
A US court has sentenced a programmer to 30 months in a federal prison in connection with software that claimed to be a legitimate tool for Windows sysadmins to remotely manage computers, but was actually used by criminals to backdoor PCs and secretly spy on victims. 21-year-old Colton Grubbs, of Stanford, Kentucky, admitted earlier this year that his software, LuminosityLink, was used for illegal surveillance and remote access of computers without the victims' knowledge and consent, had actively marketed the software as a remote access trojan (RAT) to criminals, and provided support and assistance to his customers via sites such as HackForums.
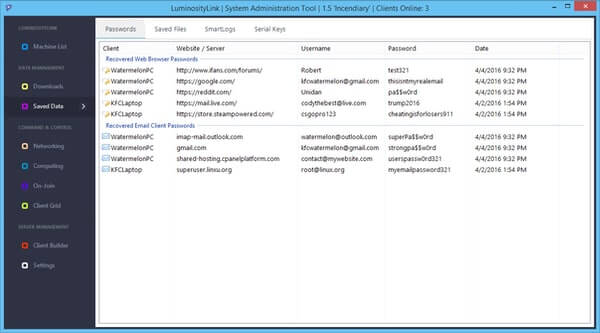
Having bought the software, purchasers could either trick targets into installing the software (perhaps by sending them an enticing email with a malicious link), or - in the case of jealous spouses and business rivals - quickly plant it themselves if they gained temporary access to their intended victim's PC. Once in place, the LuminosityLink program allowed remote hackers to record victims' keystrokes, spy via a users' webcam and microphone, steal files and passwords, exploit compromised computers' resources to mine for cryptocurrency or launch distributed denial-of-service (DDoS) attacks, and avoid detection by anti-virus software. Law enforcement agencies became aware of crimes facilitated by LuminosityLink, and began to investigate - which ultimately led police to Grubbs. Grubbs, however, realised that his apartment was likely to be searched. He hid a debit card associated with his Bitcoin account and phone containing his Bitcoin wallet information, took incriminating hard drives off the premises, and gave his laptop to a housemate, so that it could be concealed in the roommate's car. In addition, Grubbs contacted a PayPal user collecting payments for LuminosityLink (he himself had been banned from the platform for selling malware) and told him to hide evidence. These, it could be argued, are not the actions of someone who believes that their software is a legitimate system administrator tool. The LuminosityLink RAT was sold for $39.99 to more than 6,000 customers around the world via a professional-looking website.
And it was that professional-looking website which played a part in Grubbs's undoing, with its promotional text attempting to pull off the difficult feat of both claiming that LuminosityLink was a legitimate administration tool while also emphasising its list of malicious features. "Our modern society is dependent on computers, mobile devices, and the use of the internet," said Robert M. Duncan, Jr., United States Attorney for the Eastern District of Kentucky. "People simply have to have confidence in their ability to use these modern instruments to transact their business, privately communicate, and securely maintain their information. It is essential that we vigorously prosecute those who erode that confidence and illicitly gain access to computer systems and the electronic information of others. Everyone benefits when this deceitful conduct is discovered, investigated, and prosecuted." Grubbs has been ordered to forfeit the proceeds of his crimes, including the princely sum of 114 Bitcoins (currently worth more than US $725,000) seized at the time of his apprehension by the FBI. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

