
Given the recent high-profile breaches, a key challenge facing government agencies and other security-minded organizations is rooting out malware that has already become embedded on key assets. Multiple vendors are offering cloud-based sandbox analytics services, and/or on-premises appliances, that can analyze new binaries to determine if they have suspicious behavior. These services are aimed at the kind of high-end evasive malware that has avoided detection from the traditional AV solutions. Network vendors have been very active in integrating this capability into their network controls – next generation firewalls and IPS. These are powerful tools. Unfortunately, these systems are primarily looking at traffic over the network. They lack visibility when those binaries have already made it to the high value assets within the network. And, we know there are all sorts of attack vectors into a network that may not be through the common ingress point that the network breach detection appliances are monitoring. How do you find these files when they are already embedded in your environment? Tripwire now offers several important use cases to help our customers address this challenge, ranging from stand-alone one-off situations to fully integrated security automations. From the most basic to the most sophisticated, we can support a number of use cases, including:
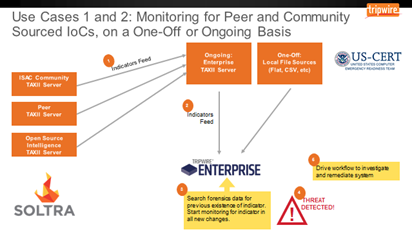
- Import a list of hashes of concern, sourced from other agencies’ experiences or US-CERT, and look for these hashes forensically, as well as in an ongoing manner;
- Incorporate an automated feed of indicators of breach from a TAXII server like those from Soltra, that is receiving indicators from ISACs, peer agencies or other open sources;
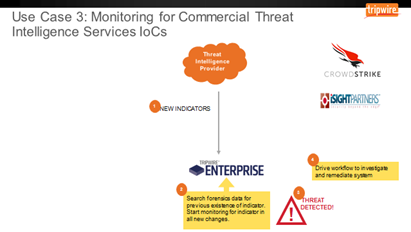
- Incorporate feeds from tailored commercial threat intelligence services, like CrowdStrike or iSight;
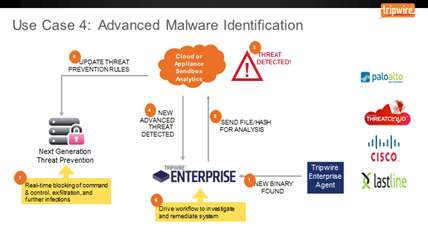
- Dynamically integrate with cloud-based sandbox analytics services (CheckPoint ThreatCloud, Cisco AMP ThreatGrid, Lastline, PaloAlto Wildfire) or an associated on-premise appliance that analyze new binaries for suspicious behavior.
In each of the first three examples, Tripwire gets information about an indicator of compromise (a hash associated with a malicious program, for example). We search both the historical information that we’ve collected over time, as well as looking for these files or other indicators to be added going forward.
The fourth example is based on a slightly different paradigm. It is kicked off when Tripwire finds an unknown executable in the environment, not necessarily identified as an indicator of compromise. In this use case, Tripwire uses an integration to pass a hash to our analytics partner. If they know what it is, they tell Tripwire and we respond accordingly. If not, the partner can detonate the executable in their sandbox and study its behavior. The beauty of this model is that by delivering a new zero-day malware into the cloud service, the cloud will not only identify it as malicious, but will also determine what this binary is attempting to do relative to exfiltrating data, connecting to an external command and control infrastructure, or further infecting systems. The service then translates this behavior into threat prevention rules that are delivered to the network controls. As a result, a customer using this combination can now have real-time protection at the network layer for a new advanced threat that was never even seen on the network – just by its detection by Tripwire and integration with the partner.
The good news? Agencies that are just getting started with a basic list of hashes can rapidly assess their situation. At the same time, knowing that there will be more lists in the future, they understand where the maturity model is going, and can also see a clear pathway to fully automating this activity for the future.

