
Cisco has patched a remote file overwrite vulnerability in its Integrated Management Controller (IMC) Supervisor and UCS Director products. On Thursday, Cisco issued an advisory that explains how a vulnerability in JavaServer Pages (JSP) input validation routines of both the IMC Supervisor and UCS Director products could be exploited by a remote, unauthenticated attacker to produce system instability or a denial-of-service (DoS) condition.
"The vulnerability is due to incomplete input sanitization on specific JSP pages," reads the advisory. "An attacker could exploit this vulnerability by sending crafted HTTP requests to the affected system. An exploit could allow the attacker to overwrite arbitrary system files resulting in system instability."
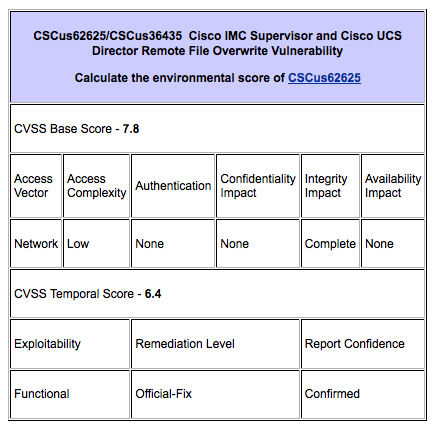
The bug (CVE-2015-6259), which has been documented as CSCus36435 (registered customers only) for the Cisco IMC Supervisor and as CSCus62625 (registered customers only) for the Cisco UCS Director, is said to affect systems running default configurations. It has received a CVSS Base Score of 7.8 due to its network access vector, low level of access complexity, and complete impact on system integrity.
Source: Cisco At this time, there is no evidence that this particular bug has been exploited in the wild. There are also no workarounds for the vulnerability. All Cisco IMC Supervisor versions prior to 1.0.0.1 as well as all Cisco USC Director versions prior to 5.2.0.1 are affected by CVE-2015-6529. Sysadmins are therefore urged to upgrade any systems running IMC Supervisor to 1.0.0.1 and any units running USC Director to either 5.2.0.1 or later or 5.3.0.0 (which contains the fix) or later. News of this patch follows Cisco's patch for a fragmented packet DoS vulnerability in the IOS XE Software for its ASR 1000 Series Aggregation Services Routers back in July. An unauthenticated, remote attacker could exploit this vulnerability by sending a crafted sequence of fragmented IPv4 and IPv6 packets, which would have subsequently caused a DoS condition (or an extended DoS condition if repeatedly exploited).

