
An ongoing phishing campaign code-named "Bad Tidings" has been targeting several Kingdom of Saudi Arabia government agencies for years. Researchers at Anomali Labs first detected the Bad Tidings campaign back in November 2016. Since then, the operation has targeted four government agencies in Saudi Arabia: the Ministry of Labor and Social Development, the Ministry of Foreign Affairs, the Saudi Government and the Ministry of Interior (Absher). Since making their discovery, Anomali Labs' researchers have also spotted a single occurrence in which the attack scheme targeted the Saudi British Bank. The campaign has thus far used a total of 95 unique phishing hostnames to target the entities listed above. To make these fraudulent domains appear legitimate, the attackers have employed various spoofing techniques such as Punycode, typosquatting and subdomain spoofing on their creations. Such crafty disguises laid the groundwork for he bad actors to build two web pages for each site, one being a replica of the targeted entity's homepage and the second being a fake login page. Anomali Labs' analysis revealed that more than half (56.84 percent) of phishing sites have so far targeted Absher. In one sample detected by the security firm on 4 March 2019, for instance, the attackers leveraged typoquatting and subdomain spoofing to lure users into visiting hxxp://www[.]moi[.]gov[.]sa[.]abshr[.]club. A close analysis by researchers revealed that the site employed an additional tactic designed to trick users into thinking they were on the actual Absher site. As they explain in a blog post:
To make the faux login page appear even more authentic, users have to complete a Captcha, which is a common challenge-response system designed to differentiate humans from robots or automated software tools that site owners use to prevent brute-force attacks. Once the user has entered their account credentials, they are redirected back to the fraudulent MOI homepage.
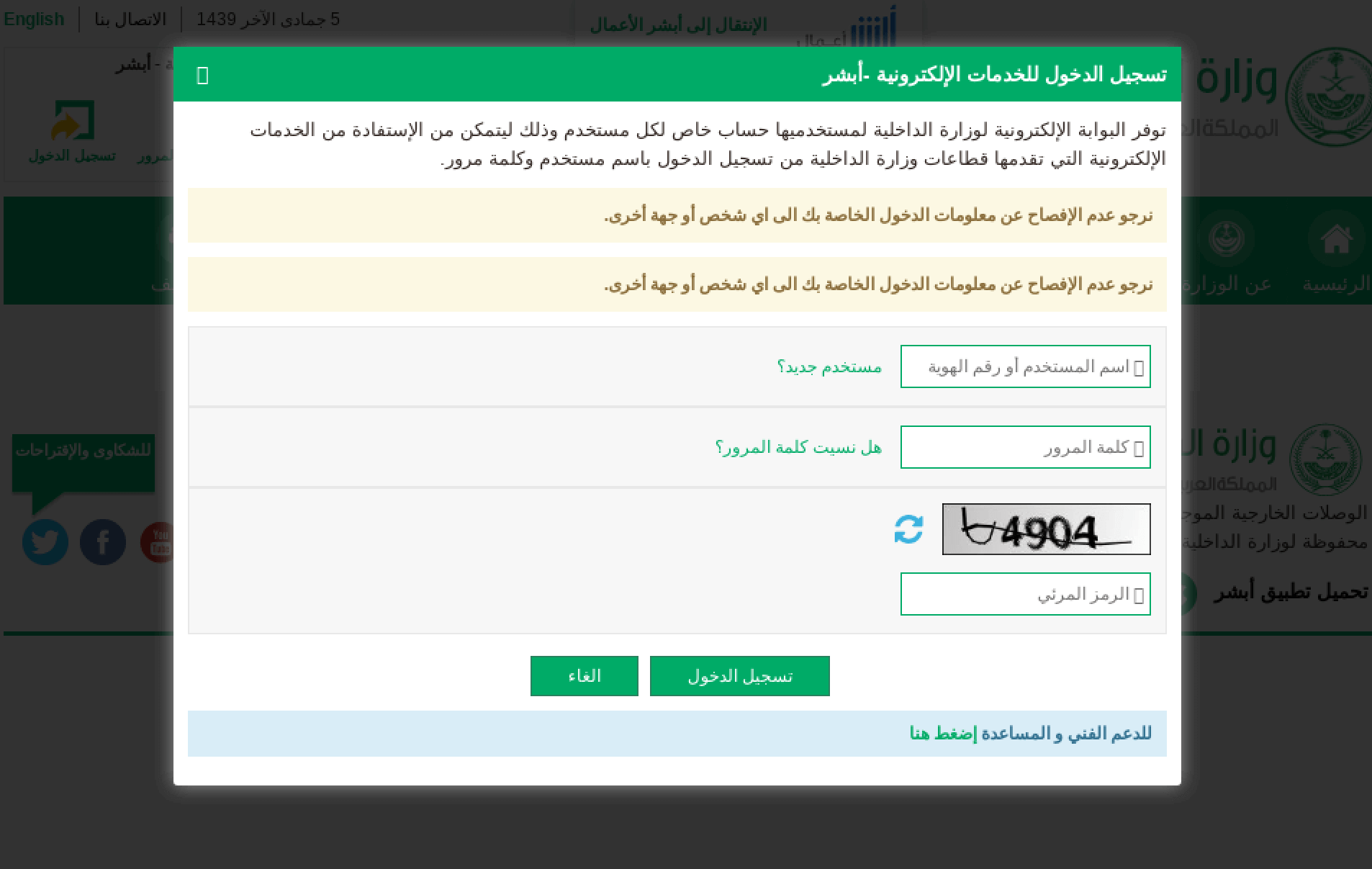
Faux account login page for MOI e-Services Absher portal. (Source: Anomali Labs) Prior to publishing its research, Anomali Labs and the Saudi Telecom Company (STC) began coordinating with the National Cybersecurity Agency (NCA) and the Saudi CERT in an effort to address the security concerns associated with this campaign. It also submitted its findings to Google Safe Browsing and Microsoft Defender Security Intelligence so that these two entities can help block the fraudulent sites. Organizations can protect themselves against these types of attacks by registering their trademark, proactively registering variants of their domain (if possible), investing in a domain monitoring and early takedown service as well as implementing MFA for their login processes. At the same time, users should use their familiarity of the most common types of phishing attacks to report any fraudulent websites to the appropriate authorities.

