
Every year when I go to Black Hat USA and DEFCON, I am reminded of the constant battle between light and dark…wait…that’s Return of the Jedi…. I mean of the constant battle between infosec and the big bad hacker. And it’s not just the uber sophisticated hacks that involve fuzzing and SQL Injections (Am I showing my age there?) or any of the other really cool APT-level stuff. As I walked around the floor at DEFCON, I realized that a huge amount of effort is not just spent in cyberspace but in meat space, as well. There is a very popular part of the Con called Lockpick Village where you can pick up a decent set of lock picks for less than a hundred bucks and sit around with several dozen of your new best friends as you learn how to pick various types of locks.
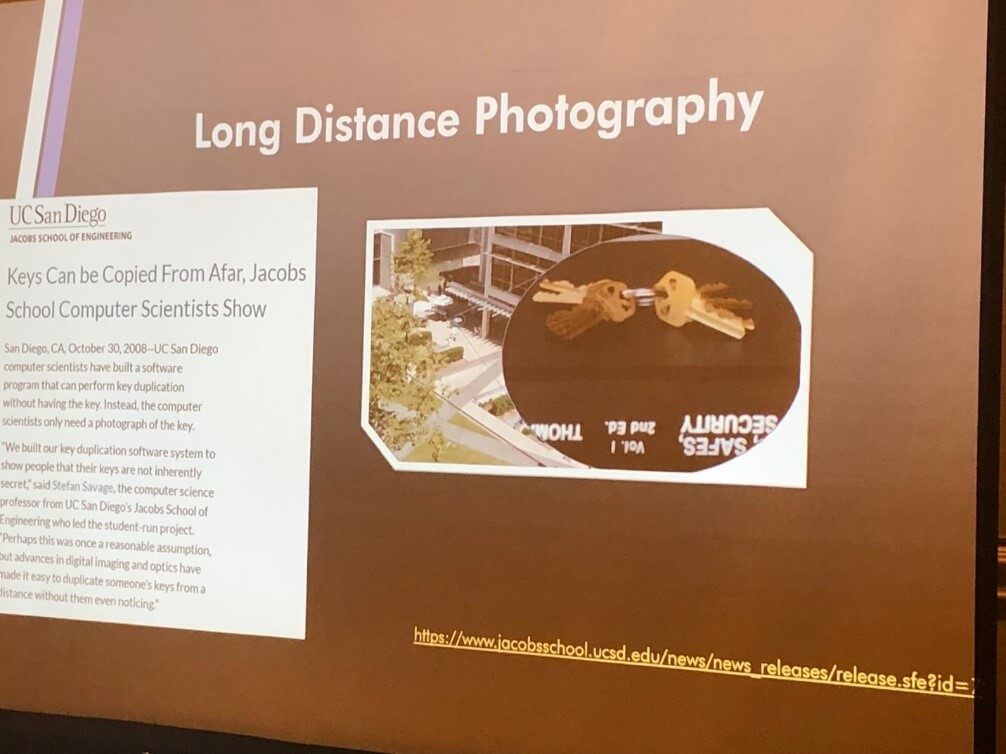
At this year’s Lockpick Village, there was a presenter who even talked about how you can try to duplicate a key from a photograph. The presentation came complete with slides containing images taken of a janitor with a set of keys dangling from his belt.
Another popular spot at DEFCON is Social Engineering Village where people are put into a soundproof booth with a phone and their research as part of a contest. They are given a target to call and try to get as much information as they can, up to and including usernames and passwords. In the vendor hall, you can buy all sorts of tools to help you exploit the masses. Wi-Fi Pineapples that allow you to spoof well known hot spots to try and steal credentials, RFID cloning kits, bump keys…the list goes on and on. Getting back to the realm of cybersecurity, there were areas dedicated to cars, which is always quite popular; an Aviation hacking village; ICS hacking, which had several displays and presentations related to things in meat space you don’t really think about like air conditioning units, lighting and all sorts of stuff that is now interconnected in new and exciting ways. Hell… you can buy ICS hacking kits now. You just buy the tools you need as if you were in a Radio Shack. (Now I am showing my age….)

Working in the industry, I am always talking to folks about the need for various layers of security, but the one area that seems to be neglected the most is the human element. Social engineering is not new. When I first got into the business over 20 years ago, it was in the back of a paper I wrote for my SANS certification. Things have gotten much worse since then. Often the crooks are pretty brazen about it knowing that a pretty fair percentage of the population will fall for their tricks. I mean back in the day, it involved an actual letter from the Nigerian prince. Now you can get several calls per day from someone claiming to be from Windows support or the IRS. You can get dozens of emails per week trying to get you to click on that link. Sometimes, it’s even easier than that. How many of us have lock screen notifications on our phones disabled? I’ll bet quite a few of us don’t. It’s all about the convenience, right? When someone sends us a text or an instant message using corporate applications, we don’t want to have to unlock our phones to read the message to determine its importance. We want it right there where we can glance at it. Well…if we can see it…so can the other guy who is trying to gather intel to determine the next vector to get into your company’s network. It’s not that he will be able to glean your credentials, (Although if he sees that your lock screen code is 123456, that’s on you…) but if he sees that you have an appointment with Bob Smith at 3, he may figure out a way to leverage that against you…or Bob…. The fact of the matter is that the individual layer where people interface with technology often gets neglected in terms of security. Whether these individuals clone your key card (or even your keys), dumpster dive your garbage at home or peek at your phone, we all have to realize that we are often the easiest way into any organization. Why bother with fancy hacks when you can just derive someone’s password or reset hint from the answers by giving a stupid Facebook post that asks what Hogwart’s House would you belong to (Slytherin). Once they have that access, they can begin making their changes and doing their thing. It’s even more pernicious because security teams with all of their fancy toys are often looking for sophisticated hacks and ignoring the bigger threat—one from the inside using credentials that for all intents and purposes belong there. Which is why I am often screaming from the rooftops (OK just blogging but it really isn’t new) that there is a reason why the 80/20 rule is a cliché. The majority of downtime is usually internal in nature. It could be the actual disgruntled or careless employee, or it could be the bad guy who was able to get access by profiling and leveraging said careless employee. At the end of the day, it’s not enough to detect changes. One must also be able to reconcile changes to mitigate this threat.

