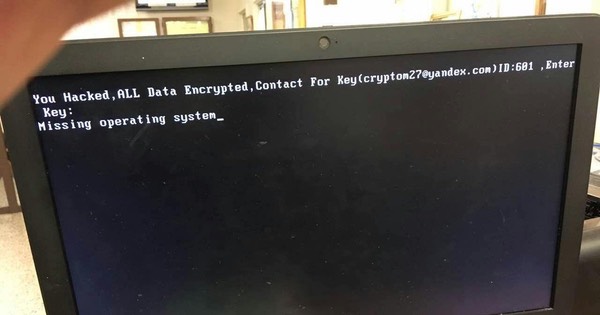
"You Hacked, ALL Data Encrypted. Contact For Key([email protected])ID:681 ,Enter."
Despite the attack, the Muni rail and bus network continued to run, but with passengers allowed to travel for free. The ransomware, which is thought to have struck on Friday afternoon, is a variant of HDDCryptor, that uses freeware and open source tools to encrypt hard drives and network-shared files, and overwrite the master boot record (MBR) on infected computers. Inevitably, the attack and its consequences has made for news headlines and TV reports, but it seems quite possible that the San Francisco Municipal Transport Agency (SFMTA) was not specifically targeted by the extortionists. Instead, it's very believable that the transport system was an unfortunate chance victim in the way that many individuals and companies fall foul of ransomware every day - by opening a malicious email attachment, visiting a boobytrapped website, or downloading a malware-infected file. When journalists at the SF Examiner contacted the email address displayed on infected computers, the alleged attacker claimed that an SFMTA employee downloaded an infected torrent file. By Sunday it appears that ticketing systems were returning to normal operation, and passengers were once again expected to purchase travel tickets. Journalist Steve Ragan of CSO Online was successful in getting the extortionist to send him his demand:
if You are Responsible in MUNI-RAILWAY ! All Your Computer’s/Server's in MUNI-RAILWAY Domain Encrypted By AES 2048Bit! We have 2000 Decryption Key ! Send 100BTC to My Bitcoin Wallet , then We Send you Decryption key For Your All Server's HDD!! We Only Accept Bitcoin , it’s So easy! you can use Brokers to exchange your money to BTC ASAP it's Fast way!
At the current exchange rate, 100 Bitcoins is equivalent to over US $70,000. However, there is no indication that SFMTA has paid any ransom, and it's perfectly possible that SFMTA would be unwilling to give in to the extortion for fear that it will only encourage more attacks in future. One hopes that the organisation has an effective disaster recovery strategy that means they are able to recover from clean backups in a prompt fashion and bring systems back to full working order. One thing is clear about such a high profile attack. Law enforcement agencies will be keen to bring whoever was responsible to justice, and the attacker - wherever they might be in the world - might be regretting that their random ransomware victim will result in such attention being shone on them. I have no doubt that the authorities are already investigating, and questions will be being asked as to how Muni's systems could be better protected from future internet attacks - which could have much more serious consequences. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

