
As a security professional, I attend many conferences and networking events. I often overhear people at these events use the following exit line: “It was great meeting you. I’ll be sure to add you on LinkedIn.” Many people use LinkedIn as a virtual business card or an online resume. While LinkedIn is a great networking tool, it can also be used for attack reconnaissance. Providing too much information can give an attacker a running start in their efforts to gather information for an attack against you or your employer.
Research
When targeting a company, an attacker might want to know what antivirus the company is using. The attacker could obtain this information many ways, but the simplest method would be to search LinkedIn. The image below is from an employee who held a recent position with a targeted company.
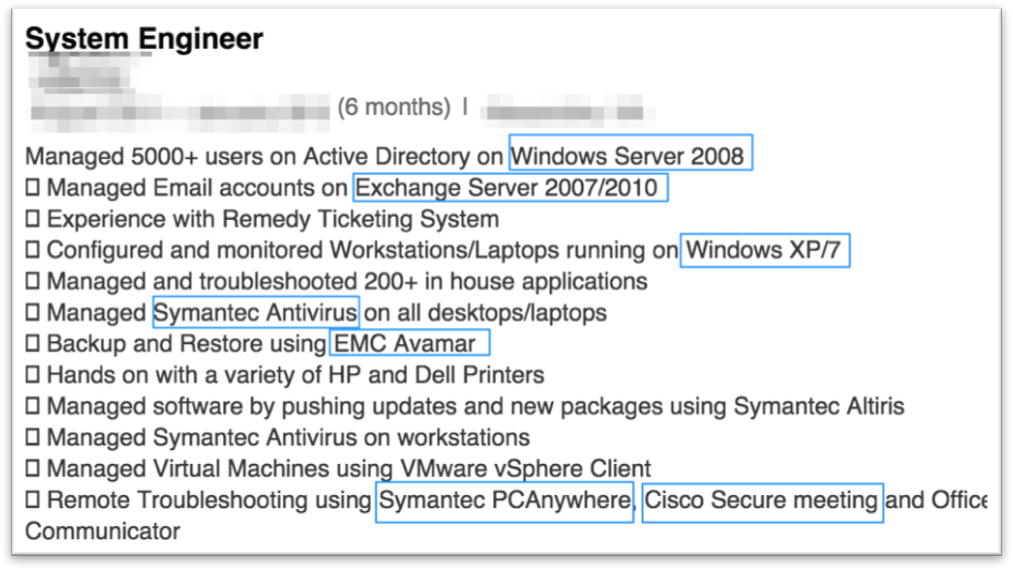
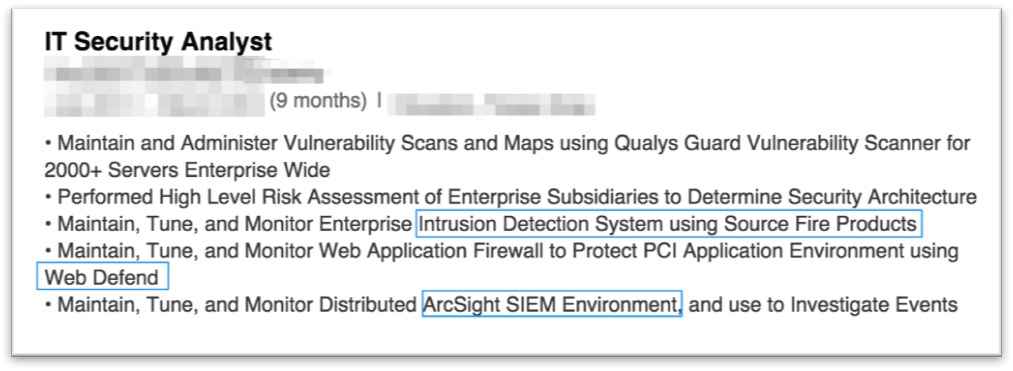
Wow, that’s a lot of information. In addition to the antivirus, vendor the attacker also knows the primary operating systems (including legacy versions) and other programs used throughout the environment. This enables the attacker to gather exploits specific to the target environment then test the exploits to ensure that the antivirus does not detect the activity. It would also be useful for the attacker to understand some of the network-level defenses in place. A quick search provides additional detail on network-based defenses and detection methods.
Once the payload is complete, the attacker must then choose employees to target. In some instances, the attacker may choose to target technical employees due to their elevated privileges on the network. A quick LinkedIn search can provide the attacker with the names of hundreds, perhaps thousands, of employees that hold technical positions at the target company. Using the employee's name to conduct some additional research, it is possible to determine the target’s work email address.
Attack Execution
At this point, the attacker could craft a phishing email to the target in order to launch the payload and compromise their system. This approach has led to many successful red team assessments, but there is another way to achieve the desired result. The attacker could simply create a fake employee LinkedIn profile. This gives the attacker the ability to gain credibility by connecting with legitimate employees. Instead of launching the attack via email, a LinkedIn message could be used. This method of attack, which is one of the most common scams on LinkedIn, eliminates the need for email address spoofing to make the message appear to originate from a coworker, and spam filter evasion. In my experience, target employees are more likely to click a link from a LinkedIn connection when the message is personalized.
Protecting Your Profile
Here are a few tips to help:
- Review your LinkedIn profile for detailed content, and avoid using specific product or vendor names in job descriptions. Instead of listing “Installed Symantec Antivirus” as a bullet, consider “Deployed endpoint protection to 5,000 servers and workstations.”
- Be leery of new connections that immediately endorse your skills, especially if you haven’t worked directly with the connection. Attackers use this tactic to quickly build rapport.
- Use a recent photograph as your profile picture. Having a well-established account with several connections, group memberships, and a photograph makes it more difficult for an attacker to create a fake version of your LinkedIn profile.
- Consider connection requests from fellow alumni carefully. Often, attackers will hone in on key employees interest outside of the workplace in order to make the initial connection.

About the Author: Valerie Thomas is a Principal Information Security Consultant for Securicon LLC that specializes in social engineering and physical penetration testing. After obtaining her bachelor’s degree in Electronic Engineering, Valerie led information security assessments for the Defense Information Systems Agency (DISA) before joining private industry. Valerie is the coauthor of “Building an Information Security Awareness Program: Defending Against Social Engineering and Technical Threats” with Bill Gardner. Throughout her career, Valerie has conducted penetration tests, vulnerability assessments, compliance audits, and technical security training for executives, developers, and other security professionals. Editor’s Note: The opinions expressed in this and other guest author articles are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc. Title image courtesy of ShutterStock
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

