
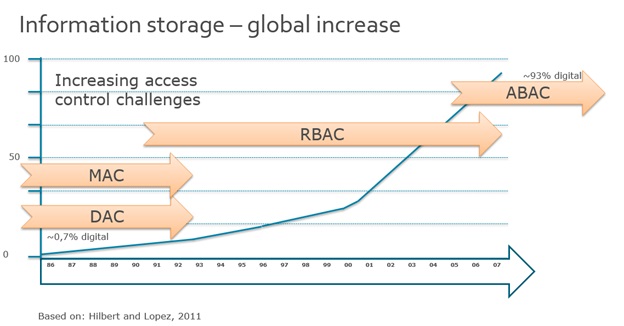
Historically, access control has been based on the identity of a user requesting execution of a capability to perform an operation (e.g., read) on an object (e.g., a file). This was done directly either as in Discretionary Access Control or Mandatory Access Control or through predefined attribute types, such as roles or groups assigned to that user as in Role Based Access Control or RBAC. While all three of these access control methods were capable and important for their time, times have changed. Based on the Hilbert and Lopez assessment of global information storage over time, this graph shows how the sum total of stored information has increased in the time span 1986 to 2007. The interesting part is not only the overall increase but also how information increasingly is stored digitally. In 2007, 97 percent of the assessment showed that some 93 percent of the information was stored in some kind of digital format – as opposed to less than 1 percent in 1986. With the amount of information stored digitally, there is an increasing need to secure that data and allow access to the appropriate individuals.
Traditional Security vs Identity Security
With the increase in digital data that is stored, it also causes an equal increase in data that is shared. The ability to access data anytime and from anywhere has created a need for business to change the way they secure data—no longer is network security sufficient. We must transform from the traditional security approach to an Identity Security approach, where the security is not defined based on where you are located (inside the firewall or outside), but who you are – your Identity. With the average person carrying 2.9 devices in 2013, demands are on businesses to secure data on devices where traditional access control models do not apply. To enable and adapt to the changing demands of users, businesses must transform the enterprise from a security of No to Know. We must be able to enable the business to access the information and apply correct security, so it is only accessible by the appropriate individuals. A system is required to make Access Control decisions without previous configuration of the entitlement by the end user or knowledge of the end user by the administrator. By relying upon the concepts of user and object attributes consistently defined between organizations, Attribute Based Access Control avoids the need for explicit authorizations to be directly assigned to individual users prior to a request to perform an operation on the object. Moreover, this model enables flexibility in a large enterprise where management of access control lists or roles and groups would be time consuming and complex. Leveraging consistently defined attributes that span both users and entitlements, authentication and authorization activities can be executed and administered in the same or separate infrastructures, while maintaining appropriate levels of security. This method of Access Control has made Gartner predict, “By 2020, 70% of all businesses will use ABAC as the dominant mechanism to protect critical assets, up from 5% today.”
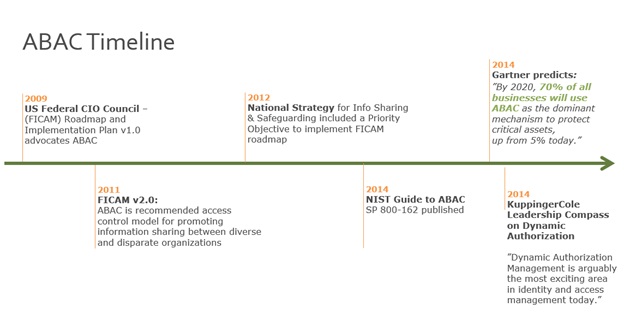
We can see as far back as 2009 that the shortcomings of current Access Control methods where becoming evident. This leads to the FICAM V2.0 in 2011, which advocates ABAC as the recommended Access Control Model. ABAC has been defined in different ways. For instance, one early paper on web services mentions that ABAC “grants accesses to services based on the attributes possessed by the requester” (L. Wang, D. Wijesekera, and S. Jajodia, 2004). While a debate of security in geographic information systems describes ABAC as a method in which “attribute values associated with users determine the association of users with privileges” (I. F. Cruz, R. Gjomemo, B. Lin, and M. Orsini, 2009). However, an additional paper recaps ABAC as a model that is “based on subject, object, and environment attributes and supports both mandatory and discretionary access control needs” (E. Yuan and J. Tong, 2005). In these and other definitions, there is a practical consensus that ABAC defines access by matching the current value of user attributes, object attributes, and environment conditions with the requirements specified in corresponding access control rules.
With the demand on businesses today to expand their reach to partners, customers, and contractors, it has become import for an access control system to expand to meet those growing needs. ABAC methods will allow an unparalleled amount of flexibility and security while stimulating information sharing between diverse organizations. It is vital that these capabilities be developed and deployed using a common foundation of concepts and functional requirements to ensure the greatest level of interoperability possible. ABAC is well suited for large enterprises. An ABAC system can implement existing role-based access control policies and can support a migration from role-based to a more granular access control policy based on many different characteristics of the individual requester. It supports the external (unexpected) user and provides administration that is more efficient. However, an ABAC system is more comprehensive, and therefore may be more costly to implement and maintain, than current access control systems. To explore this topic in more depth please attend my presentation at BSidesSLC March 20 and 21 in Salt Lake City. We will discuss why businesses today need a more comprehensive access control model to protect them from increasing threats while driving growth and revenue for their business.

About the Author: Adam Fisher is a Principal Consultant with CA Technologies whose qualifications include CISSP Certification, a Bachelor of Science Degree in Information Systems and a Master of Business Degree in Information Technology Management; a detailed knowledge of IDAM technologies and best practices, and successfully lead projects at 4 of the top 5 banks in North American and Europe. Ten years of experience in the creation and deployment of solutions protecting networks, systems and information assets for diverse companies and organizations throughout Europe and North America. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Title image courtesy of ShutterStock
Zero Trust and the Seven Tenets
Understand the principles of Zero Trust in cybersecurity with Tripwire's detailed guide. Ideal for both newcomers and seasoned professionals, this resource provides a practical pathway to implementing Zero Trust, enhancing your organization's security posture in the ever-evolving digital landscape.

