
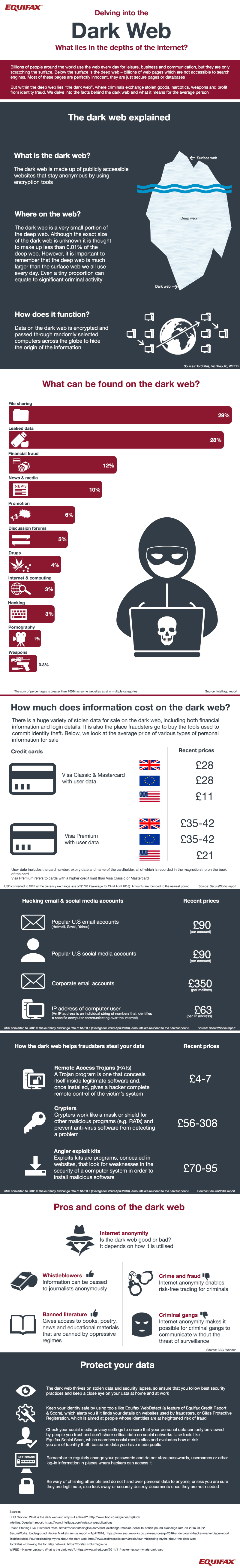
Large hacks and cyber-attacks aimed at exploiting information, affecting everyone from major company databases to politician’s email accounts, have now become a common occurrence in our ever-connected world. This hacked information – and the act of accessing it – has rapidly become a sought-after product and service on dark web marketplaces. Coupled with the measures that cyber criminals take to stay anonymous through sophisticated tools and crafty research, the dark web is the ideal place for them to conduct business. Equifax has analysed and compiled research from 2016 highlighting what is available on the dark web and at what price. According to the research, the most popular types of websites on the dark web are, unsurprisingly, those that deal in file sharing (29 percent) and leaked data (28 percent). With a huge choice of data for sale, financial information and login details are available at shockingly low prices.
Information and tool prices
Credit card details (with user data) from major companies, such as Visa and MasterCard, can be purchased for $35, with Premium accounts (higher credit limits) increasing to between $44 - $53. Email logins from a main provider, such as Gmail, Hotmail, or Yahoo, can be acquired for $113; social media login details are priced the same. Login details for a corporate email account are priced higher at around $440 due to the increased security that often surrounds them. An IP address can also be found and bought for just under $80. Many of the tools that hackers use to source this information are usually bought anonymously on the dark web too. Remote Access Trojans (RATs) – programs that hide within valid software that give a hacker control over a user’s system – can be bought cheaply at as low as $5. A Crypter that prevents anti-viruses from working properly or masks malicious programs, such as RATs, range up to $385 in price but start at $70.
Data protection
Dark web marketplaces thrive on lack of security; even the simplest of informational slip ups can be exploited. For example, using the same password for a range of accounts is a risky practice as once discovered, all accounts linked to that particular email or username can be accessed. It’s also important to check privacy settings for social media accounts. Details such as birthdays and pet/parent names, often used as answers for security questions, can be learned and combined with data acquired from breaches for easy access. Exploiting offline information in conjunction with data acquired online is a very possible concern, too. In the Werner Herzog documentary Lo and Behold, renowned hacker Kevin Mitnick details how he was able to sweet talk Motorola employees over the phone into giving him the remaining details he needed to access their data records. This shows just how vital it is to be aware of who is handling sensitive data.
Is the Dark Web all bad?
Whilst the dark web has gained a reputation as a gathering place for all types of criminals, the anonymity that users have can be used for good, too. Whistle-blowers use it to avoid risk when passing on sensitive information to journalists, and activists have been known to organise groups and protests through it. People who live under oppressive or strict regimes are also able to gain access to banned or censored materials, as well as being able to express themselves without the fear of being persecuted. Digital Shadows, a UK-based firm that has developed a dark web search engine called SearchLight, says:
"The dark web is probably a good thing, especially with those people that aren't happy with the ISPs (Internet Service Providers) blocking domains from them. If users want to go on a website that's now blocked, they could access those same websites by going through the Tor network."
Conclusion
It’s clear that the dark web won’t be going anywhere – at least not for the foreseeable future. Although there are recent reports of mass website takedowns, it will continue to be used by all types of criminals for business. The average internet user must learn to stay vigilant and be aware of where their sensitive information is stored, both online and offline. The chance of exploitation is greater than ever before, and proper responsibility in regards to data must be taken in order to stay safe. The age old saying, ‘Knowledge is power’ has never been so relevant.

About the Author: Jon Harris is a freelance writer from London, England. He writes about a variety of topics but is passionate about the deep/dark web, data security, and Arsenal football club. Jon is a graduate of Brunel University. Editor’s Note: The opinions expressed in this guest author article are solely those of the contributor, and do not necessarily reflect those of Tripwire, Inc.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

