There are numerous ways to redirect a user to an exploit kit. Some of these methods are quite sophisticated. Take pseudo-Darkleech, for instance. This attack campaign injects malicious code into WordPress core files. That code creates a malicious iframe that redirects the user to a landing page for an exploit kit. In so doing, the campaign builds off Darkleech, malware which began targeting vulnerable Apache servers with malicious web modules back in 2012.
EITest: A History of Exploit Kit Activity
Another attack campaign known as EITest uses an infection sequence that's like that of pseudo-Darkleech. Since at least 2014, it's been exposing visitors to websites injected with malicious script. The code generates an HTTP request for and redirects a user to an exploit kit landing page, where the software package scans the computer for known vulnerabilities and sends over relevant exploit code. If it succeeds in abusing an open security hole, the exploit kit sends a payload for ransomware, an information stealer, or other malware and executes it in the background. Before they know it, the user has suffered a malware infection.
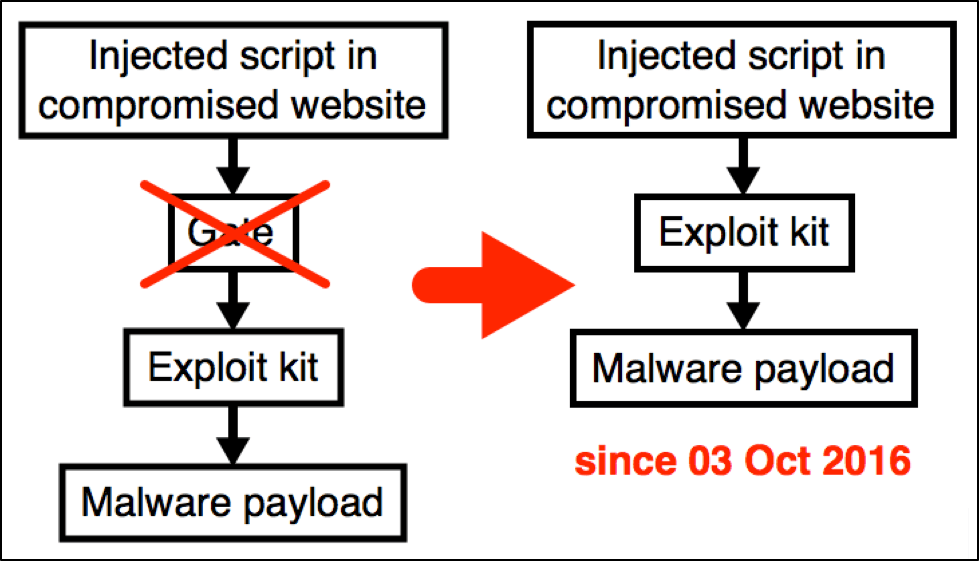
Traditional EITest infection chain (Source: Palo Alto Networks) EITest originally used a gate between a compromised website and an exploit kit landing page. But the infection campaign did away with that feature in October 2016, likely because many in the security community used this tactic to block it. It now directly links compromised websites to an exploit kit. Today, EITest is still alive and well. Its handlers are selling traffic to several groups that operate exploit kits, with the RIG-E "Empire" EK group as one of its biggest buyers. This threat actor purchases attack traffic from EITest, turns around, and then sells it to even smaller threat actors. Even so, actors are seeing a drop-off in conversions (i.e. malware installations) from exploit kits. Those who purchase EITest traffic are therefore coming up with new strategies to infect unsuspecting users. The security community has detected one such innovation: the use of social engineering to target Google Chrome users.
Font Not Found? Not Really. It's Ad Fraud Malware
In December 2016, Proofpoint researchers came across a website compromised by EITest that's dropping an executable called "Chrome_Font.exe." The infection chain is quite simple. If a visitor meets certain criteria--uses Chrome on Windows, originates from a target country, and meets the proper referrer--EITest makes the page unreadable. This tactic serves as a social engineering lure to trick the user into installing a fake update. If a visitor doesn't meet that criteria, they experience a more traditional exploit kit attack Just how does the attack campaign render the compromised website's pages unreadable? Proofpoint explains in a blog post:
"The pages are rendered unreadable by storing all the data between HTML tags in an array and iterating over them to replace them with “�”, which is not a proper ISO character; as a result, the replacement character � [9] will be displayed instead."
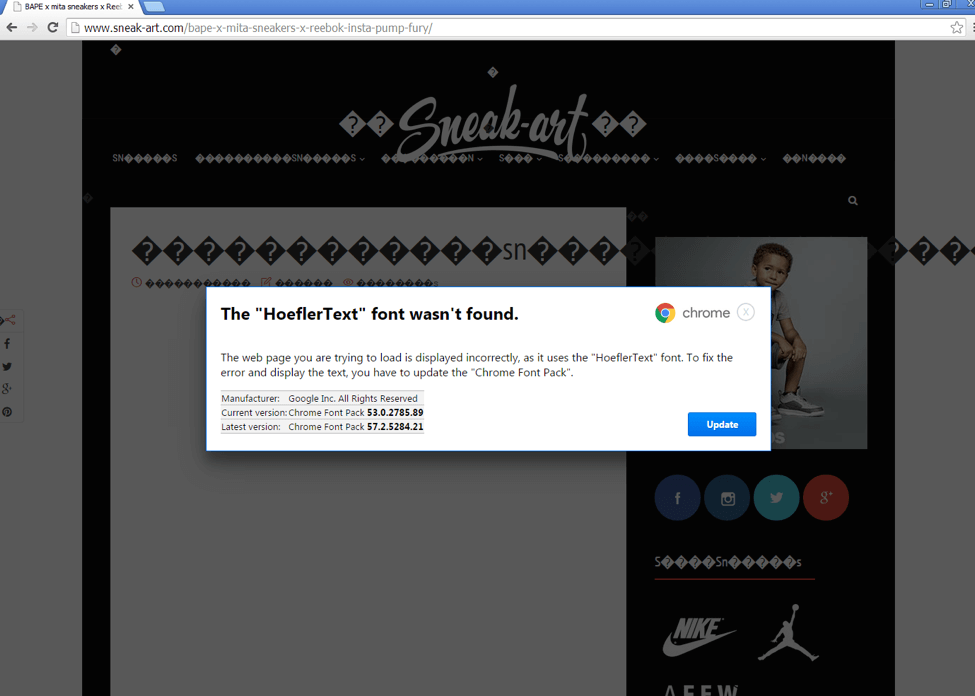
Social engineering EITest lure (Source: Proofpoint) Once the campaign scrambles the page, it displays a prompt to the user telling them that the browser can't find Hoefler Text, an old-style serif font which American typeface designer Jonathan Hoefler created in the 1990s. It tells the user to click on an "Update" button to fix the issue. Of course, pursuing that "solution" does no such thing. Instead it prompts Chrome to download "Chrome_Font.exe." This executable is a disguise for Fleercivet, a type of ad fraud malware which accepts affiliates on the dark web.
Conclusion
Bad actors are always looking for new ways to infect users with malicious software. That's especially true for criminals who have purchased traffic from campaigns like EITest. If these nefarious individuals aren't giving up, neither should you. Make sure you never install anything on your computer by impulse. That includes "updates" that suspicious websites prompt you to load. For added protection, maintain an anti-virus solution on your computer and patch your software as soon as an update becomes available.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

