
As humans and as users, we make mistakes. Sometimes we forget to implement that software patch until a week or two after its release. Other times, we decide to click on an enticing pop-up. Those types of actions can degrade our computer's speed and security. It's, therefore, our responsibility to adjust our behavior accordingly and protect ourselves. Unfortunately, that's not always feasible or effective. Think about it. We can develop a patching strategy that fits our lifestyle and computing habits. We can even train ourselves to watch out for online scams. But there are some threats against which it is almost impossible for users to defend on their own. Take typosquatting, for instance. Typosquatting is a practice by which actors create domains that users could input into the address bar if they accidentally type the wrong URL of a web service. They might not mean to type "netflix.om" instead of "netflix.com." Like all of us, they're in a hurry, and they want to find the content that matters to them. A typo is an easy enough mistake for users to make. But it does have consequences. Indeed, attackers can register malicious look-alike domains to infect sloppy spellers. They can also use Punycode to trick users into visiting a malicious website as part of a scam. Let's look at two such typosquatting examples with respect to google.com: ɢoogle.com and Ǥooǥɩe.com.
Example 1: ɢoogle.com
At the beginning of November 2016, the Analytics Edge team heard about a "Vote for Trump" message that spammers had left in many people's analytics reports. The message contained a link to secret.ɢoogle.com.
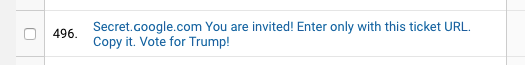
The link might look like it's legitimate. But ɢoogle.com isn't the same as Google.com. That's because the small upper-case "G" is a Latin Letter Small Capital, or Unicode 0262. ɢoogle.com, therefore ,doesn't direct users to google.com. It directs them to the following destination:
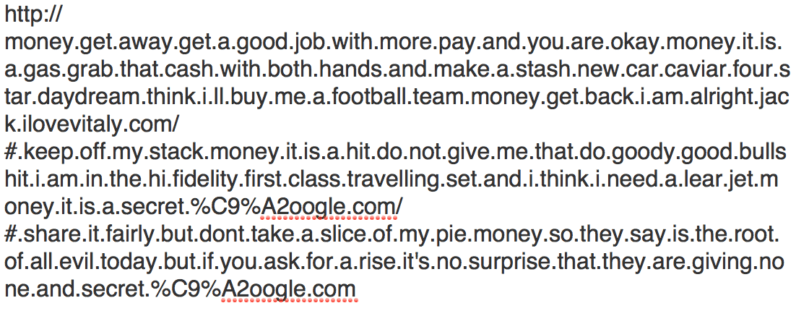
Yeah, plenty to be suspicious about with that URL. The Analytics Edge team agrees:
"Well, someone, somewhere, gave out the domain ɢoogle.com to someone who was not representing google.com. what is stopping them from mimicking YOUR web site, or YOUR BANK’s website, and then leaving innocent-looking links for you to fall prey to? You would probably never realize what you did until it was too late."
All that risk from changing a single character. But attackers don't stop there. Some make even more minute alterations to fool users. Let's move on to our next example.
Example 2: Ǥooǥɩe.com
To evaluate the threat posed by typosquatting, Richard de Vere, Director of The AntiSocial Engineer, attempted to register the Punycode version of Google.com. He wasn't successful. But using a method he refuses to disclose, he succeeded in registering a close variation in the form of xn--ooe-2fbc60f.com:
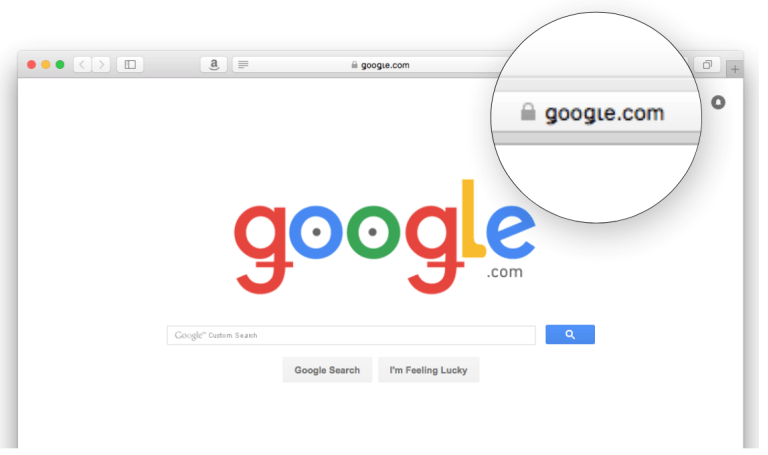
Source: TheAntiSocialEngineer.com, permission given The researcher can't overstate the threat those test results pose to users everywhere:
"Tricking people to click on a link is wearing thin on the internet, users get savvier by the day so those with malicious intent are constantly looking for new ways to trick us. We’ve seen it with typo domains for years. A lower case ‘L‘ can look almost identical to a uppercase ‘i‘ and this abuse is common place now. The problem is with nearly all devices fully supporting ASCII Punycode characters translations you have an odd situation where it’s almost too easy to register these domains and trick people. If you think you’re on the legitimate domain and you are not, the chance of something bad happening rises."
Phishing for credentials… a malware infection… all of it's possible via malicious typosquatting.
What to Do About It
Given the threats posed by typosquatting, what can we as users do to protect ourselves? The answer is not much… that is, aside from educating ourselves about what to look for. For instance, if we come across a link, we need to stop ourselves from clicking on it immediately. Instead, we need to hover over it and look for any red flags in the actual URL. Does it use any number substitution, like "0" for "o," where it shouldn't? Does it omit periods where there should be some? Does it use a plural or hyphenated version of a domain that's singular or non-hyphenated, or vice versa? All of those are signs of a potentially malicious website for which we need to look out. At the same time, websites with the means to do so (especially the big ones like Google) should buy up those domain versions that users might accidentally spell out in the address bar or that attackers could trick people into visiting. Doing so will prevent attackers from registering those domains first, which will help to protect users in the long run.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

