
Phishing scams are a persistent threat to users' inboxes. But that's not all they target. Fraudsters have other ways of delivering their ploys to unsuspecting users. One of the more common techniques is known as smishing. It's when a scammer sends a phishing ploy containing a suspicious link via SMS text message to a user's phone. Despite this change in medium, smishers use the same social engineering tactics employed by inbox phishers. For instance, to elevate users' trust in a ruse, smishers commonly reference the post office in their messages. Attackers know people are more inclined to click on something if it mentions an institution they trust. It worked for phishers who targeted Scandinavian users on two separate instances back in 2015, so nothing prevents it from working for smishers. Let's look at how one smishing campaign is leveraging the post to trick users into clicking an attack link.
You've Got Malware!
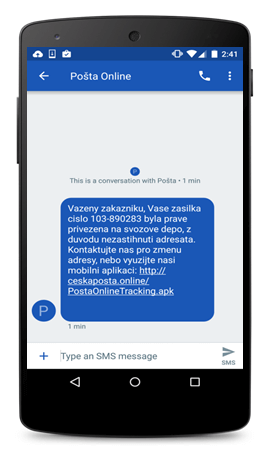
The attack begins when a user receives a text message from Czech Post, the Czech postal service. The message comes with a link that claims to let users track a package. But that's not what it does at all. Something malicious awaits the user on the other end of the link. As Check Point's Threat Research Team explains in a blog post:
"Once users click the link, they are led to a fake Czech Post web page with a seemingly legitimate address. From there the malware downloads and installs immediately on the mobile device. Since users need to approve the installation of apps from sources other than Google Play, the attackers use social engineering tactics convincing them to do so."
Every instance of the malware documented thus far assumes the icon of the Czech Post's official app. Not all samples use the postal service's name, however. Some come with the name "Flash Player 10 Update," a discrepancy which should raise red flags in every mobile user's mind. When the user tries to open the app, the icon disappears from the home screen. But by no means has the malware uninstalled itself. It simply waits for the user to open any app. At that point, it prompts the user to submit their credit card details and other sensitive financial information so that it can steal their money. Towards this end, the malware takes a page from MazarBOT and Android.He.He by intercepting SMS messages. This capability allows the malware to break into a user's banking account even if they have two-step verification (2SV) enabled. That's not all this trojan can do, either. Check Point's researchers elaborate:
"The malware communicates with its Command and Control server (C&C) which is capable of sending a wide variety of commands. The malware can send SMS messages to a user’s contacts or to a specific number which to help spread the malware. The malware can also lock the user’s device and display a ransom message to extort money from the user in return for his control of the device."
You can watch a demo of the malware in action below. https://www.youtube.com/watch?v=7v9f51tKDQc
Common Sense Goes a Long Way
Phishers employ every platform to steal users' sensitive information. With that said, mobile users should protect themselves against smishing campaigns by avoiding suspicious SMS text messages and by downloading apps only from official app marketplaces. They should also install an anti-virus solution onto their devices. To learn more about how you can protect yourself against phishing attacks, click here.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

