Like storytelling, data visualization can be used to provide a narrative about your organization’s cybersecurity posture. Cybersecurity is never a single thing; it is an amalgamation of an often growing list of issues that never seem to end. So in order to make some sense of what it means for the health of your organization, I am combining several metrics to define a singular one—cybersecurity posture—in a visual manner.
Telling Your Cybersecurity Posture Story
So what is cybersecurity posture and how does an analytics and reporting platform like Tripwire Connect help you tell that story? I am sure you have heard the adage that a picture is worth a thousand words. Just the same, a cybersecurity metric is worth not only a thousand but several thousand vulnerabilities, unauthorized changes or compliance findings. The security health of any organization is represented by not one but several variables defined by the organization in order of risk priority. In other words, your task is protecting what is important first and safeguarding it. In most cases, organizations look for vulnerabilities, changes to their configuration and adherence to certain compliance-related policies as key metrics to define their risk profile.
3 Types of Cybersecurity Posture
Taking these three factors (vulnerability, compliance and change) as the most important aspects of your enterprise’s security health, your overall cybersecurity posture reflects how well you fare when measuring these metrics Individually and together. In order to understand each of them, you have to go through a lot of data, reports and analysis.
- Vulnerability posture: Vulnerabilities by assets
- Compliance posture: Assets out of compliance
- Change posture: Files/documents that have changed
Questions Your Trend Data Should Answer
Tripwire Connect takes the data from your security configuration (SCM), file integrity monitoring (FIM) and vulnerability management (VM) installations and creates visual representations that give you instant insights on how you are doing.
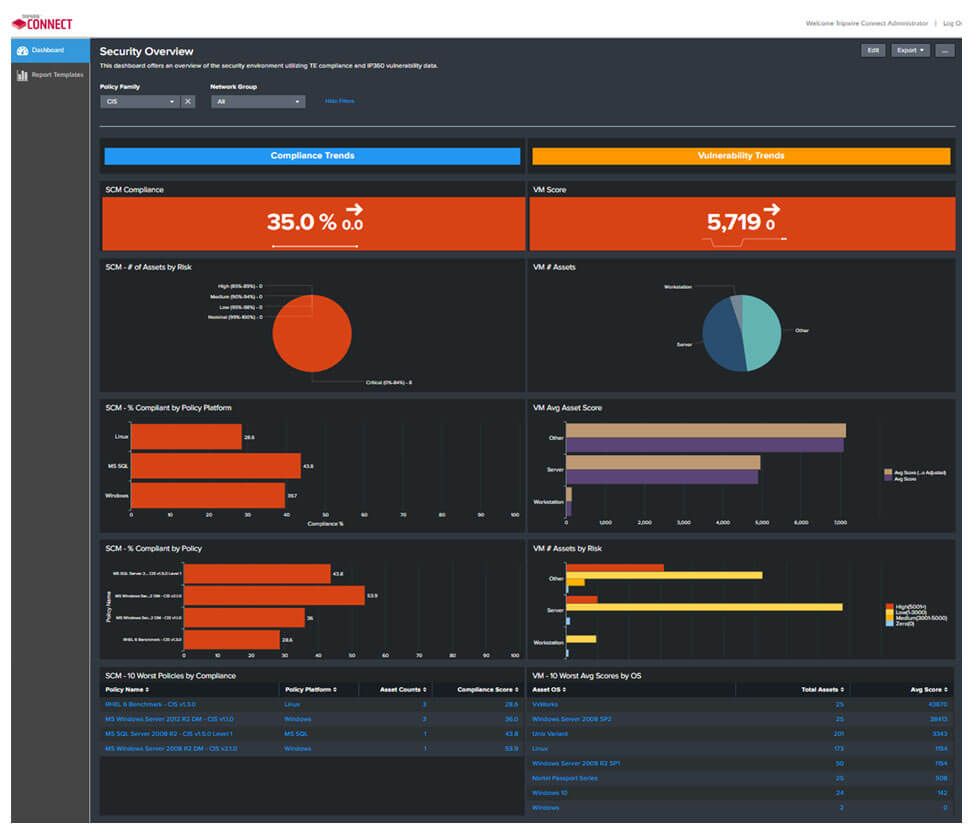
The visuals tell the user a cybersecurity story that allows them to focus their attention on what matters most. Examples of such visuals are historical trend data for each of the three types of cybersecurity postures listed above, incremental change, degree of variation and so on. These types of trend data help you answer the following key questions:
- What is my cybersecurity posture at any given point of the day?
- How is my cybersecurity posture changing over time?
- What are the most critical risks to prioritize and focus on now?
- Is the behavior normal or is it an anomaly?
- Are there any patterns associated with any vulnerability?
What Powerful Cybersecurity Visibility Looks Like
Not all visuals are created equal, and not all visuals tell a story. Creating the right cybersecurity metrics visuals is an art form and doing it right requires deep cybersecurity, statistics and computer science expertise. A great storytelling visual needs to encompass the following four things:
- A dashboard that provides a quick overview
- Filters that allow for further granularity and relevant information
- Ability to zoom on the relevant information to provide details as needed
- Linking all the different variables together via common cybersecurity thread
By having a powerful visualization tool, you can evaluate all the changes occurring in your environment simultaneously. In addition to making it easy to interpret complex data, visualization also helps you be more productive by addressing what matters most first. Whether you are a CISO or a security analyst, Tripwire Connect is designed to empower you with visuals that help you make the decisions that ultimately improve your cybersecurity posture.

