
If you have ever heard of the Federal Information Security Management Act, then you are aware of the work done by the National Institute of Standards and Technology. The goal of the Act, not to mention the subsequent documents that resulted from strategies designed around implementing it, led NIST to create works designed to bolster security on the information systems operated by the majority of federal agencies. The agencies and the organizations that do business with them are expected to implement the protocols found in these documents within one year of publication. As with any attempt at security in the public sector, updates and revisions are released from time to time. In order to understand the function of NIST 800-53 in terms of information security, it helps to know a little about what it’s designed to do, how it came about and even how to implement the provisions properly.
The Origins
The Federal Information Security Management Act (FISMA) came into being as part of the Electronic Government Act of 2002. The law recognizes the importance of keeping documents and information firmly within the control of the agency that is tasked with using it and ensuring it is only released through channels allowed by current laws. As part of FISMA, the directive was for each agency to develop programs designed to protect data and distribute it in ways that are in compliance with current laws and regulations.
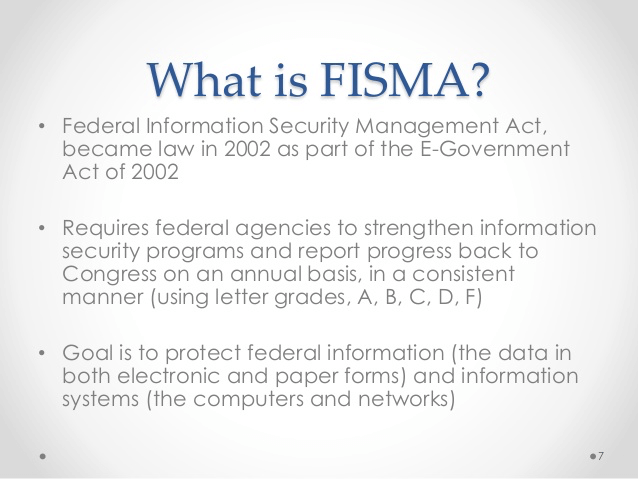
It was within this setting that NIST 800-53 came into being. The document focuses on strategies designed to protect information that is controlled by governmental agencies and ensure that it is properly shielded from hacking attempts and corruption that would lead to widespread abuse of the data as well as to ensure the information remains an asset rather than a liability. Over the years, the 800-53 has undergone revisions. This is necessary as the Internet continues to evolve and more sophisticated threats to cyber-security emerge. The expectation is that the document will continue to be updated when and as the need arises.
What It’s All About
The key provisions found in NIST 800-53 are:
- Control of access to data: Who has it, what it takes to get to it and what is done to revoke access if necessary.
- A plan for recurring audits and full accountability: This includes reviews of how the provisions within the agency are working, any irregularities identified since the last audit and even how the current revisions are working. The audit also seeks to determine the origin of any existing issues and how to go about resolving them.
- Structured training: Ensures agency personnel understand how to operate within the confines of the current recommendations. This includes provisions for remedial training and training for any recently released revisions.
- Configuration and management: All historical as well as recently acquired data. The plan is to ensure data collection is uniform and easy to access by authorized personnel and that the integrity of the data is protected.
- Proper authentication and identification: This includes the creation and issuance of logins and other credentials to authorized personnel. It also includes provisions for revoking credentials and ensuring personnel who no longer require access cannot use their codes to regain access.
- Preparing for contingencies: Ranges from planning related to a temporary shutdown of the system to activating security measures that contain data breaches.
- System maintenance: Routine and regular schedule for maintaining all hardware and software, including regular checks for efficiency and any evidence of attempted breaches.
As an ongoing effort, there have been several revisions of the document. The latest is known as Revision 4.0 which was released in 2014.
Tips to Help With Compliance
Agencies and corporations that seek government issued contracts must comply with the provisions found in NIST 800-53. They have one calendar year from the official release of a revision to bring their operations into full compliance. During that time, there are several key strategies for ensuring they are fully compliant within that time frame.
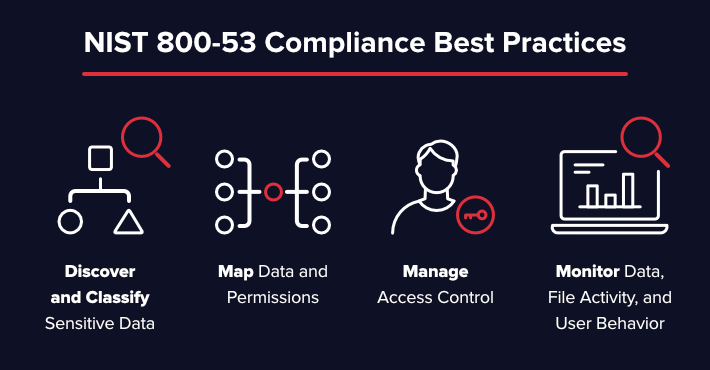
Training is key to compliance. To that end, classes are held to ensure employees and contractors are aware of the changes made in the revisions. Those classes may be held in brick and mortar locations or conducted over secure networks in virtual settings. Relating the revisions as well as the remaining components of the document to the agency function is imperative. The goal here is to analyze and compare agency operation with the security and other protocols found in the document. This provides the basis for determining how to ensure all procedures and safeguards are in line with the current version of the document. Regular assessments of the entire operation are essential. Depending on the agency involved, this could mean a full assessment of the hardware and software used at least annually. It could also mean reviewing the security measures used semi-annually or quarterly in order to determine if they need to be altered or updated in some manner. Having an escalation plan to deal with an attempted data breach (check the most common system vulnerabilities) is a must for compliance. That includes having a detailed schedule of activities designed to shut off access to data, limit who has access until the emergency is resolved and ways to check the data for any attempted corruption.
What Does the Future Hold?
The current version of NIST 800-53 was released in 2014. In 2017, a proposed update known as Revision 5.0 was made available for public viewing. Along with some changes in the text, the revision indicated that the standards found in the document would apply to a wider range of organizations, including federal agencies that were exempt in the past. The final edition of Revision 5.0 is tentatively set for release in March 2019. At that point, federal, non-federal and agencies with government contracts will be expected to review the updates and begin the process of complying with the new standards. Even if your business does not have any contracts with a government entity, monitoring the release and provisions within the latest version of NIST 800-53 would be in your best interest. Doing so will be especially helpful since the new version may help set new standards for private business networks.
About the Author: Sam Bocetta is a freelance journalist specializing in U.S. diplomacy and national security, with emphases on technology trends in cyberwarfare, cyberdefense, and cryptography. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Tripwire Enterprise: Security Configuration Management (SCM) Software
Enhance your organization's cybersecurity with Tripwire Enterprise! Explore our advanced security and compliance management solution now to protect your valuable assets and data.

