
Against many experts' advice, we as users tend to overshare information about ourselves on social media. Doing so makes the job of a bad actor so much easier. Depending on the content of the shared details, an actor can leverage the information to commit identity theft. Alternatively, they can abuse it to conduct targeted phishing campaigns known as spear-phishing (or whaling) attacks against their targets. Spear-phishing and whaling are together one of the top five most common scams found on popular social networking sites, especially on LinkedIn. With that in mind, it's not surprising attackers have developed a new phishing scam on the social media platform to steal members' sensitive personal information and payment card details. Let's look at how the new scam works.
Five Strikes, and You're a Phish!
Phishers generally deliver the new scam to a target's LinkedIn inbox in the form of an email. Here's what the email says:
Subject line: LinkedIn is requesting files from you From: "LinkedIn Messages" < [email protected] > Date: 4 November 2016 Hi [name], Thank you for being our valued customer. Your account has been selected by our verification office as a precautionary measure to defend you. Upload a viewable, scanned copy of the payment method account holder’s government-issued photo identification, such as a driver’s license or passport. Upon receipt and verification, we will notate your account that the necessary documentation to substantiate your account has been received. We thank you in advance for your cooperation and apologize for any inconvenience this may cause. The image must be a color scan that shows your photo and required data clearly. https: //www.dropbox[.]com/request[/]4o80dqbZ0Wf4[sanitized] This link will expire in 24 hours, so be sure to use it right away. Thank you for using LinkedIn! The LinkedIn Team
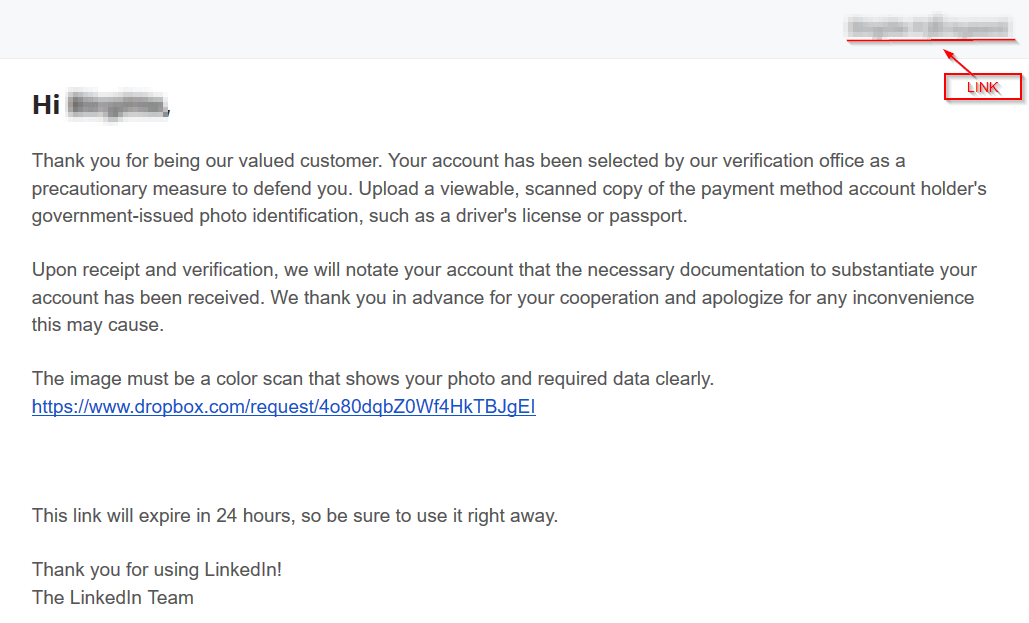
Source: Heimdal Security This email should raise at least five red flags for the educated user. First, starting at the top, the message originates from the email postmaster@fnotify[dot]com. That address doesn't have anything to do with LinkedIn. Otherwise, it would have linkedin.com as its domain. Curious, researchers at Heimdal Security looked at fnotify.com to find out more about the domain. They discovered something interesting. Heimdal security evangelist Andra Zaharia explains:
"Upon verification, we found that http : [//]fnotify.com/ is an empty WordPress website that belongs to a Finnish citizen, which was most likely compromised to be used in this phishing campaign."
Second, the message claims LinkedIn's team wants to verify the target's account "as a precautionary measure to defend [them]." Fine, but against what? Any legitimate company would go into more detail about the reasons why they're taking this step. In the very least, they would identify the threat to which they're responding. Another red flag is the fact that the message mentions a "payment method." Unless you have a LinkedIn Premium account, you have no reason to give your payment details to LinkedIn. And you should never give your account credentials to ANYONE via email no matter who they purport themselves to be. The fourth red flag is the fact that LinkedIn directs you to a Dropbox page where you can upload your documents. If this message actually originated from LinkedIn, the message would come with a unique service designed and hosted by the social networking site. It would not link to a free page provided by third-party software.
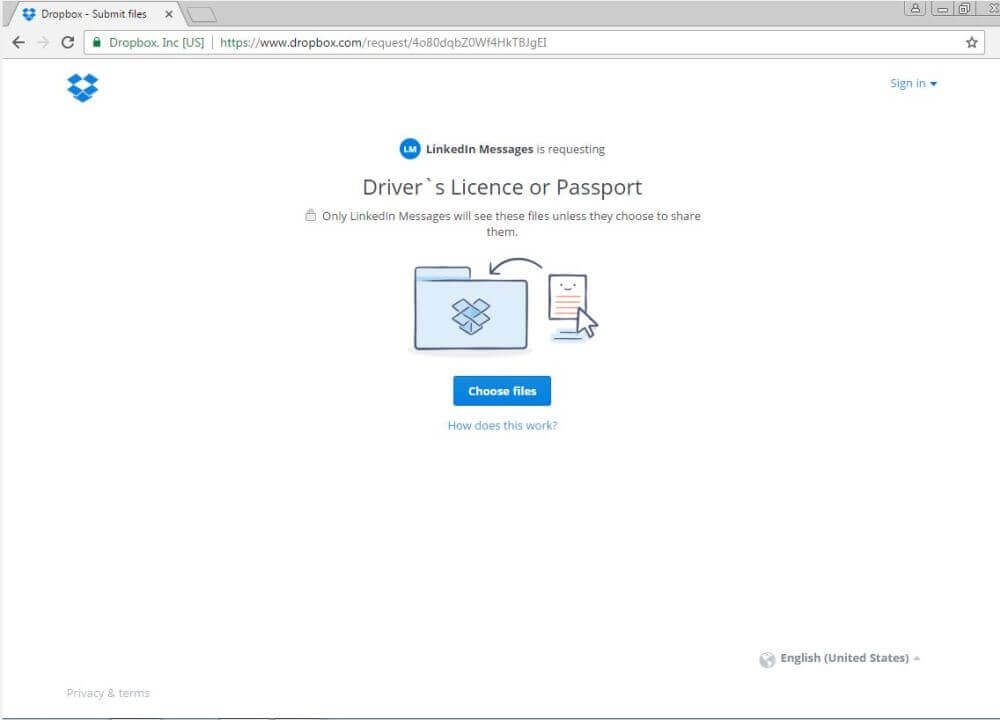
Source: Heimdal Security Finally, the email says the link will expire in 24 hours, which implies the fact that LinkedIn will delete your account unless you comply as quickly as possible. Time limits and threats are the hallmarks of a phishing scam. A legitimate web service like LinkedIn would never resort to those kinds of tactics.
Conclusion
As the scam above demonstrates, computer criminals are always attempting to con unsuspecting users into handing over their personal information and payment card details. They might try to disguise their emails in certain ways to make them appear legitimate. But unless they hack the web service directly, there's already something that gives away what's really going on. With that in mind, it's important that users make an effort to familiarize themselves with some of the most common scams they find on social media. They can start by looking at ruses that frequent LinkedIn, Twitter and Facebook.
Meet Fortra™ Your Cybersecurity Ally™
Fortra is creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable solutions. Learn more about how Fortra’s portfolio of solutions can benefit your business.

