
Last week, we reported on a post office email scam that was recently observed to be targeting PostNord customers with Cryptolocker2 ransomware. Our story noted that customers commonly fall for this type of scam because, by nature, they tend to trust institutions with which they are familiar. As a result, users were more than willing to click on a URL to arrange a pick-up time for an undelivered package from the local postal service, especially around the holidays. It would appear that attackers are once again exploiting this trust, albeit with a different institution as bait. Security firm Heimdal Security has spotted a spam campaign that is leveraging fake emails from the Internal Revenue Service (IRS) to drop two payloads onto victims' computers: Kovter ransomware and CoreBot malware. According to a blog post written by Andra Zaharia of Heimdal, each fake email takes on the following format: From: [spoofed / fake return address] Subject Line: Payment for tax refund # 00 [6 random numbers] Attached: Tax_Refund_00654767.zip -> Tax_Refund_00654767.doc.js
"If an unsuspecting user opens the attachment – and ignores several warnings – then the code will run on the machine with the privileges of the logged in user," explains Zaharia. "If you’re using your admin account on a daily basis, this may prompt you to reconsider."
The Javascript, known as "Nemucod" or "Swabfex", ultimately loads up the first payload: Kovter. Back in January of this year, researchers at Cyphort Labs observed that both the Neutrino and Sweet Orange exploit kits were targeting visitors to The Huffington Post's website with Kovter ransomware as part of a malvertising campaign. Since then, Kovter has incorporated some of the tactics employed by Trojan.Poweliks that in part allow the malware to persist in an infected computer's registry. These adaptations, among other things, have shifted Kovter in the direction of stealthier campaigns, including click-fraud activities, and away from something as blunt as ransomware. However, its authors can use the malware to hold victims' computers for ransom whenever they choose.
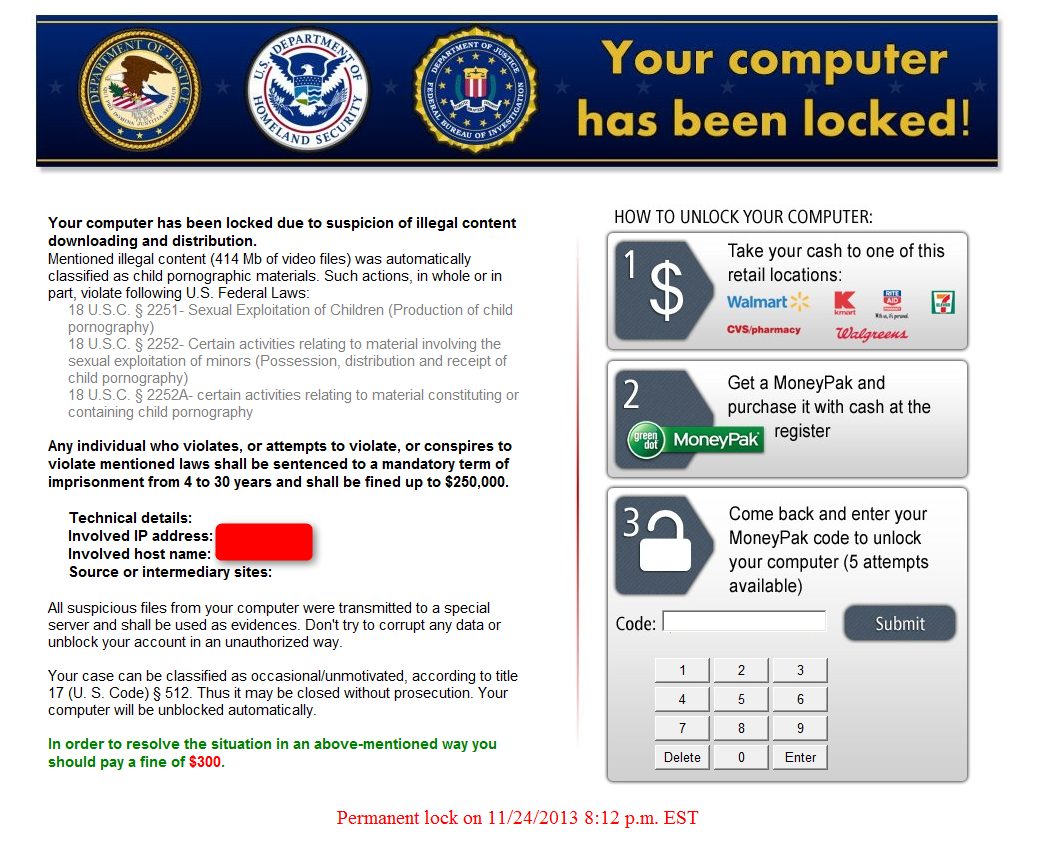
Case in point, Heimdal notes in the IRS spam campaign that Kovter connects to three domains: "http:// ahmadhania [.]com", "http:// hkcpafirm [.] com", and "http:// martenmini [.] com". From those locations, the malware retrieves a Win32PE masquerading as a ".gif" file. It then uses a "sleep mode" function built into mshta.exe to encrypt all data files found on the computer and available network drives. Finally, all of this data is harvested and sent to the attackers via a C&C server. The spam campaign is nearly complete. All that remains are the finishing touches added by CoreBot. Originally detected by IBM X-Force researchers back in August of this year, CoreBot is a modular malware that can be easily updated by attackers via a plugin system. This design makes CoreBot an adaptable threat capable of stealing passwords, grabbing forms, hooking into web browsers, harvesting credentials and performing man-in-the-middle (MiTM) attacks. It can also work in tandem with other forms of malware. Once Kovter successfully encrypts a victim's data, CoreBot in the spam campaign observed by Heimdal forces a system shutdown, which completes the ransomware payload and saves it in obfuscated form to the registry. A system restart activates the payload, at which point in time the user is alerted to the fact that all of their information has been encrypted and that they must pay a ransom in Bitcoin to regain access. As of this writing, not one of the three Kovter domains identified above scored a detection rate of more than 4/66 on VirustTotal. That makes this spam campaign particularly dangerous. Users are therefore urged to avoid clicking on suspicious links in emails, to verify the senders of important electronic documents, and to keep a regular backup of their data. For information on how to protect against ransomware, please click here. Title image courtesy of ShutterStock

