
In March 2022, the Payment Card Industry Data Security Standard (PCI DSS) was updated with a number of new and modified requirements. Since their last update in 2018, there has been a rapid increase in the use of cloud technologies, contactless payments have become the norm, and the COVID-19 pandemic spurred a massive growth in e-commerce and online payments. At the same time, cybercriminals have adopted increasingly sophisticated methods, capitalizing on global instability to compromise individuals and organizations alike.
These ongoing shifts have made online payments and the digital infrastructure around them an important target, prompting the latest update in PCI DSS requirements. According to the PCI Security Standards Council, the overarching goals of the updates are to continue to meet the security needs of the payment industry, promote security as a continuous and evolving process, add flexibility for different security methodologies, and enhance validation methods.
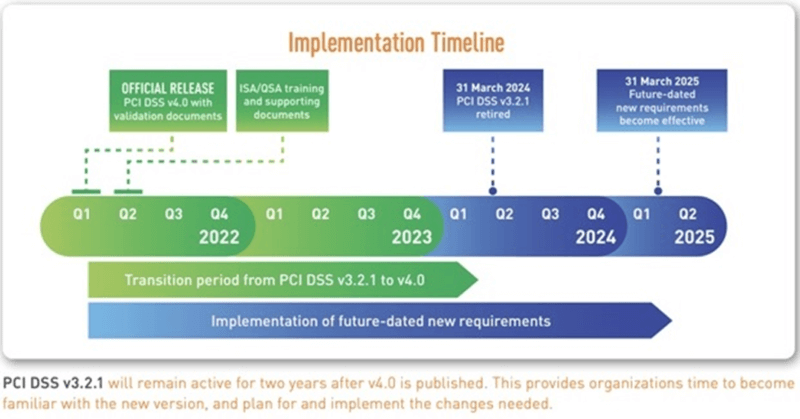
All organizations that process or store cardholder data are now responsible for meeting the new requirements, and they have until March 2024 to do so. And while that may sound like the distant future, making these changes will require significant time and effort. There’s no better time to start than now.
With that in mind, we’ve put together a five-step checklist to help you transition to meet PCI DSS v4.0, and we’ve shared some of the highlights below.
Five Steps to Ensuring Continuous Compliance with PCI DSS
As you get ready to make the transition, it’s important to remember that PCI compliance — both with these new updates and in the future — isn’t a one-time effort. Continuous compliance with any cybersecurity standards is an important part of maintaining a strong security posture, and that requires being aware of new and updated standards, implementing best practices on an ongoing basis, and being thoughtful about how and when these changes are made.
For PCI v4.0 specifically, making the transition efficiently and effectively requires a phased approach that factors in technical and cultural changes. Beyond adjusting the way you do things, you will also need to foster a security mindset within your teams to bring everyone on board with driving compliance. Here’s what that looks like.
Step 1: Plan a Phased Implementation Aligned with the PCI Timeline
To help organizations make the transition to PCI DSS 4.0, the PCI Security Standards Council has shared an implementation timeline that retires the previous version of PCI DSS by March 2024. Beyond that, there are also future-dated requirements that will need to be in place by March 2025.
Start by documenting a phased plan that accounts for the other projects on your team’s plate and gives them enough time to do things properly. This will set you on the path to greater audit success and a stronger security posture.
Step 2: Review Potential Changes to Scope
One of the changes in this new set of requirements is the expansion of Requirement 3, which now includes the protection of account data — not just cardholder data. With a change like this, it will be important to check how it impacts the scope of your compliance operations. You may have to incorporate systems that were previously not in scope, and that could impact your budget in the long run.
Step 3: Conduct a People and Process Evaluation
Building and nurturing a security mindset within your organization is a big part of ensuring continuous compliance. Engage your teams and find ways to frame compliance and security as a core element of their day-to-day work. Explore collaboration opportunities between teams and define processes that ladder up to the goal of strengthening cybersecurity.
Step 4: Strengthen SCM Processes
Another important change in these new updates is that Requirement 2 now broadens the scope of Security Configuration Management (SCM), making organizations responsible for their own security configuration program. Beyond reducing your attack surface, SCM will also help you maintain compliance with other cybersecurity standards, and reduce the time it takes to prepare an audit.
Step 5: Onboard a Tool That Automates Continuous Compliance
Having a solution that continuously monitors for compliance is the easiest way to ensure that your organization remains compliant once you’ve made all the required changes. Under the PCI DSS, compliance is expected to be proven every day, and not having an automated tool can prove expensive and time consuming for your team. Consider a platform that combines SCM with file integrity monitoring (FIM) to abide by PCI DSS v4.0.
How Tripwire Can Help
PCI DSS compliance is the best way to protect payment card data and PCI system integrity, but it shouldn’t be a challenging effort to maintain that compliance. With Tripwire Enterprise, a robust SCM and FIM solution, teams can focus on their core competencies, rather than administrative box-checking.
Specifically, the Tripwire Enterprise Change and Compliance Dashboard alerts you any time there’s an unplanned change to your network that could point to a vulnerability. It also automates compliance evidence, saving you time and effort as you work to prove compliance with PCI DSS v4.0. The dashboards are customizable and provide at-a-glance confirmation of your infrastructure’s change and compliance status, making it a light lift for your team to ensure compliance.
The most recent changes to the PCI DSS reflect important changes to how the world operates. Cybercriminals are more sophisticated than they ever have been, and the proliferation of cloud computing and online payments puts payment card holders at risk. Transitioning to meet these new requirements will be a priority for any organizations that process or store cardholder data — but the journey won’t stop there. The newest PCI DSS requirements emphasize the importance of making security a continuous effort, and that’s a trend that we expect to keep growing.
For more information around each of the five steps towards continuous PCI DSS compliance, read our executive guide.

About the Author: Ali Cameron is a content marketer that specializes in the cybersecurity and B2B SaaS space. Besides writing for Tripwire's State of Security blog, she's also written for brands including Okta, Salesforce, and Microsoft. Taking an unusual route into the world of content, Ali started her career as a management consultant at PwC where she sparked her interest in making complex concepts easy to understand. She blends this interest with a passion for storytelling, a combination that's well suited for writing in the cybersecurity space.
Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor and do not necessarily reflect those of Tripwire, Inc.
Conduct a PCI DSS Self Assessment
The PCI Security Standards Council has developed a Prioritized Approach to compliance to help organizations understand how to reduce risk earlier in their PCI DSS 4.0 compliance journey. The Prioritized Approach includes six milestones and based on this approach, we've created a multiple-choice self assessment questionnaire to help you discover the areas you need to focus the most on your journey to PCI DSS 4.0 compliance.

