On November 3, 2015, ProtonMail, a Switzerland-based encrypted email service, tweeted out that it had been taken offline by a distributed denial-of-service (DDoS) attack. The attack was so massive that it spread to the datacenter where the email service kept its servers, causing several banks and some tech companies to be knocked offline. For days, the attack traffic bombarded ProtonMail. The encrypted email service ultimately decided to pay a US$6000 ransom fee for the attackers to cease their DDoS campaign. But the onslaught didn't end there. A second group operating under the name "Armada Collective" ostensibly renewed the attack against ProtonMail and began targeting a number of other encrypted email services, including Husmail and Neomailbox. These events, not to mention the exploits of DD4BC, demonstrate that bad actors have not lost interest in DDoS attacks. On the contrary, a new report suggests that DDoS campaigns are here to stay. In its Q4 2015 Distributed Denial of Service Trends Report, network infrastructure company Verisign observes that DDoS attacks are increasing in frequency, size, and sophistication.
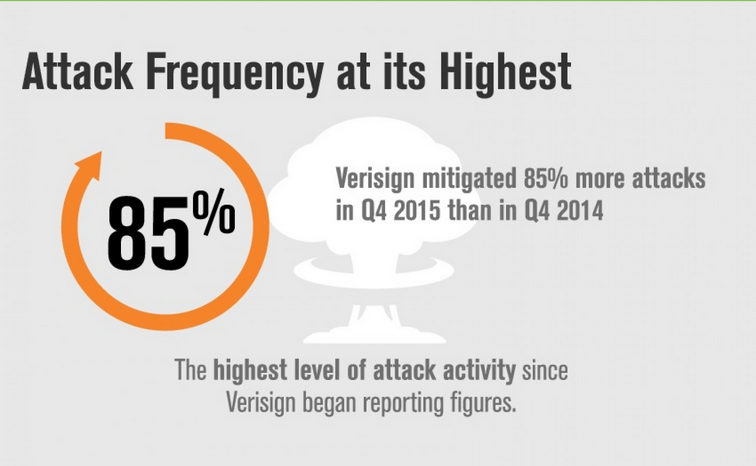
- More Attacks – Last year's fourth quarter saw a 15 percent increase over the the previous quarter and an 85 percent increase over the same time of year in 2014. In total, Q4 2015 registered the highest number of DDoS attacks in the history of Verisign's report.
- Larger Scale – A majority of the attacks (62 percent) observed in last year's fourth quarter peaked over 1 Gbps, with nearly half of those campaigns reaching above 5 Gbps. The average peak size of an attack is now at 6.88 Gbps, which suggests campaigns are growing in magnitude.
- Greater Sophistication – The largest attack in Q4 2015, which peaked at 12 Gbps and 125 Mpps, combined TCP/UDP floods and consisted of small 40 byte packets targeting port 80. This multi-vector campaign also leveraged NTP reflection attack traffic and lasted for several weeks.
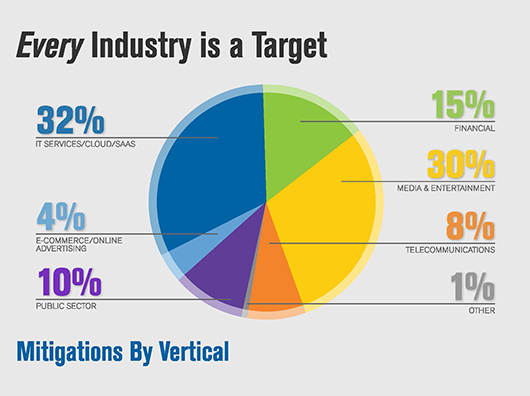
Given these findings, it would appear that no organization is safe anymore from DDoS attacks. Indeed, enterprises in IT Services/Cloud/SaaS and media/entertainment saw the greatest number of attacks at a respective 32 percent (average peak size of 7.3 Gbps) and 30 percent (average peak size of 7.9 Gbps) of the total. Financial and public sector organizations encountered their fair share of attacks, and while businesses in the telecommunications and e-commerce sectors saw only a combined 12 percent of the attacks that occurred in Q4 2015, they saw the highest average peak sizes at over 11 Gbps each.
Organizations were not the only ones singled out, either. Q4 2015 saw a DDoS attack that targeted many of the world's DNS root servers, including the A- and J-roots that Versign manages. Acknowledging their prevalence in today's threat landscape, it is recommended that all organizations invest in solutions that can help mitigate against DDoS attacks. Verisign also emphasizes the need for large-scale DNS infrastructure and for the ability to filter out illegitimate DNS traffic. Title image courtesy of ShutterStock

