
Two significant ransomware attacks occurred in the first half of 2017. The first outbreak took place on May 12, 2017, when WannaCry leveraged a known Windows exploit to infect hundreds of thousands of vulnerable computers around the world, including 34 percent of UK National Health Service (NHS) trusts. Less than two months later, NotPetya abused that same Microsoft vulnerability to strike banks, airports and power companies in Ukraine, Russia and parts of Europe. (Kaspersky Lab says NotPetya is wiper malware, not ransomware, because its encryption algorithm prevents the decryption of infected disks even if victims pay the ransom.) Both WannaCry and NotPetya prove just how far cybercrime has come over the past few decades. Just take a look at WannaCry's ransom note:

As you can see, the message for this threat is a professionally designed dialog box that doesn't just tell users their files are encrypted and that they must pay $300 in Bitcoin to recover their data; it also provides users with the ability to check their payment, as well as to learn more about Bitcoin and how to purchase units of the cryptocurrency. The dialog box even comes with working counters that indicate the time left before attackers raise their ransom amount and permanently delete the decryption key for the affected files. Such a sophisticated ransom note is a far cry from that of the 1989 AIDS Trojan, a threat which many consider to be the first piece of ransomware ever written.
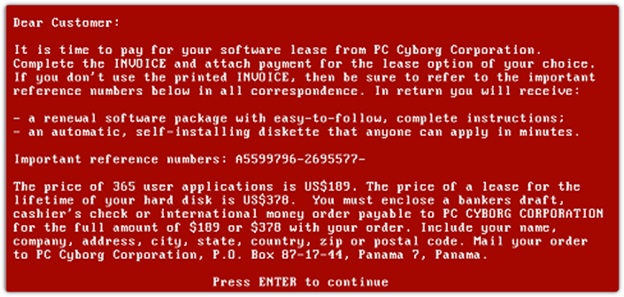
Unlike WannaCry, the AIDS Trojan didn't abuse a Microsoft vulnerability for distribution. Bad actors circulated the threat on infected floppy disks they sent to unsuspecting web users' homes. When someone loaded the disk onto their computers, the malware allowed 90 bootcycles to pass before hiding the directories, encrypting the names of files on the C drive, and demanding the user send a check of $189 to a PO Box in Panama for the PC Cyborg Corporation. Upon receiving payment, those responsible for the malware sent out a tool in the mail that helped affected users decrypt their files, KnowBe4 notes in a blog post. We all know what happened next. Ransomware split off into different directions after the AIDS Trojan. Some malicious developers began creating "scareware," or software which uses fake virus warnings and similar alerts to scare users into purchasing fake or malicious PC protection solutions. Others developed encryption-based threats, or "cryptoware." The field has shifted over the years in tandem with technological innovations and countermeasures employed by the security community to favor different types of malware. Currently, cryptoware is the most popular form among ransomware actors. Ransomware has been around for nearly three decades, and it's safe to assume it could continue to adapt to plague users over the coming years. With that said, it's not only important that users take steps to prevent a ransomware infection. Organizations also need to protect themselves.
What should they do and how can PCI/DSS help?
Ensuring they're compliant with PCI/DSS is a good place to start. Doing so can help organizations identify and strengthen weakened controls and reduce their attack surface. It can also assist companies in implementing security controls such as file integrity monitoring and vulnerability management. Enterprises sometimes struggle to achieve PCI/DSS compliance, however. Time and effort are required to initially reach compliance. Organizations must then attempt to remain compliant and determine if compliance is consistent, all while dealing with tedious audits. They must also make sure they're going beyond compliance to emphasize the security of their systems against threats like crypto-ransomware. Done well, PCI/DSS compliance can protect against ransomware, so it's well worth the investment. In fact, PCI/DSS compliance doesn't even need to be that hard. Tripwire Enterprise can make the process easy and help organizations prevent an infection at the hands of WannaCry or another modern ransomware threat. To discover more about how Tripwire can help, join us for a live webcast to learn how you can secure your environment from ransomware and help you more easily pass your audits—all while staying continuously compliant. Attendees will learn:
- How compliance with PCI DSS 3.2 can protect you from ransomware
- The benefits of Tripwire's managed service solution and continuous PCI compliance
- How change detection can stop suspicious or unauthorized changes before they hold business critical systems hostage
We hope you can join us! Earn a CPE Credit for attending. Register here today!
Insider Insights for the PCI DSS 4.0 Transition
Gain valuable insights from cybersecurity experts on transitioning to PCI DSS 4.0. Tripwire's comprehensive guide provides strategic advice, making the compliance process more streamlined and efficient. Understand the challenges and solutions for meeting PCI DSS requirements with expert guidance.

